IRC flood
This article may need to be rewritten to comply with Wikipedia's quality standards. (January 2012) |
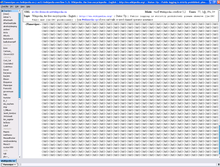
Internet Relay Chat Flooding/Scrolling on an IRC network is a method of disconnecting users from an IRC server (a form of Denial of Service), exhausting bandwidth which causes network latency ('lag'), or just disrupting users. Floods can either be done by scripts (written for a given client) or by external programs.
History[edit]
The history of Internet Relay Chat flooding started as a method of taking over an IRC channel from the original founders of the channel. The first attacks generally used a modified IRC client or an application to flood a channel or a user. Later they started to be based on bots and scripts. This later moved on to starting IRC-based botnets which were capable of DDoS and IRC floods.
Types of floods[edit]
Connect flood[edit]
Connecting and disconnecting from a channel as fast as possible, therefore spamming the channel with dis/connect messages also called q/j flooding.
CTCP flood[edit]
Since CTCP is implemented in almost every client, most users respond to CTCP requests. By sending too many requests, after a couple of answers they get disconnected from the IRC server. The most widely used type is CTCP PING, although some clients also implement other CTCP replies.
DCC flood[edit]
This type consists of initiating many DCC requests simultaneously. Theoretically it can also be used to disconnect users, because the target client sends information back about what port is intended to be used during the DCC session.
ICMP flood[edit]
Typically referred to as a ping flood. This attack overloads the victim's internet connection with an amount of ICMP data exceeding the connection's capacity, potentially causing a disconnection from the IRC network. For the duration of the attack, the user's internet connection remains hindered. Technically speaking, this is not an IRC flood, as the attack itself doesn't traverse the IRC network at all, but operates entirely independent of anything but the raw internet connection and its IP protocol (of which ICMP is a subset). Even so, the actual IP address to flood (the address of the victim's connection) is frequently obtained by looking at the victim's user information (e.g. through the /whois or /dns command) on the IRC network.
Invite flood[edit]
Sending disruptive numbers of invites to a certain channel.
Post flood[edit]
This is the simplest type of IRC flooding. It involves posting large numbers of posts or one very long post with repetitive text. This type of flood can be achieved, for example, by copying and pasting one short word repeatedly.

Message flood[edit]
Sending massive numbers of private messages to the victim, mainly from different connections called clones (see below). Since some clients separate the private conversations into another window, each new message could open a new window for every new user a message is received from. This is exploitable by sending messages from multiple names, causing the target client to open many new windows and potentially swamping the user with boxes. Sometimes the easiest way to close all the windows is to restart the IRC client, although scripts (client extensions) exist to 'validate' unknown nicknames before receiving messages from them.
Notice flood[edit]
Similar to the message, but uses the "notice" command.
Nick flood[edit]
Changing the nick as fast as possible, thus disrupting conversation in the channel.
See also[edit]
References[edit]
This article includes a list of general references, but it lacks sufficient corresponding inline citations. (May 2009) |
- Pioch, Nicolas (1993-02-28). "A short IRC primer". Archived from the original on 2009-08-14. Retrieved 2009-05-25.
- "Logging and Reporting IRC Abuses". Archived from the original on 2009-08-15. Retrieved 2009-05-25.
- Brinton, Aaron (August 1997). "IRC Operators Guide". Archived from the original on 2009-08-14. Retrieved 2009-05-25.
- Powers, Ray (1998-07-30). "The myths of opers..." Archived from the original on 2009-08-15. Retrieved 2009-05-25.
- Reed, Darren (May 1992). A Discussion on Computer Network Conferencing: 5.2.6 Network Friendliness. IETF. doi:10.17487/RFC1324. RFC 1324. Retrieved 2009-05-25.
- Oikarinen, Jarkko; Reed, Darren (May 1993). Internet Relay Chat Protocol: 8.10 Flood control of clients. IETF. doi:10.17487/RFC1459. RFC 1459. Retrieved 2009-05-25.
- Kalt, Christophe (April 2000). Internet Relay Chat: Server Protocol: 5.8 Flood control of clients. IETF. doi:10.17487/RFC2813. RFC 2813. Retrieved 2009-05-25.
- Mutton, Paul (2004-07-27). IRC Hacks (1st ed.). Sebastopol, CA: O'Reilly Media. pp. 302, 98, 134, 170–172, 268–269, 300. ISBN 0-596-00687-X.
- Grimes, Roger A. (August 2001). Malicious Mobile Code: Virus Protection for Windows. Sebastopol, CA: O'Reilly Media. pp. 188, 239–240, 242–243. ISBN 1-56592-682-X.
- (anonymous) (June 1997). Maximum Security: A Hacker's Guide to Protecting Your Internet Site and Network. SAMS Publishing. pp. 140–141. ISBN 1-57521-268-4.
- Crystal, David (2006-09-18). Language and the Internet (2nd ed.). Cambridge University Press. p. 160. ISBN 0-521-86859-9.
- Rheingold, Howard (October 1993). The Virtual Community: Homesteading on the Electronic Frontier (1st ed.). Basic Books. p. 185. ISBN 0-201-60870-7.
- Surratt, Carla G. (1999-08-01). Netaholics?: The Creation of a Pathology. Hauppauge, New York: Nova Science Publishers. p. 156. ISBN 1-56072-675-X.
- Gibbs, Donna; Krause, Kerri-Lee, eds. (2006-06-01). Cyberlines 2.0: Languages and Cultures of the Internet (2nd ed.). James Nicholas Publishers. pp. 270–271. ISBN 1-875408-42-8.
- Piccard, Paul; Baskin, Brian; Edwards, Craig; Spillman, George (2005-05-01). Sachs, Marcus (ed.). Securing IM and P2P Applications for the Enterprise. foreword by Kevin Beaver (1st ed.). Rockland, Massachusetts: Syngress Publishing. ISBN 1-59749-017-2.
- McClure, Stuart; Scambray, Joel; Kurtz, George (2005-04-19). Hacking Exposed 5th Edition: Network Security Secrets And Solutions (5th ed.). New York, New York: McGraw-Hill Professional. pp. 494–497. ISBN 0-07-226081-5.
- Scambray, Joel; Shema, Mike; Sima, Caleb (2006-06-05). Hacking Exposed: Web Applications (2nd ed.). New York, New York: McGraw-Hill Professional. pp. 370–373. ISBN 0-07-226299-0.
- Tipton, Harold F.; Krause, Micki, eds. (2004-12-28). Information Security Management Handbook. Vol. 2 (5th ed.). Auerbach Publications. p. 517. ISBN 0-8493-3210-9.
- Harold F. Tipton, Micki Krause. (2007-05-14). Tipton, Harold F.; Krause, Micki (eds.). Information Security Management Handbook (6th ed.). Auerbach Publications. ISBN 978-0-8493-7495-1.
- Maynor, David; James, Lance; Spammer-X; Bradley, Tony; Thornton, Frank; Haines, Brad; Baskin, Brian; Bhargava, Hersh; Faircloth, Jeremy; Edwards, Craig; Gregg, Michael; Bandes, Ron; Das, Anand M.; Piccard, Paul (November 2006). Emerging Threat Analysis: From Mischief to Malicious. Rockland, Massachusetts: Syngress Publishing. p. 170. ISBN 1-59749-056-3.
- Bidgoli, Hossein (2003-12-23). The Internet Encyclopedia (1st ed.). Hoboken, New Jersey: John Wiley & Sons. pp. 209, 213. ISBN 0-471-22201-1.
- Northcutt, Stephen; Novak, Judy (2002-09-06). Network Intrusion Detection (3rd ed.). SAMS Publishing. ISBN 0-7357-1265-4.
- Douligeris, Christos; Serpanos, Dimitrios N. (2007-06-15). Network Security: Current Status and Future Directions. Hoboken, New Jersey: John Wiley & Sons. ISBN 978-0-471-70355-6.
- Skoudis, Ed; Liston, Tom (2006-01-02). Counter Hack Reloaded: A Step-by-Step Guide to Computer Attacks and Effective Defenses (2nd ed.). Prentice Hall. ISBN 0-13-148104-5.
- King, Todd; Tittel, Ed; Bittlingmeier, David (2003-04-06). Security+ Training Guide. Que Publishing. ISBN 0-7897-2836-2.
- Baskin, Brian; Bradley, Tony; Faircloth, Jeremy; Schiller, Craig A.; Caruso, Ken; Piccard, Paul; James, Lance (2006-09-19). Piltzecker, Tony (ed.). Combating Spyware in the Enterprise (1st ed.). Rockland, Massachusetts: Syngress Publishing. p. 19. ISBN 1-59749-064-4.
- Höök, Kristina; Benyon, David; Munro, Alan J., eds. (2003-01-31). Designing Information Spaces: The Social Navigation Approach (1st ed.). Germany: Springer Science+Business Media. p. 266. ISBN 1-85233-661-7.
- Schiller, Craig A.; Binkley, Jim; Harley, David; Evron, Gadi; Bradley, Tony; Willems, Carsten; Cross, Michael (2007-02-15). Botnets: The Killer Web App. Rockland, Massachusetts: Syngress Publishing. p. 80. ISBN 978-1-59749-135-8.
