Lorenz cipher
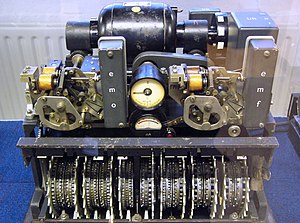
The Lorenz SZ40, SZ42a and SZ42b were German rotor stream cipher machines used by the German Army during World War II. They were developed by C. Lorenz AG in Berlin. The model name SZ was derived from Schlüssel-Zusatz, meaning cipher attachment. The instruments implemented a Vernam stream cipher.
British cryptanalysts, who referred to encrypted German teleprinter traffic as Fish, dubbed the machine and its traffic Tunny (meaning tunafish) and deduced its logical structure three years before they saw such a machine.[1]
The SZ machines were in-line attachments to standard teleprinters. An experimental link using SZ40 machines was started in June 1941. The enhanced SZ42 machines were brought into substantial use from mid-1942 onwards for high-level communications between the German High Command in Wünsdorf close to Berlin, and Army Commands throughout occupied Europe.[2] The more advanced SZ42A came into routine use in February 1943 and the SZ42B in June 1944.[3]
Radioteletype (RTTY) rather than land-line circuits was used for this traffic.[4] These audio frequency shift keying non-Morse (NoMo) messages were picked up by Britain's Y-stations at Knockholt in Kent, its outstation at Higher Wincombe[5] in Wiltshire, and at Denmark Hill in south London, and forwarded to the Government Code and Cypher School at Bletchley Park (BP). Some were deciphered using hand methods before the process was partially automated, first with Robinson machines and then with the Colossus computers.[6] The deciphered Lorenz messages made one of the most significant contributions to British Ultra military intelligence and to Allied victory in Europe, due to the high-level strategic nature of the information that was gained from Lorenz decrypts.[7]
History
[edit]After the Second World War, a group of British and US cryptanalysts entered Germany with the front-line troops to capture the documents, technology and personnel of the various German signal intelligence organizations before these secrets could be destroyed, looted, or captured by the Soviets. They were called the Target Intelligence Committee: TICOM.[8][9]
From captured German cryptographers Drs Huttenhain and Fricke they learnt of the development of the SZ40 and SZ42 a/b.[10] The design was for a machine that could be attached to any teleprinter. The first machine was referred to as the SZ40 (old type) which had ten rotors with fixed cams. It was recognised that the security of this machine was not great. The definitive SZ40 had twelve rotors with movable cams. The rightmost five rotors were called Spaltencäsar but named the Chi wheels by Bill Tutte. The leftmost five were named Springcäsar, Psi wheels to Tutte. The middle two Vorgeleger rotors were called Mu or motor wheels by Tutte.
The five data bits of each ITA2-coded telegraph character were processed first by the five chi wheels and then further processed by the five psi wheels. The cams on the wheels reversed the value of a bit if in the raised position, but left it unchanged if in the lowered position.
Vernam cipher
[edit]Gilbert Vernam was an AT&T Bell Labs research engineer who, in 1917, invented a cipher system that used the Boolean "exclusive or" (XOR) function, symbolised by ⊕.[11] This is represented by the following "truth table", where 1 represents "true" and 0 represents "false".
| Input | A ⊕ B | |
|---|---|---|
| A | B | |
| 0 | 0 | 0 |
| 0 | 1 | 1 |
| 1 | 0 | 1 |
| 1 | 1 | 0 |
Other names for this function are: Not equal (NEQ), modulo 2 addition (without 'carry') and modulo 2 subtraction (without 'borrow').
Vernam's cipher is a symmetric-key algorithm, i.e. the same key is used both to encipher plaintext to produce the ciphertext and to decipher ciphertext to yield the original plaintext:
and:
This produces the essential reciprocity that allows the same machine with the same settings to be used for both encryption and decryption.
Vernam's idea was to use conventional telegraphy practice with a paper tape of the plaintext combined with a paper tape of the key. Each key tape would have been unique (a one-time tape), but generating and distributing such tapes presented considerable practical difficulties. In the 1920s four men in different countries invented rotor cipher machines to produce a key stream to act instead of a tape.[12] The 1940 Lorenz SZ40/42 was one of these.[13]
Operating Principle
[edit]The logical functioning of the Tunny system was worked out well before the Bletchley Park cryptanalysts saw one of the machines—which only happened in 1945, as Germany was surrendering to the Allies.[14]

| OKW/Chi wheel name | A | B | C | D | E | F | G | H | I | K | L | M |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| BP wheel name[15] | ψ1 | ψ2 | ψ3 | ψ4 | ψ5 | μ37 | μ61 | χ1 | χ2 | χ3 | χ4 | χ5 |
| Number of cams (pins) | 43 | 47 | 51 | 53 | 59 | 37 | 61 | 41 | 31 | 29 | 26 | 23 |
The SZ machine served as an in-line attachment to a standard Lorenz teleprinter. It had a metal base 19 in × 15.5 in (48 cm × 39 cm) and was 17 in (43 cm) high.[13] The teleprinter characters consisted of five data bits (or "impulses"), encoded in the International Telegraphy Alphabet No. 2 (ITA2). The machine generated a stream of pseudorandom characters. These formed the key that was combined with the plaintext input characters to form the ciphertext output characters. The combination was by means of the XOR (or modulo 2 addition) process.[16]
The key stream consisted of two component parts that were XOR-ed together. These were generated by two sets of five wheels which rotated together. The Bletchley Park cryptanalyst Bill Tutte called these the χ ("chi") wheels, and the ψ ("psi") wheels. Each wheel had a series of cams (or "pins") around their circumference. These cams could be set in a raised (active) or lowered (inactive) position. In the raised position they generated a '1' which reversed the value of a bit, in the lowered position they generated a '0' which left the bit unchanged.[17] The number of cams on each wheel equalled the number of impulses needed to cause them to complete a full rotation. These numbers are all co-prime with each other, giving the longest possible time before the pattern repeated. This is the product of the number of positions of the wheels. For the set of χ wheels it was 41 × 31 × 29 × 26 × 23 = 22,041,682 and for the ψ wheels it was 43 × 47 × 51 × 53 × 59 = 322,303,017. The number of different ways that all twelve wheels could be set was 1.603×1019 i.e. 16 billion billion.
The set of five χ wheels all moved on one position after each character had been enciphered. The five ψ wheels, however, advanced intermittently. Their movement was controlled by the two μ ("mu") or "motor" wheels in series.[18] The SZ40 μ61 motor wheel stepped every time but the μ37 motor wheel stepped only if the first motor wheel was a '1'. The ψ wheels then stepped only if the second motor wheel was a '1'.[19] The SZ42A and SZ42B models added additional complexity to this mechanism, known at Bletchley Park as Limitations. Two of the four different limitations involved characteristics of the plaintext and so were autoclaves.[20]
The key stream generated by the SZ machines thus had a χ component and a ψ component. Symbolically, the key that was combined with the plaintext for enciphering and with the ciphertext for deciphering, can be represented as follows.[18]
- key = χ-key ⊕ ψ-key
However to indicate that the ψ component often did not change from character to character, the term extended psi was used, symbolised as: Ψ'. So enciphering can be shown symbolically as:
- plaintext ⊕ χ-stream ⊕ ψ'-stream = ciphertext
and deciphering as:
- ciphertext ⊕ χ-stream ⊕ ψ'-stream = plaintext.
Operation
[edit]
Each "Tunny" link had four SZ machines with a transmitting and a receiving teleprinter at each end. For enciphering and deciphering to work, the transmitting and receiving machines had to be set up identically. There were two components to this; setting the patterns of cams on the wheels and rotating the wheels for the start of enciphering a message. The cam settings were changed less frequently before summer 1944. The ψ wheel cams were initially only changed quarterly, but later monthly, the χ wheels were changed monthly but the motor wheel patterns were changed daily. From 1 August 1944, all wheel patterns were changed daily.[21]
Initially the wheel settings for a message were sent to the receiving end by means of a 12-letter indicator sent un-enciphered, the letters being associated with wheel positions in a book. In October 1942, this was changed to the use of a book of single-use settings in what was known as the QEP book. The last two digits of the QEP book entry were sent for the receiving operator to look up in his copy of the QEP book and set his machine's wheels. Each book contained one hundred or more combinations. Once all the combinations in a QEP book had been used it was replaced by a new one.[22] The message settings should never have been re-used, but on occasion they were, providing a "depth", which could be utilised by a cryptanalyst.[23]
As was normal telegraphy practice, messages of any length were keyed into a teleprinter with a paper tape perforator. The typical sequence of operations would be that the sending operator would punch up the message, make contact with the receiving operator, use the EIN / AUS switch on the SZ machine to connect it into the circuit, and then run the tape through the reader.[13] At the receiving end, the operator would similarly connect his SZ machine into the circuit and the output would be printed up on a continuous sticky tape. Because this was the practice, the plaintext did not contain the characters for "carriage return", "line feed" or the null (blank tape, 00000) character.[4]
Cryptanalysis
[edit]
British cryptographers at Bletchley Park had deduced the operation of the machine by January 1942 without ever having seen a Lorenz machine, a feat made possible thanks to mistakes made by German operators.
Interception
[edit]Tunny traffic was known by Y Station operators used to listening to Morse code transmission as "new music". Its interception was originally concentrated at the Foreign Office Y Station operated by the Metropolitan Police at Denmark Hill in Camberwell, London. But due to lack of resources at this time (around 1941), it was given a low priority. A new Y Station, Knockholt in Kent, was later constructed specifically to intercept Tunny traffic so that the messages could be efficiently recorded and sent to Bletchley Park.[24] The head of Y station, Harold Kenworthy, moved to head up Knockholt. He was later promoted to head the Foreign Office Research and Development Establishment (F.O.R.D.E).
Code breaking
[edit]On 30 August 1941, a message of some 4,000 characters was transmitted from Athens to Vienna. However, the message was not received correctly at the other end. The receiving operator then sent an uncoded request back to the sender asking for the message to be retransmitted. This let the codebreakers know what was happening.
The sender then retransmitted the message but, critically, did not change the key settings from the original "HQIBPEXEZMUG". This was a forbidden practice; using a different key for every different message is critical to any stream cipher's security. This would not have mattered had the two messages been identical, however the second time the operator made a number of small alterations to the message, such as using abbreviations, making the second message somewhat shorter.
From these two related ciphertexts, known to cryptanalysts as a depth, the veteran cryptanalyst Brigadier John Tiltman in the Research Section teased out the two plaintexts and hence the keystream. But even almost 4,000 characters of key was not enough for the team to figure out how the stream was being generated; it was just too complex and seemingly random.
After three months, the Research Section handed the task to mathematician Bill Tutte. He applied a technique that he had been taught in his cryptographic training, of writing out the key by hand and looking for repetitions. Tutte did this with the original teleprinter 5-bit International Telegraph Alphabet No. 2 (ITA2) (which was a development of the Baudot code (ITA1)), which led him to his initial breakthrough of recognising a 41-bit repetition.[14][25] Over the following two months up to January 1942, Tutte and colleagues worked out the complete logical structure of the cipher machine. This remarkable piece of reverse engineering was later described as "one of the greatest intellectual feats of World War II".[14]
After this cracking of Tunny, a special team of code breakers was set up under Ralph Tester, most initially transferred from Alan Turing's Hut 8. The team became known as the Testery. It performed the bulk of the subsequent work in breaking Tunny messages, but was aided by machines in the complementary section under Max Newman known as the Newmanry.[26]
Decryption machines
[edit]Several complex machines were built by the British to aid the attack on Tunny. The first was the British Tunny.[27][28] This machine was designed by Bletchley Park, based on the reverse engineering work done by Tiltman's team in the Testery, to emulate the Lorenz Cipher Machine. When the pin wheel settings were found by the Testery, the Tunny machine was set up and run so that the messages could be printed.
A family of machines known as "Robinsons" were built for the Newmanry. These used two paper tapes, along with logic circuitry, to find the settings of the χ pin wheels of the Lorenz machine.[29] The Robinsons had major problems keeping the two paper tapes synchronized and were relatively slow, reading only 2,000 characters per second.

The most important machine was the Colossus of which ten were in use by the war's end, the first becoming operational in December 1943. Although not fully programmable, they were far more efficient than their predecessors, representing advances in electronic digital computers. The Colossus computers were developed and built by Tommy Flowers, of the Dollis Hill Post Office Research Station, using algorithms developed by Bill Tutte and his team of mathematicians.[30] Colossus proved to be efficient and quick against the twelve-rotor Lorenz SZ42 on-line teleprinter cipher machine.
Some influential figures had doubts about his proposed design for the decryption machine, and Flowers proceeded with the project while partly funding it himself.[31][32] Like the later ENIAC of 1946, Colossus did not have a stored program, and was programmed through plugboards and jumper cables. It was faster, more reliable and more capable than the Robinsons, so speeding up the process of finding the Lorenz χ pin wheel settings. Since Colossus generated the putative keys electronically, it only had to read one tape. It did so with an optical reader which, at 5,000 characters per second, was driven much faster than the Robinsons' and meant that the tape travelled at almost 30 miles per hour (48 km/h).[33] This, and the clocking of the electronics from the optically read paper tape sprocket holes, completely eliminated the Robinsons' synchronisation problems. Bletchley Park management, which had been sceptical of Flowers's ability to make a workable device, immediately began pressuring him to construct another. After the end of the war, Colossus machines were dismantled on the orders of Winston Churchill,[34] but GCHQ retained two of them.[35]
Testery executives and Tunny codebreakers
[edit]- Ralph Tester: linguist and head of Testery
- Jerry Roberts: shift-leader, linguist and senior codebreaker
- Peter Ericsson: shift-leader, linguist and senior codebreaker
- Victor Masters: shift-leader
- Denis Oswald: linguist and senior codebreaker
- Peter Hilton: codebreaker and mathematician
- Peter Benenson: codebreaker
- Peter Edgerley: codebreaker
- John Christie: codebreaker
- John Thompson: codebreaker
- Roy Jenkins: codebreaker
- Shaun Wylie: codebreaker
- Tom Colvill: general manager
By the end of the war, the Testery had grown to nine cryptographers and 24 ATS girls (as the women serving that role were then called), with a total staff of 118, organised in three shifts working round the clock.
Surviving machines
[edit]
Lorenz cipher machines were built in small numbers; today only a handful survive in museums.
In Germany, examples may be seen at the Heinz Nixdorf MuseumsForum, a computer museum in Paderborn, and the Deutsches Museum, a museum of science and technology in Munich.[36] Two further Lorenz machines are displayed at both Bletchley Park and The National Museum of Computing in the United Kingdom. Another example is on display at the National Cryptologic Museum in Maryland, the United States.
John Whetter and John Pether, volunteers with The National Museum of Computing, bought a Lorenz teleprinter on eBay for £9.50 that had been retrieved from a garden shed in Southend-on-Sea.[37][38] It was found to be the World War II military version, was refurbished and in May 2016 installed next to the SZ42 machine in the museum's "Tunny" gallery.
See also
[edit]Notes
[edit]- ^ Hinsley 1993, p. 141
- ^ Hinsley 1993, p. 142
- ^ Copeland 2006, pp. 38, 39, "The German Tunny Machine".
- ^ a b Good, Michie & Timms 1945, p. 4 of German Tunny
- ^ "The National Archives: The interception of German Teleprinter Communications at Foreign Office Station Knockholt - Piece details HW 50/79". Retrieved 2023-12-15.
- ^ Good 1993, pp. 160–165
- ^ "The History of the Lorenz Cipher and the Colossus Machine". Stanford University. Retrieved 2018-09-09.
- ^ Parrish 1986, p. 276.
- ^ Rezabek 2017, I Introduction: Origin of TICOM.
- ^ Huttenhain & Fricke 1945, pp. 16–19.
- ^ Klein, p. 2
- ^ Klein, p. 3
- ^ a b c Good, Michie & Timms 1945, p. 10 of German Tunny
- ^ a b c Sale, Tony, The Lorenz Cipher and how Bletchley Park broke it, retrieved 2010-10-21
- ^ Good, Michie & Timms 1945, 1 Introduction: 11 German Tunny, 11B The Tunny Cipher Machine, p. 6.
- ^ Good, Michie & Timms 1945, p. 6 of German Tunny
- ^ Churchhouse 2002, pp. 156, 157.
- ^ a b Good, Michie & Timms 1945, p. 7 of German Tunny
- ^ Roberts, Eric, The Lorenz Schluesselzusatz SZ40/42, Stanford University
- ^ Good, Michie & Timms 1945, p. 8 of German Tunny
- ^ Good, Michie & Timms 1945, p. 14 of German Tunny
- ^ Copeland 2006, p. 45, "The German Tunny Machine".
- ^ Churchhouse 2002, p. 34
- ^ Good, Michie & Timms 1945, p. 281 in Knockholt
- ^ Tutte 1998, pp. 356, 357
- ^ Roberts 2009
- ^ Halton 1993
- ^ Bletchley Park completes epic Tunny machine The Register, 26 May 2011, Accessed May 2011
- ^ Copeland 2006, p. 66, "Machine against Machine".
- ^ "Biography of Professor Tutte - Combinatorics and Optimization". 13 March 2015. Archived from the original on 2019-08-19. Retrieved 2017-05-13.
- ^ Boden, Margaret Ann (2006). Mind as Machine: A History of Cognitive Science. Oxford: Clarendon Press. p. 159. ISBN 9780199543168.
- ^ Atkinson, Paul (2010). Computer. UK: Reaktion Books. p. 29. ISBN 9781861897374.
- ^ Flowers 2006, p. 100
- ^ Verdict of Peace: Britain Between Her Yesterday and the future, Correlli Barnett, 2002
- ^ Copeland 2006, p. 173.
- ^ "Cryptology". Deutsches Museum. Retrieved 2014-10-30.
- ^ O'Connell, Paddy (29 May 2016). "Secret German WW2 Code Machine Found on eBay". Broadcasting House. BBC News. Retrieved 2016-11-06.
- ^ Gayle, Damien; Meikle, James (29 May 2016). "Device Used in Nazi Coding Machine Found for Sale on eBay". The Guardian. London. Retrieved 2016-11-06.
References
[edit]- Churchhouse, Robert (2002), Codes and Ciphers: Julius Caesar, the Enigma and the Internet, Cambridge: Cambridge University Press, ISBN 978-0-521-00890-7
- Copeland, Jack, ed. (2006), Colossus: The Secrets of Bletchley Park's Codebreaking Computers, Oxford: Oxford University Press, ISBN 978-0-19-284055-4
- Davies, Donald W., The Lorenz Cipher Machine SZ42, (reprinted in Selections from Cryptologia: History, People, and Technology, Artech House, Norwood, 1998)
- Flowers, Thomas H. (2006), Colossus in Copeland 2006, pp. 91–100
- Good, Jack (1993), Enigma and Fish in Hinsley & Stripp 1993, pp. 149–166
- Good, Jack; Michie, Donald; Timms, Geoffrey (1945), General Report on Tunny: With Emphasis on Statistical Methods, UK Public Record Office HW 25/4 and HW 25/5, archived from the original on 2010-09-17, retrieved 2010-09-15. (Facsimile copy)
- Sale, Tony (2001), Part of the "General Report on Tunny", the Newmanry History, formatted by Tony Sale (PDF), retrieved 2010-09-20. (Transcript of much of this document in PDF format)
- Ellsbury, Graham, General Report on Tunny With Emphasis on Statistical Methods, retrieved 2010-11-03. (Web transcript of Part 1)
- Halton, Ken (1993), The Tunny Machine in Hinsley & Stripp 1993, pp. 167–174
- Hinsley, F. H.; Stripp, Alan, eds. (1993) [1992], Codebreakers: The inside story of Bletchley Park, Oxford: Oxford University Press, ISBN 978-0-19-280132-6
- Hinsley, F. H. (1993), An introduction to Fish in Hinsley & Stripp 1993, pp. 141–148
- Huttenhain, Orr; Fricke (1945), OKW/Chi Cryptanalytic Research on Enigma, Hagelin and Cipher Teleprinter Messages, TICOM
- Klein, Melville, Securing Record Communication: The TSEC/KW-26 (PDF), archived from the original (PDF) on 2012-03-15, retrieved 2010-09-17
- Parrish, Thomas (1986), The Ultra Americans: The U.S. Role in Breaking the Nazi Codes, New York: Stein and Day, ISBN 978-0-8128-3072-9
- Rezabek, Randy (2017), TICOM: the Hunt for Hitler's Codebreakers, Independently published, ISBN 978-1-5219-6902-1, archived from the original on 2022-05-26, retrieved 2021-01-16
- Roberts, Jerry (2006), Major Tester's Section in Copeland 2006, pp. 249–259
- Roberts, Jerry (2009), My Top-Secret Codebreaking During World War II: The Last British Survivor of Bletchley Park's Testery (video), University College London
- Sale, Tony, The Lorenz Cipher and how Bletchley Park broke it, retrieved 2010-10-21
- Tutte, W. T. (19 June 1998), Fish and I (PDF), archived from the original (PDF) on 2015-02-12, retrieved 2015-02-13 Transcript of a lecture given by Prof. Tutte at the University of Waterloo
- Entry for "Tunny" in the GC&CS Cryptographic Dictionary
Further reading
[edit]- Budiansky, Stephen (2000), Battle of wits: The Complete Story of Codebreaking in World War II, Free Press, ISBN 978-0684859323 Contains a short but informative section (pages 312–315) describing the operation of Tunny, and how it was attacked.
- Flowers, T. H. (1983), "The Design of Colossus", Annals of the History of Computing, 5 (3): 239–252, doi:10.1109/mahc.1983.10079, S2CID 39816473* Paul Gannon, Colossus: Bletchley Park's Greatest Secret (Atlantic Books, 2006). Using recently declassified material and dealing exclusively with the efforts to break into Tunny. Clears up many previous misconceptions about Fish traffic, the Lorenz cipher machine and Colossus.
- Small, Albert W. (1944), The Special Fish Report, retrieved 2010-09-21
- Smith, Michael (2007) [1998], Station X: The Codebreakers of Bletchley Park, Pan Grand Strategy Series (Pan Books ed.), London: Pan MacMillan Ltd, ISBN 978-0-330-41929-1 Contains a lengthy section (pages 148–164) about Tunny and the British attack on it.
External links
[edit]- Frode Weierud's CryptoCellar Historical documents and publications about Lorenz Schlüsselzusatz SZ42. Retrieved 22 April 2016.
- Lorenz ciphers and the Colossus
- Photographs and description of Tunny
- Simplified Lorenz Cipher Toolkit
- Brailsford, David. "Fishy Codes: Bletchley's Other Secret" (video). Brady Haran. Archived from the original on 2021-12-12. Retrieved 2015-07-10.
- "Tunny" Machine and Its Solution – Brigadier General John Tiltman – National Security Agency
- General Report on Tunny: With Emphasis on Statistical Methods – National Archives UK
- General Report on Tunny: With Emphasis on Statistical Methods – Jack Good, Donald Michie, Geoffrey Timms – 1945.
- Virtual Lorenz 3D A 3D browser based simulation of the Lorenz SZ40/42
