Search results
Appearance
The page "Operations Security Protected Information" does not exist. You can create a draft and submit it for review or request that a redirect be created, but consider checking the search results below to see whether the topic is already covered.
- An information security operations center (ISOC or SOC) is a facility where enterprise information systems (web sites, applications, databases, data centers...9 KB (1,098 words) - 18:32, 8 February 2024
- Information security, sometimes shortened to infosec, is the practice of protecting information by mitigating information risks. It is part of information...191 KB (22,122 words) - 03:18, 17 June 2024
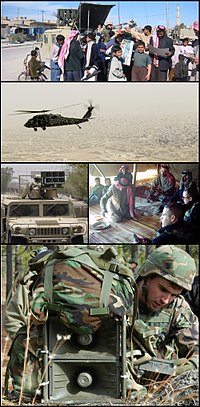
- (EW), computer network operations (CNO), psychological operations (PSYOP), military deception (MILDEC), and operations security (OPSEC), in concert with...69 KB (7,814 words) - 06:44, 21 May 2024
- A security operations center (SOC) is responsible for protecting an organization against cyber threats. SOC analysts perform round-the-clock monitoring...3 KB (395 words) - 19:48, 22 August 2023
- Information risk management Information security and information assurance Information security operations center (ISOC) Information technology controls for...10 KB (1,157 words) - 13:10, 18 February 2024
- An information security audit is an audit of the level of information security in an organization. It is an independent review and examination of system...31 KB (4,029 words) - 09:48, 21 June 2023
- or other authenticating information that allows them access to information and programs within their authority. Network security covers a variety of computer...11 KB (1,264 words) - 08:58, 20 March 2024
- Classified information is material that a government body deems to be sensitive information that must be protected. Access is restricted by law or regulation...72 KB (5,969 words) - 09:49, 21 May 2024
- Information security standards or cyber security standards are techniques generally outlined in published materials that attempt to protect the cyber...23 KB (2,598 words) - 11:34, 20 May 2024
- combine security information management (SIM) and security event management (SEM). SIEM is the core component of any typical Security Operations Center...35 KB (4,095 words) - 05:10, 18 April 2024
- Computer security, cybersecurity, digital security, or information technology security (IT security) is the protection of computer systems and networks...218 KB (22,132 words) - 21:53, 16 June 2024
- agency-wide program to provide information security for the information and information systems that support the operations and assets of the agency, including...22 KB (2,209 words) - 13:35, 2 November 2023
- computing. It is a sub-domain of computer security, network security, and, more broadly, information security. Cloud computing and storage provide users...53 KB (6,675 words) - 14:12, 15 June 2024
- Bureau of Diplomatic Security, its primary mission is to provide security to protect diplomatic assets, personnel, and information, and combat visa and...73 KB (8,361 words) - 03:00, 1 June 2024
- Internet security is a branch of computer security. It encompasses the Internet, browser security, web site security, and network security as it applies...24 KB (2,588 words) - 10:56, 17 June 2024
- The Organization for Security and Co-operation in Europe (OSCE) is a regional security-oriented intergovernmental organization comprising member states...121 KB (8,679 words) - 14:04, 4 June 2024
- Obscurity in the context of security engineering is the notion that information can be protected, to a certain extent, when it is difficult to access or comprehend...14 KB (1,399 words) - 14:58, 6 June 2024
- anti-terrorism, border security, immigration and customs, cyber security, and disaster prevention and management. It began operations on March 1, 2003, after...75 KB (7,200 words) - 01:37, 9 June 2024
- Control Measures (ACCM) – Security measures used to safeguard classified intelligence or operations and support information when normal measures are insufficient...15 KB (1,684 words) - 14:25, 7 May 2024
- Psychological operations (PSYOP) are operations to convey selected information and indicators to audiences to influence their motives and objective reasoning...81 KB (9,947 words) - 22:12, 15 June 2024
- Memorandum National security presidential memorandum 7: Integration, Sharing, and Use of National Security Threat Actor Information to Protect Americans Memorandum
- United Nations (redirect from UN Security Council)maintaining international peace and security, promoting human rights, fostering social and economic development, protecting the environment, and providing
- Information security means protecting information (data) and information systems from unauthorized access, use, disclosure, disruption, modification, or