The Sleuth Kit
This article needs additional citations for verification. (August 2016) |
 | |
| Original author(s) | Brian Carrier |
|---|---|
| Stable release | 4.12.1[1]
/ 29 August 2023 |
| Repository | |
| Written in | C, Perl |
| Operating system | Unix-like, Windows |
| Type | Computer forensics |
| License | IPL, CPL, GPL |
| Website | www |
The Sleuth Kit (TSK) is a library and collection of Unix- and Windows-based utilities for extracting data from disk drives and other storage so as to facilitate the forensic analysis of computer systems. It forms the foundation for Autopsy, a better known tool that is essentially a graphical user interface to the command line utilities bundled with The Sleuth Kit.[2][3]
The collection is open source and protected by the GPL, the CPL and the IPL. The software is under active development and it is supported by a team of developers. The initial development was done by Brian Carrier[4] who based it on The Coroner's Toolkit. It is the official successor platform.[5]
The Sleuth Kit is capable of parsing NTFS, FAT/ExFAT, UFS 1/2, Ext2, Ext3, Ext4, HFS, ISO 9660 and YAFFS2 file systems either separately or within disk images stored in raw (dd), Expert Witness or AFF formats.[6] The Sleuth Kit can be used to examine most Microsoft Windows, most Apple Macintosh OSX, many Linux and some other UNIX computers.
The Sleuth Kit can be used via the included command line tools, or as a library embedded within a separate digital forensic tool such as Autopsy or log2timeline/plaso.
Tools[edit]
Some of the tools included in The Sleuth Kit include:
- ils lists all metadata entries, such as an Inode.
- blkls displays data blocks within a file system (formerly called dls).
- fls lists allocated and unallocated file names within a file system.
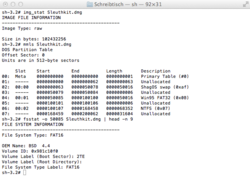
- fsstat displays file system statistical information about an image or storage medium.
- ffind searches for file names that point to a specified metadata entry.
- mactime creates a timeline of all files based upon their MAC times.
- disk_stat (currently Linux-only) discovers the existence of a Host Protected Area.
Applications[edit]
The Sleuth Kit can be used
- for use in forensics, its main purpose
- for understanding what data is stored on a disk drive, even if the operating system has removed all metadata.
- for recovering deleted image files [7]
- summarizing all deleted files[8]
- search for files by name or included keyword [9]
- for use by future historians dealing with computer storage devices
See also[edit]
- Autopsy (software) — A graphical user interface to The Sleuth Kit.
- CAINE Linux − Includes The Sleuth Kit
References[edit]
- ^ "Release 4.12.1". 29 August 2023. Retrieved 19 September 2023.
- ^ Parasram, Shiva V. N. (2017). Digital forensics with Kali Linux: perform data acquisition, digital investigation, and threat analysis using Kali Linux tools. Birmingham, UK. ISBN 978-1-78862-957-7. OCLC 1020288734.
{{cite book}}: CS1 maint: location missing publisher (link) - ^ Altheide, Cory (2011). Digital forensics with open source tools: using open source platform tools for performing computer forensics on target systems: Windows, Mac, Linux, UNIX, etc. Harlan A. Carvey. Burlington, MA: Syngress. ISBN 978-1-59749-587-5. OCLC 713324784.
- ^ "About". www.sleuthkit.org. Brian Carrier. Retrieved 2016-08-30.
- ^ "The Coroner's Toolkit (TCT)".
- ^ "File and Volume System Analysis". www.sleuthkit.org. Brian Carrier. Retrieved 2016-08-30.
- ^ "Autopsy: Lesson 1: Analyzing Deleted JPEGs". www.computersecuritystudent.com. Retrieved 2020-06-20.
- ^ "FS Analysis - SleuthKitWiki". wiki.sleuthkit.org. Retrieved 2020-06-20.
- ^ "The Sleuth Kit - analyze disk images and recover files". LinuxLinks. Retrieved 2020-06-20.
External links[edit]
