Malware
Malware, short for malicious software, is software used or created to disrupt computer operation, gather sensitive information, or gain access to private computer systems. It can appear in the form of code, scripts, active content, and other software.[1] 'Malware' is a general term used to refer to a variety of forms of hostile, intrusive, or annoying software.[2]
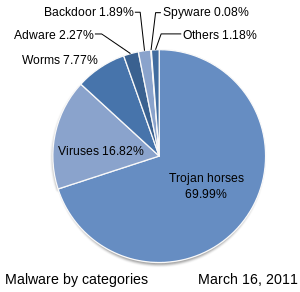
Malware includes computer viruses, worms, trojan horses, spyware, adware, and other malicious programs. In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.[3][4] Malware is not the same as defective software, which is software that has a legitimate purpose but contains harmful bugs that were not noticed before release. However, some malware is disguised as genuine software, and may come from an official company website. An example of this is software used for harmless purposes that is packed with additional tracking software that gathers marketing statistics.
Malware has caused the rise in use of protective software types such as anti virus, anti-malware, and firewalls. Each of these are commonly used by personal users and corporate networks in order to stop the unauthorized access by other computer users, as well as the automated spread of malicious scripts and software.
Purposes
Many early infectious programs, including the first Internet Worm, were written as experiments or pranks. Today, malware is used primarily to steal sensitive personal, financial, or business information for the benefit of others.
Malware is sometimes used broadly against government or corporate websites to gather guarded information, or to disrupt their operation in general. However, malware is often used against individuals to gain personal information such as social security numbers, bank or credit card numbers, and so on. Left un-guarded, personal and networked computers can be at considerable risk against these threats. (These are most frequently counter-acted by various types of firewalls, anti virus software, and network hardware).
Since the rise of widespread broadband Internet access, malicious software has more frequently been designed for profit. Since 2003, the majority of widespread viruses and worms have been designed to take control of users' computers for black-market exploitation.[5] Infected "zombie computers" are used to send email spam, to host contraband data such as child pornography,[6] or to engage in distributed denial-of-service attacks as a form of extortion.[7]
Another strictly for-profit category of malware has emerged, called spyware. These programs are designed to monitor users' web browsing, display unsolicited advertisements, or redirect affiliate marketing revenues to the spyware creator. Spyware programs do not spread like viruses; instead they are generally installed by exploiting security holes. They can also be packaged together with user-installed software, such as peer-to-peer application.
Proliferation
Preliminary results from Symantec published in 2008 suggested that "the release rate of malicious code and other unwanted programs may be exceeding that of legitimate software applications."[8] According to F-Secure, "As much malware [was] produced in 2007 as in the previous 20 years altogether."[9] Malware's most common pathway from criminals to users is through the Internet: primarily by e-mail and the World Wide Web.[10]
The prevalence of malware as a vehicle for Internet crime, along with the challenge of anti-malware software to keep up with the continuous stream of new malware, has seen the adoption of a new mindset for individuals and businesses using the Internet. With the amount of malware currently being distributed, some percentage of computers will always be infected. For businesses, especially those that sell mainly over the Internet, this means they need to find a way to operate despite security concerns. The result is a greater emphasis on back-office protection designed to protect against advanced malware operating on customers' computers.[11]
On March 29, 2010, Symantec Corporation named Shaoxing, China, as the world's malware capital.[12] A 2011 study from the University of California, Berkeley, and the Madrid Institute for Advanced Studies published an article in Software Development Technologies, examining how entrepreneurial crackers are helping enable the spread of malware by offering access to computers for a price. Microsoft reported in May 2011 that one in every 14 downloads from the Internet may now contain malware code. Social media, and Facebook in particular, are seeing a rise in the number of tactics used to spread malware to computers.[13]
Infectious malware: viruses and worms
The best-known types of malware, viruses and worms, are known for the manner in which they spread, rather than any specific types of behavior. The term computer virus is used for a program that has infected some executable software and, when run, causes the virus to spread to other executables. On the other hand, a worm is a program that actively transmits itself over a network to infect other computers. These definitions lead to the observation that a virus requires user intervention to spread, whereas a worm spreads itself automatically.
Using this distinction, infections transmitted by email or Microsoft Word documents, which rely on the recipient opening a file or email to infect the system, would be classified as viruses rather than worms. Some writers in the trade and popular press misunderstand this distinction and use the terms interchangeably.
Concealment: Trojan horses, rootkits, and backdoors
Trojan horses
For a malicious program to accomplish its goals, it must be able to run without being detected, shut down, or deleted. When a malicious program is disguised as something normal or desirable, users may willfully install it without realizing it. This is the technique of the Trojan horse or trojan. In broad terms, a Trojan horse is any program that invites the user to run it, concealing harmful or malicious code. The code may take effect immediately and can lead to many undesirable effects, such as deleting the user's files or installing additional harmful software.
One of the most common ways that spyware is distributed is as a Trojan horse, bundled with a piece of desirable software that the user downloads from the Internet. When the user installs the software, the spyware is installed along with it. Spyware authors who attempt to act in a legal fashion may include an end-user license agreement that states the behavior of the spyware in loose terms, which users may not read or understand.
Rootkits
Once a malicious program is installed on a system, it is essential that it stays concealed, to avoid detection. Techniques known as rootkits allow this concealment, by modifying the host's operating system so that the malware is hidden from the user. Rootkits can prevent a malicious process from being visible in the system's list of processes, or keep its files from being read.
Some malicious programs contain routines to defend against removal, not merely to hide themselves, but to resist attempts to remove them. An early example of this behavior is recorded in the Jargon File tale of a pair of programs infesting a Xerox CP-V time sharing system:
- Each ghost-job would detect the fact that the other had been killed, and would start a new copy of the recently stopped program within a few milliseconds. The only way to kill both ghosts was to kill them simultaneously (very difficult) or to deliberately crash the system.[14]
Backdoors
A backdoor is a method of bypassing normal authentication procedures. Once a system has been compromised, one or more backdoors may be installed in order to allow easier access in the future. Backdoors may also be installed prior to malicious software, to allow attackers entry.
The idea has often been suggested that computer manufacturers preinstall backdoors on their systems to provide technical support for customers, but this has never been reliably verified. Crackers typically use backdoors to secure remote access to a computer, while attempting to remain hidden from casual inspection. To install backdoors crackers may use Trojan horses, worms, or other methods.
Vulnerability to malware
In this context, as throughout, it should be borne in mind that the “system” under attack may be of various types, e.g. a single computer and operating system, a network or an application.
Various factors make a system more vulnerable to malware:
- Homogeneity: e.g. when all computers in a network run the same operating system; upon exploiting one, one can exploit them all.
- Weight of numbers: simply because the vast majority of existing malware is written to attack Windows systems, then Windows systems are more vulnerable to succumbing to malware attacks (regardless of the security strengths or weaknesses of Windows itself).
- Defects: malware using defects in the operating system design.
- Unconfirmed code: code from a floppy disk, CD-ROM or USB device may be executed without the user’s permission.
- Over-privileged users: some systems allow all users to modify their internal structures. This was the standard operating procedure for early microcomputer and home computer systems, where there was no distinction between an Administrator or root, and a regular user of the system.
- Over-privileged code: some systems allow code executed by a user to access all rights of that user. Also standard operating procedure for early microcomputer and home computer systems.
Use of the same operating system
An oft-cited cause of vulnerability of networks is consistent use of the same operating system.[15] For example, Microsoft Windows or Mac OS X have such a large share of the market that concentrating on either could enable an exploited vulnerability to subvert a large number of systems. Instead, introducing diversity, purely for the sake of robustness, could increase short-term costs for training and maintenance. However, having a few diverse nodes would deter total shutdown of the network, and allow those nodes to help with recovery of the infected nodes. Such separate, functional redundancy could avoid the cost of a total shutdown.
Software bugs
Most systems contain bugs, or loopholes, which may be exploited by malware. A typical example is the buffer-overrun weakness, in which an interface designed to store data, in a small area of memory, allows the caller to supply more data than will fit. This extra data then overwrites the interface's own executable structure (past the end of the buffer and other data). In this manner, malware can force the system to execute malicious code, by replacing legitimate code with its own payload of instructions (or data values) copied into live memory, outside the buffer area.
Originally, PCs had to be booted from floppy disks. Until recently it was common for a computer to boot from an external device by default. boot device. This meant that a live floppy disk or CD could subvert the computer during booting and boot into a modified operating system.
Over-privileged users
In some systems, non-administrator users are over-privileged by design, in the sense that they are allowed to modify internal structures of the system. In some environments, users are over-privileged because they have been inappropriately granted administrator or equivalent status. This is primarily a configuration decision, but on Microsoft Windows systems the default configuration is to over-privilege the user.
As privilege escalation exploits have increased this priority is shifting for the release of Microsoft Windows Vista. As a result, many existing applications that require excess privilege (over-privileged code) may have compatibility problems with Vista. However, Vista's User Account Control feature attempts to remedy applications not designed for under-privileged users, acting as a crutch to resolve the privileged access problem inherent in legacy applications.
Malware, running as over-privileged code, can use this privilege to subvert the system. Almost all currently popular operating systems, and also many scripting applications allow code too many privileges, usually in the sense that when a user executes code, the system allows that code all rights of that user. This makes users vulnerable to malware in the form of e-mail attachments, which may or may not be disguised.
Anti-malware strategies
As malware attacks become more frequent, attention has begun to shift from viruses and spyware protection, to malware protection, and programs that have been specifically developed to combat malware.
Anti-virus and anti-malware software
anti virus and anti-malware software commonly hooks deep into the operating system's core or kernel functions in a manner similar to how malware itself would attempt to operate, though with the user's informed permission for protecting the system. Any time the operating system does something, the anti-malware software checks that the OS is doing an approved task. This commonly slows down the operating system and/or consumes large amounts of system memory. The goal is to stop any operations the malware may attempt on the system before they occur, including activities which might exploit bugs or trigger unexpected operating system behavior.
Anti-malware programs can combat malware in two ways:
- They can provide real time protection against the installation of malware software on a computer. This type of spyware protection works the same way as that of antivirus protection in that the anti-malware software scans all incoming network data for malware software and blocks any threats it comes across.
- Anti-malware software programs can be used solely for detection and removal of malware software that has already been installed onto a computer. This type of anti-malware software scans the contents of the Windows registry, operating system files, and installed programs on a computer and will provide a list of any threats found, allowing the user to choose which files to delete or keep, or to compare this list to a list of known malware components, removing files that match.
Real-time protection from malware works identically to real-time antivirus protection: the software scans disk files at download time, and blocks the activity of components known to represent malware. In some cases, it may also intercept attempts to install start-up items or to modify browser settings. Because many malware components are installed as a result of browser exploits or user error, using security software (some of which are anti-malware, though many are not) to "sandbox" browsers (essentially babysit the user and their browser) can also be effective in helping to restrict any damage done.
Examples of Microsoft Windows anti virus and anti-malware software include Windows Defender[16] (for Windows XP) and Microsoft Security Essentials[17] (for Vista and Windows 7) for real-time protection, and the Malicious Software Removal Tool.[18]
Website security scans
As malware also harms the compromised websites (by breaking reputation, blacklisting in search engines, etc.), some companies offer website scanning services.[19][20] Such scans periodically check the site, detecting malware, noticed security vulnerabilities, outdated software stack with known security issues, etc. The found issues are only reported to the site owner who can fix them. The provider may also offer the security badge that the owner can only display if the site has been recently scanned.
Eliminating over-privileged code
Over-privileged code dates from the time when most programs were either delivered with a computer or written in-house, and repairing it would at a stroke render most antivirus software almost redundant. It would, however, have appreciable consequences for the user interface and system management.
The system would have to maintain privilege profiles, and know which to apply for each user and program. In the case of newly installed software, an administrator would need to set up default profiles for the new code.
Eliminating vulnerability to rogue device drivers is probably harder than for arbitrary rogue executable. Two techniques, used in VMS, that can help are memory mapping only the registers of the device in question and a system interface associating the driver with interrupts from the device.
Other approaches are:
- Various forms of virtualization, allowing the code unlimited access only to virtual resources
- Various forms of sandbox or jail
- The security functions of Java, in
java.security
Such approaches, however, if not fully integrated with the operating system, would reduplicate effort and not be universally applied, both of which would be detrimental to security.
History of viruses and worms
Before Internet access became widespread, viruses spread on personal computers by infecting the executable boot sectors of floppy disks. By inserting a copy of itself into the machine code instructions in these executables, a virus causes itself to be run whenever a program is run or the disk is booted. Early computer viruses were written for the Apple II and Macintosh, but they became more widespread with the dominance of the IBM PC and MS-DOS system. Executable-infecting viruses are dependent on users exchanging software or boot-able floppies, so they spread rapidly in computer hobbyist circles.
The first worms, network-borne infectious programs, originated not on personal computers, but on multitasking Unix systems. The first well-known worm was the Internet Worm of 1988, which infected SunOS and VAX BSD systems. Unlike a virus, this worm did not insert itself into other programs. Instead, it exploited security holes (vulnerabilities) in network server programs and started itself running as a separate process. This same behavior is used by today's worms as well.
With the rise of the Microsoft Windows platform in the 1990s, and the flexible macros of its applications, it became possible to write infectious code in the macro language of Microsoft Word and similar programs. These macro viruses infect documents and templates rather than applications (executables), but rely on the fact that macros in a Word document are a form of executable code.
Today, worms are most commonly written for the Windows OS, although a few like Mare-D[21] and the Lion worm[22] are also written for Linux and Unix systems. Worms today work in the same basic way as 1988's Internet Worm: they scan the network and use vulnerable computers to replicate. Because they need no human intervention, worms can spread with incredible speed. The SQL Slammer infected thousands of computers in a few minutes.[23]
Academic research
The notion of a self-reproducing computer program can be traced back to initial theories about the operation of complex automata.[24] John von Neumann showed that in theory a program could reproduce itself. This constituted a plausibility result in computability theory. Fred Cohen experimented with computer viruses and confirmed Neumann's postulate and investigated other properties of malware such as detectability, self-obfuscation using rudimentary encryption, and others. His Doctoral dissertation was on the subject of computer viruses.[25]
See also
- Browser hijacker
- Computer crime
- Computer insecurity
- Cyber spying
- Firewall (computing)
- Identity theft
- Industrial espionage
- IT risk
- Malvertising
- Play mp3.exe (trojan)
- Privacy-invasive software
- Security in Web applications
- Social engineering (security)
- Spy software
- Targeted threat
- Web security exploits
- Web server overload causes
- White-collar crime
References
- ^ http://www.us-cert.gov/control_systems/pdf/undirected_attack0905.pdf
- ^ "Defining Malware: FAQ". technet.microsoft.com. Retrieved 2009-09-10.
- ^ National Conference of State Legislatures Virus/Contaminant/Destructive Transmission Statutes by State
- ^ "§18.2-152.4:1 Penalty for Computer Contamination" (PDF). Joint Commission on Technology and Science. Retrieved 2010-09-17.
- ^ "Malware Revolution: A Change in Target". March 2007.
- ^ "Child Porn: Malware's Ultimate Evil". November 2009.
- ^ PC World - Zombie PCs: Silent, Growing Threat.
- ^ "Symantec Internet Security Threat Report: Trends for July–December 2007 (Executive Summary)" (PDF). XIII. Symantec Corp. April 2008: 29. Retrieved 2008-05-11.
{{cite journal}}: Cite journal requires|journal=(help) - ^ "F-Secure Reports Amount of Malware Grew by 100% during 2007" (Press release). F-Secure Corporation. December 4, 2007. Retrieved 2007-12-11.
- ^ "F-Secure Quarterly Security Wrap-up for the first quarter of 2008". F-Secure. March 31, 2008. Retrieved 2008-04-25.
- ^ "Continuing Business with Malware Infected Customers". Gunter Ollmann. October 2008.
- ^ "Symantec names Shaoxing, China as world's malware capital". Engadget. Retrieved 2010-04-15.
- ^ Rooney, Ben (2011-05-23). "Malware Is Posing Increasing Danger". Wall Street Journal.
- ^ "Catb.org". Catb.org. Retrieved 2010-04-15.
- ^ "LNCS 3786 - Key Factors Influencing Worm Infection", U. Kanlayasiri, 2006, web (PDF): SL40-PDF.
- ^ "Windows Defender". Retrieved June 21, 2012.
- ^ "Microsoft Security Essentials". Retrieved June 21, 2012.
- ^ "Malicious Software Removal Tool". Retrieved June 21, 2012.
- ^ An example of the web site scan proposal
- ^ "Safe Browsing (Google Online Security Blog)". Retrieved June 21, 2012.
- ^ Nick Farrell (20 February 2006). "Linux worm targets PHP flaw". The Register. Retrieved 19 May 2010.
- ^ John Leyden (March 28, 2001). "Highly destructive Linux worm mutating". The Register. Retrieved 19 May 2010.
- ^ "Aggressive net bug makes history". BBC News. February 3, 2003. Retrieved 19 May 2010.
- ^ John von Neumann, "Theory of Self-Reproducing Automata", Part 1: Transcripts of lectures given at the University of Illinois, December 1949, Editor: A. W. Burks, University of Illinois, USA, 1966.
- ^ Fred Cohen, "Computer Viruses", PhD Thesis, University of Southern California, ASP Press, 1988.
External links
- Home Computer Security - Carnegie Mellon Software Institute
- OnGuard Online.gov – How to Secure Your Computer
- Template:Dmoz
- Open Security Foundation Data Loss Database
- Internet Crime Complaint Center
- APWG Unified Cybercrime Response and Education
- Video: Mark Russinovich – Advanced Malware Cleaning
- MalCon, International Malware Conference (convention), focused specifically on Malware development, research and containment.
- Jamie Crapanzano (2003): "Deconstructing SubSeven, the Trojan Horse of Choice", SANS Institute, Retrieved on 2011-05-23
- The commercialization of malware distribution: Pay per install
