Crypto Wars
The Crypto Wars is an unofficial name for the U.S. and allied governments' attempts to limit the public's and foreign nations' access to cryptography strong enough to resist decryption by national intelligence agencies (especially USA's NSA).[2]
Export of cryptography from the United States
Cold War era
In the early days of the Cold War, the U.S. and its allies developed an elaborate series of export control regulations designed to prevent a wide range of Western technology from falling into the hands of others, particularly the Eastern bloc. All export of technology classed as 'critical' required a license. CoCom was organized to coordinate Western export controls.
Two types of technology were protected: technology associated only with weapons of war ("munitions") and dual use technology, which also had commercial applications. In the U.S., dual use technology export was controlled by the Department of Commerce, while munitions were controlled by the State Department. Since in the immediate post WWII period the market for cryptography was almost entirely military, the encryption technology (techniques as well as equipment and, after computers became important, crypto software) was included as a Category XIII item into the United States Munitions List. The multinational control of the export of cryptography on the Western side of the cold war divide was done via the mechanisms of CoCom.
By the 1960s, however, financial organizations were beginning to require strong commercial encryption on the rapidly growing field of wired money transfer. The U.S. Government's introduction of the Data Encryption Standard in 1975 meant that commercial uses of high quality encryption would become common, and serious problems of export control began to arise. Generally these were dealt with through case-by-case export license request proceedings brought by computer manufacturers, such as IBM, and by their large corporate customers.
PC era
Encryption export controls became a matter of public concern with the introduction of the personal computer. Phil Zimmermann's PGP cryptosystem and its distribution on the Internet in 1991 was the first major 'individual level' challenge to controls on export of cryptography. The growth of electronic commerce in the 1990s created additional pressure for reduced restrictions.[3] Shortly afterward, Netscape's SSL technology was widely adopted as a method for protecting credit card transactions using public key cryptography.
SSL-encrypted messages used the RC4 cipher, and used 128-bit keys. U.S. government export regulations would not permit crypto systems using 128-bit keys to be exported.[4] At this stage Western governments had, in practice, a split personality when it came to encryption; policy was made by the military cryptanalysts, who were solely concerned with preventing their 'enemies' acquiring secrets, but that policy was then communicated to commerce by officials whose job was to support industry.
The longest key size allowed for export without individual license proceedings was 40 bits, so Netscape developed two versions of its web browser. The "U.S. edition" had the full 128-bit strength. The "International Edition" had its effective key length reduced to 40 bits by revealing 88 bits of the key in the SSL protocol. Acquiring the 'U.S. domestic' version turned out to be sufficient hassle that most computer users, even in the U.S., ended up with the 'International' version,[5] whose weak 40-bit encryption could be broken in a matter of days using a single personal computer. A similar situation occurred with Lotus Notes for the same reasons.[6]
Legal challenges by Peter Junger and other civil libertarians and privacy advocates, the widespread availability of encryption software outside the U.S., and the perception by many companies that adverse publicity about weak encryption was limiting their sales and the growth of e-commerce, led to a series of relaxations in US export controls, culminating in 1996 in President Bill Clinton signing the Executive order 13026[7] transferring the commercial encryption from the Munition List to the Commerce Control List. Furthermore, the order stated that, "the software shall not be considered or treated as 'technology'" in the sense of Export Administration Regulations. This order permitted the United States Department of Commerce to implement rules that greatly simplified the export of commercial and open source software containing cryptography, which they did in 2000.[8]
Current status
As of 2009, non-military cryptography exports from the U.S. are controlled by the Department of Commerce's Bureau of Industry and Security.[9] Some restrictions still exist, even for mass market products, particularly with regard to export to "rogue states" and terrorist organizations. Militarized encryption equipment, TEMPEST-approved electronics, custom cryptographic software, and even cryptographic consulting services still require an export license[9] (pp. 6–7). Furthermore, encryption registration with the BIS is required for the export of "mass market encryption commodities, software and components with encryption exceeding 64 bits" (75 FR 36494). In addition, other items require a one-time review by or notification to BIS prior to export to most countries.[9] For instance, the BIS must be notified before open-source cryptographic software is made publicly available on the Internet, though no review is required.[10] Export regulations have been relaxed from pre-1996 standards, but are still complex.[9] Other countries, notably those participating in the Wassenaar Arrangement,[11] have similar restrictions.[12]
Mobile phone signals
Clipper Chip

The Clipper chip was a chipset for mobile phones made by the NSA in the 1990s, which implemented encryption with a backdoor for the US government.[3] The US government tried to get phone manufacturers to adopt the chipset, but without success, and the program was finally defunct by 1996.
A5/1 (GSM encryption)
A5/1 is a stream cipher used to provide over-the-air communication privacy in the GSM cellular telephone standard.
Security researcher Ross Anderson reported in 1994 that "there was a terrific row between the NATO signal intelligence agencies in the mid-1980s over whether GSM encryption should be strong or not. The Germans said it should be, as they shared a long border with the Warsaw Pact; but the other countries didn't feel this way, and the algorithm as now fielded is a French design."[13]
According to professor Jan Arild Audestad, at the standardization process which started in 1982, A5/1 was originally proposed to have a key length of 128 bits. At that time, 128 bits was projected to be secure for at least 15 years. It is now estimated that 128 bits would in fact also still be secure as of 2014. Audestad, Peter van der Arend, and Thomas Haug says that the British insisted on weaker encryption, with Haug saying he was told by the British delegate that this was to allow the British secret service to eavesdrop more easily. The British proposed a key length of 48 bits, while the West Germans wanted stronger encryption to protect against East German spying, so the compromise became a key length of 56 bits.[14]
DES Challenges
The widely used DES encryption algorithm was originally planned by IBM to have a key size of 64 bits; NSA lobbied for a key size of 48 bits. The end compromise were a key size of 56 bits.[15] Around 1997 DES was considered insecure by many, and documents leaked in the 2013 Snowden leak shows that it was in fact easily crackable by the NSA, but was still recommended by NIST. The DES Challenges were a series of brute force attack contests created by RSA Security to highlight the lack of security provided by the Data Encryption Standard. As part of the successful cracking of the DES-encoded messages, EFF constructed a specialized DES cracking computer nicknamed Deep Crack.
The successful cracking of DES likely helped gather both political and technical support for more advanced encryption in the hands of ordinary citizens.[16] In 1997, NIST began a competition to select a replacement for DES, resulting in the publication in 2000 of the Advanced Encryption Standard (AES).[17] NSA considers AES strong enough to protect information classified at the Top Secret level.[18]
Snowden and NSA's bullrun program
Fearing widespread adoption of encryption, the NSA set out to stealthily influence and weaken encryption standards and obtain master keys—either by agreement, by force of law, or by computer network exploitation (hacking).[3][19]
According to the New York Times: "But by 2006, an N.S.A. document notes, the agency had broken into communications for three foreign airlines, one travel reservation system, one foreign government’s nuclear department and another’s Internet service by cracking the virtual private networks that protected them. By 2010, the Edgehill program, the British counterencryption effort, was unscrambling VPN traffic for 30 targets and had set a goal of an additional 300."[19]
As part of Bullrun, NSA has also been actively working to "Insert vulnerabilities into commercial encryption systems, IT systems, networks, and endpoint communications devices used by targets".[20] The New York Times has reported that the random number generator Dual_EC_DRBG contains a back door from the NSA, which would allow the NSA to break encryption keys generated by the random number generator.[21] Even though Dual_EC_DRBG was known to be an insecure and slow random number generator soon after the standard was published, and the potential NSA backdoor was found in 2007, and alternative random number generators without these flaws were certified and widely available, RSA Security continued using Dual_EC_DRBG in the company's BSAFE toolkit and Data Protection Manager until September 2013. While RSA Security has denied knowingly inserting a backdoor into BSAFE, it has not yet given an explanation for the continued usage of Dual_EC_DRBG after its flaws became apparent in 2006 and 2007,[22] however it was reported on December 20, 2013 that RSA had accepted a payment of $10 million from the NSA to set the random number generator as the default.[23][24] Leaked NSA documents state that their effort was “a challenge in finesse” and that “Eventually, N.S.A. became the sole editor” of the standard.
By 2010, the NSA had developed “groundbreaking capabilities” against encrypted Internet traffic. A GCHQ document warned however “These capabilities are among the Sigint community’s most fragile, and the inadvertent disclosure of the simple ‘fact of’ could alert the adversary and result in immediate loss of the capability.”[19] Another internal document stated that “there will be NO ‘need to know.’”[19] Several experts, including Bruce Schneier and Christopher Soghoian, have speculated that a successful attack against RC4, a 1987 encryption algorithm still used in at least 50 per cent of all SSL/TLS traffic is a plausible avenue, given several publicly known weaknesses of RC4.[25] Others have speculated that NSA has gained ability to crack 1024-bit RSA and Diffie Hellman public keys.[26] A team of researchers have pointed out that there is wide reuse of a few non-ephemeral 1024 bit primes in Diffie–Hellman implementations, and that NSA having done precomputation against those primes in order to break encryption using them in real time is very plausibly what NSA's "groundbreaking capabilities" refer to.[27]
The Bullrun program is controversial, in that it is believed that NSA deliberately inserts or keeps secret vulnerabilities which affect both law-abiding US citizens as well as NSA's targets, under its NOBUS policy.[28] In theory, NSA has two jobs: prevent vulnerabilities that affect the US, and find vulnerabilities that can be used against US targets; but as argued by Bruce Schneier, NSA seems to prioritize finding (or even creating) and keeping vulnerabilities secret. Bruce Schneier has called for the NSA to be broken up so that the group charged with strengthening cryptography is not subservient to the groups that want to break the cryptography of its targets.[29]
Encryption of smartphone storage
As part of the Snowden leaks, it became widely known that intelligence agencies could bypass encryption of data stored on Android and iOS smartphones by legally ordering Google and Apple to bypass the encryption on specific phones. Around 2014, as a reaction to this, Google and Apple redesigned their encryption so that they did not have the technical ability to bypass it, and it could only be unlocked by knowing the user's password.[30][31]
Various law enforcements officials, including the Obama administration's Attorney General Eric Holder[32] responded with strong condemnation, calling it unacceptable that the state could not access criminals' data even with a warrant. One of the more iconic responses being the chief of detectives for Chicago’s police department stating that "Apple will become the phone of choice for the pedophile".[33] Washington Post posted an editorial insisting that "smartphone users must accept that they cannot be above the law if there is a valid search warrant", and after agreeing that backdoors would be undesirable, suggested implementing a "golden key" backdoor which would unlock the data with a warrant.[34][35]
FBI Director James Comey cited a number of cases to support the need to decrypt smartphones. Incredibly, in none of the presumably carefully handpicked cases did the smartphone have anything to do with the identification or capture of the culprits, and FBI seems to have been unable to find any strong cases supporting the need for smartphone decryption.[36]
Bruce Schneier has labelled the right to smartphone encryption debate Crypto Wars II,[37] while Cory Doctorow called it Crypto Wars redux.[38]
Legislators in the US states of California[39] and New York[40] have proposed bills to outlaw the sale of smartphones with unbreakable encryption. As of February 2016, no bills have been passed.
In February 2016 the FBI obtained a court order demanding that Apple create and electronically sign new software which would enable the FBI to unlock an iPhone 5c it recovered from one of the shooters in the 2015 terrorist attack in San Bernardino, California. Apple has challenged the order. See FBI–Apple encryption dispute.
In April 2016, Dianne Feinstein and Richard Burr sponsored an overly vague bill that would be likely to criminalise all forms of strong encryption.[41][42][43]
2015 UK call for outlawing non-backdoored cryptography
Following the 2015 Charlie Hebdo shooting, an Islamist terrorism attack, former UK Prime Minister David Cameron called for outlawing non-backdoored cryptography, saying that there should be no "means of communication" which "we cannot read".[44][45] US president Barack Obama has sided with Cameron on this.[46]
See also
References
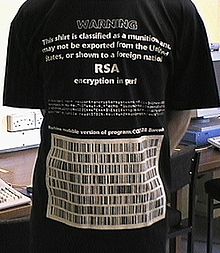
- ^ "Munitions T-shirt". cypherspace.org.
- ^ "The Crypto Wars: Governments Working to Undermine Encryption". Electronic Frontier Foundation.
- ^ a b c Ranger, Steve (24 March 2015). "The undercover war on your internet secrets: How online surveillance cracked our trust in the web". TechRepublic. Archived from the original on 2016-06-12. Retrieved 2016-06-12.
- ^ "SSL by Symantec - Learn How SSL Works - Symantec". verisign.com.
- ^ January 25, 1999 archive of the Netscape Communicator 4.61 download page showing a more difficult path to download 128-bit version at the Wayback Machine (archived September 16, 1999)
- ^ Crypto: How the Code Rebels Beat the Government—Saving Privacy in the Digital Age, Steven Levy, Penguin, 2001
- ^ "Administration of Export Controls on Encryption Products" (PDF). Federalregister.gov. Retrieved 2016-06-11.
- ^ "Revised U.S. Encryption Export Control Regulations (January 2000)". Electronic Privacy Information Center. US Department of Commerce. January 2000. Retrieved 2014-01-06.
- ^ a b c d Robin Gross. "Regulations" (PDF). gpo.gov.
- ^ "U. S. Bureau of Industry and Security - Notification Requirements for "Publicly Available" Encryption Source Code". Bis.doc.gov. 2004-12-09. Retrieved 2009-11-08.
- ^ "Participating States - The Wassenaar Arrangement". Wassenaar.org. Retrieved 11 June 2016.
- ^ "Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies: Guidelines & Procedures, including the Initial Elements" (PDF). Wassenaar.org. December 2009. Retrieved 2016-06-11.[permanent dead link]
- ^ Ross Anderson (1994-06-17). "A5 (Was: HACKING DIGITAL PHONES)". Newsgroup: uk.telecom. Usenet: 2ts9a0$95r@lyra.csx.cam.ac.uk.
- ^ "Sources: We were pressured to weaken the mobile security in the 80's". Aftenposten.
- ^ Stanford Magazine. "Keeping Secrets". Medium.
- ^ "Brute Force". google.com.
- ^ Commerce Department Announces Winner of Global Information Security Competition. Nist.gov (1997-09-12). Retrieved on 2014-05-11.
- ^ Lynn Hathaway (June 2003). "National Policy on the Use of the Advanced Encryption Standard (AES) to Protect National Security Systems and National Security Information" (PDF). Retrieved 2011-02-15.
- ^ a b c d "N.S.A. Able to Foil Basic Safeguards of Privacy on Web". The New York Times. 6 September 2013. Retrieved 11 June 2016.
- ^ "Secret Documents Reveal N.S.A. Campaign Against Encryption". New York Times.
- ^ "New York Times provides new details about NSA backdoor in crypto spec". Ars Technica.
- ^ Matthew Green. "RSA warns developers not to use RSA products".
- ^ Menn, Joseph (December 20, 2013). "Exclusive: Secret contract tied NSA and security industry pioneer". San Francisco: Reuters. Retrieved December 20, 2013.
- ^ Reuters in San Francisco (2013-12-20). "$10m NSA contract with security firm RSA led to encryption 'back door' | World news". theguardian.com. Retrieved 2014-01-23.
{{cite web}}:|author=has generic name (help) - ^ "That earth-shattering NSA crypto-cracking: Have spooks smashed RC4?". theregister.co.uk.
- ^ Lucian Constantin (19 November 2013). "Google strengthens its SSL configuration against possible attacks". PCWorld.
- ^ Adrian, David; Bhargavan, Karthikeyan; Durumeric, Zakir; Gaudry, Pierrick; Green, Matthew; Halderman, J. Alex; Heninger, Nadia; Springall, Drew; Thomé, Emmanuel; Valenta, Luke; VanderSloot, Benjamin; Wustrow, Eric; Zanella-Béguelin, Santiago; Zimmermann, Paul (October 2015). "Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice" (PDF).
- ^ Meyer, David. "Dear NSA, Thanks for Making Us All Insecure". Bloomberg.com. Retrieved 11 June 2016.
- ^ "Schneier on Security". Schneier.com. Retrieved 2016-06-11.
- ^ Matthew Green. "A Few Thoughts on Cryptographic Engineering". cryptographyengineering.com.
- ^ "Keeping the Government Out of Your Smartphone". American Civil Liberties Union.
- ^ "U.S. attorney general criticizes Apple, Google data encryption". Reuters.
- ^ "FBI blasts Apple, Google for locking police out of phones". Washington Post.
- ^ "Compromise needed on smartphone encryption". Washington Post.
- ^ "Washington Post's Clueless Editorial On Phone Encryption: No Backdoors, But How About A Magical 'Golden Key'?". Techdirt.
- ^ "The FBI Director's Evidence Against Encryption Is Pathetic - The Intercept". The Intercept.
- ^ "Schneier on Security". schneier.com.
- ^ Cory Doctorow (October 9, 2014). "Crypto wars redux: why the FBI's desire to unlock your private life must be resisted". the Guardian.
- ^ Farivar, Cyrus (2016-01-21). "Yet another bill seeks to weaken encryption-by-default on smartphones". Ars Technica. Retrieved 2016-06-11.
- ^ Farivar, Cyrus (2016-01-14). "Bill aims to thwart strong crypto, demands smartphone makers be able to decrypt". Ars Technica. Retrieved 2016-06-11.
- ^ Dustin Volz and Mark Hosenball (April 8, 2016). "Leak of Senate encryption bill prompts swift backlash". Reuters.
- ^ "Senate bill effectively bans strong encryption". The Daily Dot.
- ^ "'Leaked' Burr-Feinstein Encryption Bill Is a Threat to American Privacy". Motherboard.
- ^ "BBC News - Can the government ban encryption?". BBC News.
- ^ "UK prime minister wants backdoors into messaging apps or he'll ban them". Ars Technica.
- ^ Danny Yadron. "Obama Sides with Cameron in Encryption Fight". WSJ.
