Search results
Appearance
- In computer architecture, 32-bit computing refers to computer systems with a processor, memory, and other major system components that operate on data...11 KB (1,366 words) - 01:07, 9 June 2024
- In computer architecture, 8-bit integers or other data units are those that are 8 bits wide (1 octet). Also, 8-bit central processing unit (CPU) and arithmetic...11 KB (1,110 words) - 14:30, 24 June 2024
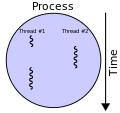
- In computer architecture, multithreading is the ability of a central processing unit (CPU) (or a single core in a multi-core processor) to provide multiple...12 KB (1,463 words) - 01:17, 19 June 2024
- In systems engineering and software engineering, requirements analysis focuses on the tasks that determine the needs or conditions to meet the new or altered...25 KB (2,899 words) - 08:49, 18 April 2024
- Copy protection, also known as content protection, copy prevention and copy restriction, is any measure to enforce copyright by preventing the reproduction...52 KB (6,402 words) - 01:42, 1 July 2024
- A terminal emulator, or terminal application, is a computer program that emulates a video terminal within some other display architecture. Though typically...15 KB (1,891 words) - 13:33, 29 June 2024
- DriveSpace (initially known as DoubleSpace) is a disk compression utility supplied with MS-DOS starting from version 6.0 in 1993 and ending in 2000 with...18 KB (2,076 words) - 22:21, 30 March 2024
- The instruction cycle (also known as the fetch–decode–execute cycle, or simply the fetch-execute cycle) is the cycle that the central processing unit (CPU)...9 KB (1,182 words) - 18:33, 26 June 2024
- In computer architecture, 24-bit integers, memory addresses, or other data units are those that are 24 bits (3 octets) wide. Also, 24-bit central processing...4 KB (513 words) - 07:42, 17 May 2024
- In the seven-layer OSI model of computer networking, the session layer is layer 5. The session layer provides the mechanism for opening, closing and managing...7 KB (975 words) - 23:34, 3 April 2024
- Morpheus was a file sharing and searching peer-to-peer client for Microsoft Windows, developed and distributed by the company StreamCast, that originally...4 KB (340 words) - 05:51, 6 June 2024
- Electronic data processing (EDP) or business information processing can refer to the use of automated methods to process commercial data. Typically, this...12 KB (1,377 words) - 13:33, 5 May 2024
- Yaffs (Yet Another Flash File System) is a file system designed and written by Charles Manning for the company Aleph One. Yaffs1 was the first version...8 KB (1,078 words) - 20:53, 18 March 2024
- A terminate-and-stay-resident program (commonly TSR) is a computer program running under DOS that uses a system call to return control to DOS as though...13 KB (1,787 words) - 18:58, 18 June 2024
- The UNI/O bus /ˌjuːniˈoʊ/ is an asynchronous serial bus created by Microchip Technology for low speed communication in embedded systems. The bus uses a...11 KB (1,403 words) - 08:51, 18 May 2024
- Network delay is a design and performance characteristic of a telecommunications network. It specifies the latency for a bit of data to travel across the...2 KB (248 words) - 14:10, 19 June 2023
- In computer architecture, 36-bit integers, memory addresses, or other data units are those that are 36 bits (six six-bit characters) wide. Also, 36-bit...7 KB (996 words) - 05:13, 5 February 2024
- An XOR linked list is a type of data structure used in computer programming. It takes advantage of the bitwise XOR operation to decrease storage requirements...8 KB (1,232 words) - 17:47, 26 May 2024
- Windows Genuine Advantage (WGA) was an anti-infringement system created by Microsoft used to validate the licences of several Microsoft Windows operating...30 KB (2,958 words) - 00:50, 23 May 2024
- In computational complexity theory, DSPACE or SPACE is the computational resource describing the resource of memory space for a deterministic Turing machine...7 KB (1,047 words) - 07:21, 26 April 2023