Computer worm: Difference between revisions
m Reverted edits by 163.6.207.155 (talk) to last revision by Rhododendrites (HG) |
|||
| Line 17: | Line 17: | ||
Worms spread by exploiting vulnerabilities in operating systems.<!-- NOTE: this statement is erroneous. a Trojan horse is a category similar to a [[master status]]. Any program can be a Trojan horse~> If user interaction is required for the malware to spread, it is called a [[Trojan horse (computing)|Trojan horse]]. |
Worms spread by exploiting vulnerabilities in operating systems.<!-- NOTE: this statement is erroneous. a Trojan horse is a category similar to a [[master status]]. Any program can be a Trojan horse~> If user interaction is required for the malware to spread, it is called a [[Trojan horse (computing)|Trojan horse]]. |
||
--> |
--> |
||
Vendors with security problems supply regular security updates<ref>{{cite web|url=http://www.ubuntu.com/usn |title=USN list |publisher=Ubuntu |date= |accessdate=2012-06-10}}</ref> (see "[[Patch |
Vendors with security problems supply regular security updates<ref>{{cite web|url=http://www.ubuntu.com/usn |title=USN list |publisher=Ubuntu |date= |accessdate=2012-06-10}}</ref> (see "[[Patch Thursday]]"), and if these are installed to a machine then the majority of worms are unable to spread to it. If a vulnerability is disclosed before the security patch released by the vendor, a [[zero-day attack]] is possible. |
||
Users need to be wary of opening unexpected email,<ref>{{cite web|url=http://www.microsoft.com/technet/security/alerts/info/nimda.mspx |title=Information on the Nimda Worm |publisher=Microsoft.com |date= |accessdate=2012-06-10}}</ref> and should not run attached files or programs, or visit web sites that are linked to such emails. However, as with the [[ILOVEYOU]] worm, and with the increased growth and efficiency of [[phishing]] attacks, it remains possible to trick the end-user into running malicious code. |
Users need to be wary of opening unexpected email,<ref>{{cite web|url=http://www.microsoft.com/technet/security/alerts/info/nimda.mspx |title=Information on the Nimda Worm |publisher=Microsoft.com |date= |accessdate=2012-06-10}}</ref> and should not run attached files or programs, or visit web sites that are linked to such emails. However, as with the [[ILOVEYOU]] worm, and with the increased growth and efficiency of [[phishing]] attacks, it remains possible to trick the end-user into running malicious code. |
||
Revision as of 15:47, 12 February 2014

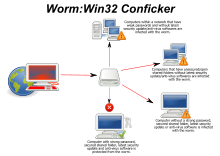
A computer worm is a standalone malware computer program that replicates itself in order to spread to other computers.[1] Often, it uses a computer network to spread itself, relying on security failures on the target computer to access it. Unlike a computer virus, it does not need to attach itself to an existing program.[2] Worms almost always cause at least some harm to the network, even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer.
Many worms that have been created are designed only to spread, and do not attempt to change the systems they pass through. However, as the Morris worm and Mydoom showed, even these "payload free" worms can cause major disruption by increasing network traffic and other unintended effects. A "payload" is code in the worm designed to do more than spread the worm—it might delete files on a host system (e.g., the ExploreZip worm), encrypt files in a cryptoviral extortion attack, or send documents via e-mail. A very common payload for worms is to install a backdoor in the infected computer to allow the creation of a "zombie" computer under control of the worm author. Networks of such machines are often referred to as botnets and are very commonly used by spam senders for sending junk email or to cloak their website's address.[3] Spammers are therefore thought to be a source of funding for the creation of such worms,[4][5] and the worm writers have been caught selling lists of IP addresses of infected machines.[6] Others try to blackmail companies with threatened DoS attacks.[7]
Backdoors can be exploited by other malware, including worms. Examples include Doomjuice, which can spread using the backdoor opened by Mydoom, and at least one instance of malware taking advantage of the rootkit and backdoor installed by the Sony/BMG DRM software utilized by millions of music CDs prior to late 2005.[8] [dubious ]
Worms with good intent
Beginning with the very first research into worms at Xerox PARC, there have been attempts to create useful worms. Those worms allowed testing by John Shoch and Jon Hupp of the Ethernet principles on their network of Xerox Alto computers. The Nachi family of worms tried to download and install patches from Microsoft's website to fix vulnerabilities in the host system—by exploiting those same vulnerabilities.[9] In practice, although this may have made these systems more secure, it generated considerable network traffic, rebooted the machine in the course of patching it, and did its work without the consent of the computer's owner or user. Regardless of their payload or their writers' intentions, most security experts regard all worms as malware.
Several worms, like XSS worms, have been written to research how worms spread. For example, the effects of changes in social activity or user behavior. One study proposed what seems to be the first computer worm that operates on the second layer of the OSI model (Data link Layer), it utilizes topology information such as Content-addressable memory (CAM) tables and Spanning Tree information stored in switches to propagate and probe for vulnerable nodes until the enterprise network is covered.[10]
Protecting against dangerous computer worms
Worms spread by exploiting vulnerabilities in operating systems. Vendors with security problems supply regular security updates[11] (see "Patch Thursday"), and if these are installed to a machine then the majority of worms are unable to spread to it. If a vulnerability is disclosed before the security patch released by the vendor, a zero-day attack is possible.
Users need to be wary of opening unexpected email,[12] and should not run attached files or programs, or visit web sites that are linked to such emails. However, as with the ILOVEYOU worm, and with the increased growth and efficiency of phishing attacks, it remains possible to trick the end-user into running malicious code.
Anti-virus and anti-spyware software are helpful, but must be kept up-to-date with new pattern files at least every few days. The use of a firewall is also recommended.
In the April–June, 2008, issue of IEEE Transactions on Dependable and Secure Computing, computer scientists describe a potential new way to combat internet worms. The researchers discovered how to contain the kind of worm that scans the Internet randomly, looking for vulnerable hosts to infect. They found that the key is for software to monitor the number of scans that machines on a network sends out. When a machine starts sending out too many scans, it is a sign that it has been infected, allowing administrators to take it off line and check it for malware.[13][14] In addition, machine learning techniques can be used to detect new worms, by analyzing the behavior of the suspected computer.[15]
Mitigation techniques
- ACLs in routers and switches
- Packet-filters
- TCP Wrapper/libwrap enabled network service daemons
- Nullrouting
History
The actual term "worm" was first used in John Brunner's 1975 novel, The Shockwave Rider. In that novel, Nichlas Haflinger designs and sets off a data-gathering worm in an act of revenge against the powerful men who run a national electronic information web that induces mass conformity. "You have the biggest-ever worm loose in the net, and it automatically sabotages any attempt to monitor it... There's never been a worm with that tough a head or that long a tail!"[16]
On November 2, 1988, Robert Tappan Morris, a Cornell University computer science graduate student, unleashed what became known as the Morris worm, disrupting a large number of computers then on the Internet, guessed at the time to be one tenth of all those connected[17] During the Morris appeal process, the U.S. Court of Appeals estimated the cost of removing the virus from each installation was in the range of $200–53,000, and prompting the formation of the CERT Coordination Center[18] and Phage mailing list.[19] Morris himself became the first person tried and convicted under the 1986 Computer Fraud and Abuse Act.[20]
See also
- Computer and network surveillance
- Computer virus
- Helpful worm
- Spam
- Timeline of notable computer viruses and worms
- Trojan horse (computing)
- XSS Worm
References
- ^ Barwise, Mike. "What is an internet worm?". BBC. Retrieved 9 September 2010.
- ^ "Difference between a computer virus and a computer worm". USCB SicienceLine.
- ^ Ray, Tiernan (February 18, 2004). "Business & Technology: E-mail viruses blamed as spam rises sharply". The Seattle Times.
- ^ McWilliams, Brian (October 9, 2003). "Cloaking Device Made for Spammers". Wired.
- ^ "Unavailable".
- ^ "Uncovered: Trojans as Spam Robots". hiese online. 2004-02-21. Archived from the original on 2009-05-28. Retrieved 2012-11-02.
- ^ "Hacker threats to bookies probed". BBC News. February 23, 2004.
- ^ "Sony Ships Sneaky DRM Software". Pcworld.com. 2005-11-01. Retrieved 2012-06-10.
- ^ "Virus alert about the Nachi worm". Microsoft.
- ^ Al-Salloum, Z.; et al. (2010). "Iscc 2010". IEEE.
{{cite journal}}:|contribution=ignored (help); Cite journal requires|journal=(help); Explicit use of et al. in:|last2=(help) - ^ "USN list". Ubuntu. Retrieved 2012-06-10.
- ^ "Information on the Nimda Worm". Microsoft.com. Retrieved 2012-06-10.
- ^ Sellke, S. H.; Shroff, N. B.; Bagchi, S. (2008). "Modeling and Automated Containment of Worms". IEEE Transactions on Dependable and Secure Computing. 5 (2): 71–86.
- ^ "A New Way to Protect Computer Networks from Internet Worms". Newswise. Retrieved July 5, 2011.
- ^ Moskovitch R., Elovici Y., Rokach L. (2008), Detection of unknown computer worms based on behavioral classification of the host, Computational Statistics and Data Analysis, 52(9):4544–4566, DOI 10.1016/j.csda.2008.01.028
- ^ Brunner, John (1975). The Shockwave Rider. New York: Ballantine Books. ISBN 0-06-010559-3.
- ^ "The Submarine".
- ^ "Security of the Internet". CERT/CC.
- ^ "Phage mailing list". securitydigest.org.
- ^ Dressler, J. (2007). "United States v. Morris". Cases and Materials on Criminal Law. St. Paul, MN: Thomson/West. ISBN 978-0-314-17719-3.
External links
- Malware Guide – Guide for understanding, removing and preventing worm infections on Vernalex.com.
- "The 'Worm' Programs – Early Experience with a Distributed Computation", John Shoch and Jon Hupp, Communications of the ACM, Volume 25 Issue 3 (March 1982), pages 172-180.
- "The Case for Using Layered Defenses to Stop Worms", Unclassified report from the U.S. National Security Agency (NSA), 18 June 2004.
- Worm Evolution, paper by Jago Maniscalchi on Digital Threat, 31 May 2009.
