Search results
- Extensible HyperText Markup Language (XHTML) is part of the family of XML markup languages which mirrors or extends versions of the widely used HyperText...59 KB (6,926 words) - 15:02, 6 April 2024
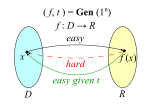
 In theoretical computer science and cryptography, a trapdoor function is a function that is easy to compute in one direction, yet difficult to compute...9 KB (1,316 words) - 09:51, 25 February 2024
In theoretical computer science and cryptography, a trapdoor function is a function that is easy to compute in one direction, yet difficult to compute...9 KB (1,316 words) - 09:51, 25 February 2024- Gnutella is a peer-to-peer network protocol. Founded in 2000, it was the first decentralized peer-to-peer network of its kind, leading to other, later...41 KB (3,845 words) - 04:48, 9 April 2024
- Microchip Technology Incorporated is a publicly listed American corporation that manufactures microcontroller, mixed-signal, analog, and Flash-IP integrated...51 KB (4,469 words) - 08:15, 21 April 2024
- Keychain is the password management system in macOS, developed by Apple. It was introduced with Mac OS 8.6, and has been included in all subsequent versions...11 KB (1,168 words) - 06:10, 27 April 2024
- Pivot Animator (formerly Pivot Stickfigure Animator and usually shortened to Pivot) is a freeware application that allows users to create stick-figure...6 KB (662 words) - 07:30, 18 April 2024
 An optical head-mounted display (OHMD) is a wearable device that has the capability of reflecting projected images as well as allowing the user to see...13 KB (1,194 words) - 05:42, 6 April 2024
An optical head-mounted display (OHMD) is a wearable device that has the capability of reflecting projected images as well as allowing the user to see...13 KB (1,194 words) - 05:42, 6 April 2024- MatrixSSL is an open-source TLS/SSL implementation designed for custom applications in embedded hardware environments. The MatrixSSL library contains a...6 KB (554 words) - 07:49, 20 January 2023
- Intel Trusted Execution Technology (Intel TXT, formerly known as LaGrande Technology) is a computer hardware technology of which the primary goals are:...12 KB (1,536 words) - 04:24, 30 August 2023
- A point of presence (PoP) is an artificial demarcation point or network interface point between communicating entities. A common example is an ISP point...2 KB (180 words) - 14:54, 28 August 2022
- In computing, paravirtualization or para-virtualization is a virtualization technique that presents a software interface to the virtual machines which...9 KB (1,036 words) - 21:13, 24 April 2024
- String functions are used in computer programming languages to manipulate a string or query information about a string (some do both). Most programming...124 KB (4,068 words) - 13:48, 3 March 2024
- Web IDL is an interface description language (IDL) format for describing APIs (application programming interfaces) that are intended to be implemented...5 KB (435 words) - 16:15, 6 October 2023
- Microsoft BizTalk Server is an inter-organizational middleware system (IOMS) that automates business processes through the use of adapters which are tailored...15 KB (1,346 words) - 17:05, 6 April 2024
- In negotiation theory, the best alternative to a negotiated agreement or BATNA (no deal option) refers to the most advantageous alternative course of action...13 KB (1,765 words) - 20:07, 10 April 2024
- The Chyron Corporation, formerly ChyronHego Corporation, headquartered in Melville, New York, is a company that specializes in broadcast graphics creation...12 KB (1,517 words) - 02:10, 11 December 2023
- In video coding, a group of pictures, or GOP structure, specifies the order in which intra- and inter-frames are arranged. The GOP is a collection of successive...7 KB (931 words) - 14:17, 4 April 2024