Spamming
Spamming is the abuse of electronic messaging systems to send unsolicited, bulk messages. While the most widely recognized form of spam is e-mail spam, the term is applied to similar abuses in other media: instant messaging spam, Usenet newsgroup spam, Web search engine spam, spam in blogs, and mobile phone messaging spam.
Below is another example of spam that some people do to wiki's:
I just thought it would be funny to spam.
From Sir Spamalot
http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.comhttp://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com v http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com http://osxx86.orgfree.com nice blog
Spamming is economically viable because advertisers have effectively no operating costs beyond the management of their mailing lists, and it has proved difficult to hold senders accountable for their mass mailings. Because the barrier to entry is so low, spammers are numerous and the volume of unsolicited mail has become very high. The costs, such as lost productivity and fraud, are borne by the public and by Internet service providers, which add extra capacity to cope with the deluge. Spamming is widely reviled, and has been the subject of legislation in many jurisdictions.
Spamming in different media
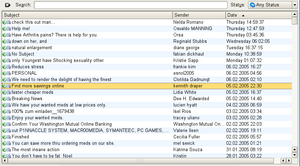
E-mail spam
E-mail spam is the most common form of internet spamming. It involves sending identical or near identical unsolicited messages to a large number of recipients. Unlike legitimate commercial e-mail, spam is generally sent without the explicit permission of the recipients, and frequently contains various tricks to bypass e-mail filters.
Spammers obtain e-mail addresses by a number of means: harvesting addresses from Usenet postings, DNS listings, or Web pages; guessing common names at known domains (known as a dictionary attack); and "e-pending" or searching for e-mail addresses corresponding to specific persons, such as residents in an area. Many spammers utilize programs called web spiders to find e-mail addresses on web pages, although it is possible to fool the web spider by substituting the "@" symbol with another symbol, for example "#", while posting an e-mail address.
Many e-mail spammers go to great lengths to conceal the origin of their messages. They might do this by spoofing e-mail addresses (similar to Internet protocol spoofing). The spammer will modify the e-mail message so it looks like it is coming from another e-mail address. However, many spammers also make it easy for recipients to identify their messages as spam by placing an ad phrase in the From field. Spammers try to circumvent the email filters by intentionally misspelling common spam filter trigger words. For example, "viagra" might become "vaigra", or other symbols may be inserted into the word as in "v/i/a/g./r/a". ISPs have begun to use the misspellings themselves as a filtering test.
The most dedicated spammers—often those making a great deal of money or engaged in illegal activities, such as the pornography, casinos and Nigerian scammers—are often one step ahead of the ISPs. Reporting them to your ISP may help block less sophisticated spammers in the future.
So-called "spambots" are a major producer of e-mail spam. The worst spammers create e-mail viruses that render an unprotected PC a "zombie computer"; the zombie will inform a central unit of its existence, and the central unit will command the "zombie" to send a low volume of spam. This allows spammers to send high volumes of e-mail without being caught by their ISPs or being tracked down by antispammers; a low volume of spam is instead sent from many locations simultaneously.
Bill Gates, speaking at the World Economic Forum in Davos in January 2004, predicted that technology would make spam "a thing of the past" within two years. [1]
Messaging spam
Messaging spam, sometimes termed spim (a portmanteau of spam and IM, short for instant messenger), makes use of instant messaging systems, such as AOL Instant Messenger or ICQ. Many IM systems offer a user directory, including demographic information that allows an advertiser to gather the information, sign on to the system, and send unsolicited messages. To send instant messages to millions of users requires scriptable software and the recipients' IM usernames. Spammers have similarly targeted Internet Relay Chat channels, using IRC bots that join channels and bombard them with advertising.
Messenger service spam has lent itself to spammer use in a particularly circular scheme. In many cases, messenger spammers send messages to vulnerable Windows machines consisting of text like "Annoyed by these messages? Visit this site." The link leads to a Web site where, for a fee, users are told how to disable the Windows messenger service. Though the messenger service is easily disabled for free, the scam works because it creates a perceived need and offers a solution. Often the only "annoying messages" the user receives through Messenger are ads to disable Messenger itself.
Newsgroup spam and Forum spam
Newsgroup spam predates e-mail spam, and targets Usenet newsgroups and it consists of repetitous posting of a message (or substantially similar messages). The Breidbart Index was developed to provide an objective measure of the "spamminess" of a multi-posted or cross-posted message on Usenet. Spamming an internet forum is when a user posts a message that is off-topic or has little relevance to the subject being discussed, or a post that fails to contribute to the thread. Lastly, there is also the case where a person posts messages solely for the purpose of increasing his forum ranking.
Mobile phone spam
Mobile phone spam is directed at the text messaging service of a mobile phone. This can be especially irritating to consumers not only for the inconvenience but also because of the fee that they are charged per text message. The term "SpaSMS" was coined at the adnews website Adland in 2000 to describe spam SMS.
Online game messaging spam
Many online games allow players to contact each other via player-to-player messaging, or chatrooms or public discussion areas. What qualifies as spam varies from game to game, but usually this term applies to all forms of message flooding, violating the terms of service contract for the website.
Spam targeting search engines (Spamdexing)
Spamdexing (a portmanteau of spamming and indexing) refers to the practice on the World Wide Web of deliberately modifying HTML pages to increase the chance of them being placed high on search engine relevancy lists. It uses unethical means, "black hat SEO techniques." to unfairly increase the rank of sites in search engines. Many modern search engines modified their search algorithms to try to exclude web pages utilizing spamdexing tactics.
Blog, wiki, and guestbook spam
Blog spam, or "blam" for short is spamming on weblogs. In 2003, this type of spam took advantage of the open nature of comments in the blogging software Movable Type by repeatedly placing comments to various blog posts that provided nothing more than a link to the spammer's commercial web site. [2] Similar attacks are often performed against wikis and guestbooks, both of which accept user contributions.
Commercial uses
The most common purpose for spamming is advertising. Goods commonly advertised in spam include pornography, unlicensed computer software, medical products such as Viagra, credit card accounts, and fad products. Many of the products advertised are fraudulent in nature, such as quack medications and get-rich-quick schemes. Spam is frequently used to advertise scams, such as diploma mills, advance fee fraud, pyramid schemes, stock pump-and-dump schemes, and phishing.
Some of the most common ad spams are associated with the GAIN advertising network from Claria Corporation - formerly known as Gator. Programs that use GAIN typically hide themselves within the active programs on your computer and collect information on Internet usage and habits. It will then send you relevant advertising at random intervals based on the sites you visit. These programs are often attached and automatically installed with popular free software, such as P2P filesharing clients and screensavers. Even removing these programs from your computer can prove difficult, as it leaves traces of itself even after uninstallation.
Comparison to postal "junk" mail
There are a number of differences between spam and postal junk mail:
- Unlike junk postal mail, the costs of spam paid for by the recipient's mail site commonly approach or exceed those of the sender, in terms of bandwidth, CPU processing time, and storage space. Spammers frequently use free dial-up accounts, so their costs may be quite minimal. Because of this offloading of costs, many consider spamming to be criminal conversion or theft.
- Bulk mail is generally used by businesses that are traceable and can be held responsible for what they send. Spammers frequently operate on a fly-by-night basis, using the anonymity of the Internet as their cover.
Noncommercial spam
E-mail and other forms of spamming have been used for purposes other than advertisements. Many early Usenet spams were religious or political in nature. Serdar Argic, for instance, spammed Usenet with historical revisionist screeds. A number of evangelists have spammed Usenet and e-mail media with preaching messages. A growing number of criminals are also using spam to perpetrate various sorts of fraud[3], and in some cases have used it to lure people to locations where they have been kidnapped, held for ransom and even murdered [4].
Hobbit Spam
In early July 2006 there has been a massive increase in an unsolicited message from a spoofed address with a half dozen or so random letter subject which contains nothing but three lines of text from JRR Tolkein's The Hobbit. This follows fairly closely another similar form dubbed "discordian poetry" that appeared to used a random word generator dubbed "discordian poetry". In both of these there was no apparent attempt to sell anything and was theorized it was a skriptkiddie ineptly running a spamsuite, confirmed when shortly afterward the same format messages began appearing with image files overlaying the text (a common spam technique). It is suspected to be a variation from the same source and image overlays will begin appearing. [[5]]
Spam as denial of service
Spamming has also been used as a denial of service ("DoS") tactic, particularly on Usenet. By overwhelming the readers of a newsgroup with an inordinate number of nonsense messages, legitimate messages can be lost and computing resources are consumed. Since these messages are usually forged (that is, sent falsely under regular posters' names) this tactic has come to be known as sporgery (from spam + forgery). This tactic has for instance been used by partisans of the Church of Scientology against the alt.religion.scientology newsgroup (see Scientology vs. the Internet) and by spammers against news.admin.net-abuse.email, a forum for mail administrators to discuss spam problems. Applied to e-mail, this is termed mailbombing. The Usenet Meow Wars (circa 1996) were DoS attacks on various newsgroups aimed at specific posters, thus disrupting the newsgroups where they were active. The DoS attacks launched by Hipcrime, which continue today, are more specifically crafted as DoS attacks on entire newsgroups. The alt.sex newsgroups were rendered virtually uninhabitable by commercial porn site spammers, partially for advertising purposes and partially to destroy a perceived free competitor. (This spawned the creation of the moderated, unspammable soc.sexuality newsgroups.)
In a handful of cases, forged e-mail spam has been used as a tool of harassment. The spammer collects a list of addresses as usual, then sends a spam to them signed with the name of the person he wishes to harass. Some recipients, angry that they received spam and seeing an obvious "source", will respond angrily or pursue various sorts of revenge against the apparent spammer, the forgery victim. A widely known victim of this sort of harassment was Joe's CyberPost, which has lent its name to the offense: it is known as a joe job. "Joe jobs" have been most often used against antispammers: in more recent examples, Steve Linford of Spamhaus Project and Timothy Walton, a California attorney, have been targeted. Sometimes victims (such as ROKSO-listed spammers) are subscribed to lists that don't practice verified opt-in, such as magazine subscriptions and e-mail newsletters, a practise known as subscriptionbombing.
Spammers have also abused resources set up for purposes of anonymous speech online, such as anonymous remailers. As a result, many of these resources have been shut down, denying their utility to legitimate users.
E-mail worms or viruses may be spammed to set up an initial pool of infected machines, which then resend the virus to other machines in a spam-like manner. The infected machines can often be used as remote-controlled zombie computers, for more conventional spamming or DDoS attacks. Sometimes trojans are spammed to phish for bank account details, or to set up a pool of zombies without using a virus.
In Gaming
The term "spamming" is used in the older sense of something repetitious and disruptive by players ("spammers") of various video games, most often first-person shooters or fighting games. For shooters, it refers to "area denial" tactics—repeatedly firing rockets, grenades, and/or other explosive shells into an area—or to any tactic whereby a large volume of ammunition is expended in the hope of either scoring chance hits, covering teammates' advance with suppressive fire, or clearing or defending an area from an enemy presence. In fighting games, spamming most often refers to overuse of particularly powerful moves, especially if they are easy to execute.
Whether such tactics are viewed as cheating or abusive varies from game to game, community to community. Analogous to camping, the tactical advantage gained by those thus engaged is the crux of the issue. If every player defensively "spams", and no one makes the offensive push, there will be no opportunities for players to come into conflict, and thus there will be no game. Games like Capture the Flag help to break this deadlock by providing incentive to invade enemy territory, however risky.
Conversely, the same term may be used to describe those who flood the in-game chat with needlessly profuse and/or frequent messaging, similar to messaging spam mentioned above. Although perceptions vary within the gaming community, in most arenas excessive messaging is unwelcome. On the other hand, in the role-playing games MUD, MUSH, and MUCK, players happily continue using the word in this original sense, with no implication of abuse. When a player returns to the terminal after a brief break to find his or her screen wonderfully filled with pages of random chat, it's still called "spam". [6]
History
The term spam is derived from the Monty Python SPAM sketch, set in a cafe where every item on the menu includes SPAM luncheon meat. As the server recites the SPAM-filled menu, a chorus of Viking patrons drowns out all conversations with a song repeating "SPAM, SPAM, SPAM, SPAM... lovely SPAM, wonderful SPAM," hence "SPAMming" the dialogue. The excessive amount of SPAM mentioned in the sketch is a reference to British rationing during World War II. SPAM was one of the few foods that was not restricted and was therefore widely available.
Although the first known instance of unsolicited commercial e-mail occurred in 1978 (unsolicited electronic messaging had already taken place over other media, with the first recorded instance being via telegram on September 13 1904), the term "spam" for this practice had not yet been applied. In the 1980s the term was adopted to describe certain abusive users who frequented BBSs and MUDs, who would repeat "SPAM" a huge number of times to scroll other users' text off the screen. In the early Chat rooms in services like PeopleLink and the early days of AOL, they actually flooded the screen with sizeable quotes from the Monty Python routine. This was generally used as a tactic by insiders of a particular group who wanted to drive newcomers out of the room so the usual conversation could continue. This act, previously termed flooding or trashing, came to be called spamming as well. [7] By analogy, the term was soon applied to any large amount of text broadcast by one user, or sometimes by many users.
It later came to be used on Usenet to mean excessive multiple posting—the repeated posting of the same message. The first evident usage of this sense was by Joel Furr in the aftermath of the ARMM incident of March 31 1993, in which a piece of experimental software released dozens of recursive messages onto the news.admin.policy newsgroup. Soon, this use had also become established—to spam Usenet was to flood newsgroups with junk messages.
Commercial spamming started in force on March 5, 1994, when a pair of lawyers, Laurence Canter and Martha Siegel, began using bulk Usenet posting to advertise immigration law services. The incident was commonly termed the "Green Card spam", after the subject line of the postings. The two went on to widely promote spamming of both Usenet and e-mail as a new means of advertisement—over the objections of Internet users they labeled "anti-commerce radicals." Within a few years, the focus of spamming (and antispam efforts) moved chiefly to e-mail, where it remains today. [8]
There are three popular fake etymologies of the word "spam". The first, promulgated by Canter & Siegel themselves, is that "spamming" is what happens when one dumps a can of SPAM luncheon meat into a fan blade. The second is the backronym "shit posing as mail." The third is similar, using "stupid pointless annoying messages."
Hormel Foods Corporation, the makers of SPAM® luncheon meat, do not object to the Internet use of the term "spamming." However, they do ask that the capitalized word "SPAM" be reserved to refer to their product and trademark. [9] By and large, this request is obeyed in forums which discuss spam—to the extent that to write "SPAM" for "spam" brands the writer as a newbie. However, Hormel has begun to press the trademark issue—first, when a firm registered the trademark "SpamArrest" in 2003, Hormel sued to invalidate the mark, [10], and more recently two failed attempts to revoke the mark "spambuster".[11], [12]
Alternate meanings
SPAM could also be taken to mean a set of humorous English backronyms, including: Short/Stupid/Silly Particularly/Pointless Annoying Messages, Self-Promotional Advertising Material, Self Propelled Automatic Mail, Send Post All Members and Sending Persistently Annoying Mail. SPAM is also a portmanteau of "spew" and "scam".
Costs of spam
The California legislature found that spam cost United States organizations alone more than $10 billion in 2004, including lost productivity and the additional equipment, software, and manpower needed to combat the problem.
Spam's direct effects include the consumption of computer and network resources, and the cost in human time and attention of dismissing unwanted messages. In addition, spam has costs stemming from the kinds of spam messages sent, from the ways spammers send them, and from the arms race between spammers and those who try to stop or control spam. In addition, there are the opportunity cost of those who forgo the use of spam-afflicted systems. There are the direct costs, as well as the indirect costs borne by the victims - both those related to the spamming itself, and to other crimes that usually accompany it, such as financial theft, identity theft, data and intellectual property theft, virus and other malware infection, child pornography, fraud, and deceptive marketing.
The methods of spammers are likewise costly. Because spamming contravenes the vast majority of ISPs' acceptable-use policies, most spammers have for many years gone to some trouble to conceal the origins of their spam. E-mail, Usenet, and instant-message spam are often sent through insecure proxy servers belonging to unwilling third parties. Spammers frequently use false names, addresses, phone numbers, and other contact information to set up "disposable" accounts at various Internet service providers. In some cases, they have used falsified or stolen credit card numbers to pay for these accounts. This allows them to quickly move from one account to the next as each one is discovered and shut down by the host ISPs.
The costs of spam also include the collateral costs of the struggle between spammers and the administrators and users of the media threatened by spamming. See [13].
Many users are bothered by spam because it impinges upon the amount of time they spend reading their e-mail. Many also find the content of spam frequently offensive, in that pornography is one of the most frequently advertised products. Spammers send their spam largely indiscriminately, so pornographic ads may show up in a work place e-mail inbox—or a child's, the latter of which is illegal in many jurisdictions. Recently, there has been a noticeable increase in spam advertising websites that contain child pornography.
Some spammers argue that most of these costs could potentially be alleviated by having spammers reimburse ISPs and individuals for their material. There are two problems with this logic: first, the rate of reimbursement they could credibly budget is not nearly high enough to pay the direct costs; and second, the human cost (lost mail, lost time, and lost opportunities) is basically unrecoverable.
E-mail spam exemplifies a tragedy of the commons: spammers use resources (both physical and human), without bearing the entire cost of those resources. In fact, spammers commonly do not bear the cost at all. This raises the costs for everyone. In some ways spam is even a potential threat to the entire e-mail system, as operated in the past.
Since e-mail is so cheap to send, a tiny number of spammers can saturate the Internet with junk mail. Although only a tiny percentage of their targets are motivated to purchase their products (or fall victim to their scams), the low cost may provide a sufficient conversion rate to keep the spamming alive. Furthermore, even though spam appears not to be economically viable as a way for a reputable company to do business, it suffices for professional spammers to convince a tiny proportion of gullible advertisers that it is viable for those spammers to stay in business. Finally, new spammers go into business every day, and the low costs allow a single spammer to do a lot of harm before finally realizing that the business is not profitable.
Some companies and groups "rank" spammers; spammers who make the news are sometimes referred to by these rankings (Spamhaus' "TOP 10 spam service ISPs", The 10 Worst ROKSO Spammers ). The necessary secretiveness of the operations makes uncertainty about how they actually determine "how bad" a spammer is unavoidable. Also, spammers may target different networks to different extents, depending on how successful they are at attacking the target. Thus considerable resources are employed to actually measure the amount of spam generated by a single person or group. For example, victims that use common antispam hardware, software or services provide opportunities for such tracking. Nevertheless, such rankings should be taken with a grain of salt.
To better understand the cost of spam to an organization, MX Logic Email Defense has posted a cost of spam calculator on their website.
Continuously updated statistics from postini track the ebb and flow of e-mail abuse without ranking spammers.
Political issues
Spamming remains a hot discussion topic. In fact, many online users have even suggested (though they were presumably joking) that cruel forms of capital punishment would be appropriate for spammers. In 2004, the seized Porsche of an indicted spammer was advertised on the internet; this revealed the extent of the financial rewards available to those who are willing to commit duplicitous acts online. However, some of the possible means used to stop spamming may lead to other side effects, such as increased government control over the Net, loss of privacy, barriers to free expression, and even the commercialization of e-mail.
One of the chief values favored by many long-time Internet users and experts, as well as by many members of the public, is the free exchange of ideas. Many have valued the relative anarchy of the Internet, and bridle at the idea of restrictions placed upon it. A common refrain from spam-fighters is that spamming itself abridges the historical freedom of the Internet, by attempting to force users to carry the costs of material which they would not choose.
An ongoing concern expressed by parties such as the Electronic Frontier Foundation and the ACLU has to do with so-called "stealth blocking", a term for ISPs employing aggressive spam blocking without their users' knowledge. These groups' concern is that ISPs or technicians seeking to reduce spam-related costs may select tools which (either through error or design) also block non-spam e-mail from sites seen as "spam-friendly". SPEWS is a common target of these criticisms. Few object to the existence of these tools; it is their use in filtering the mail of users who are not informed of their use which draws fire.
Some see spam-blocking tools as a threat to free expression—and laws against spamming as an untoward precedent for regulation or taxation of e-mail and the Internet at large. Even though it is possible in some jurisdictions to treat some spam as unlawful merely by applying existing laws against trespass and conversion, some laws specifically targeting spam have been proposed. In 2004, United States passed the Can Spam Act of 2003 which provided ISPs with tools to combat spam. This act allowed Yahoo! to successfully sue Eric Head, reportedly one of the biggest spammers in the world, who settled the lawsuit for several thousand U.S. dollars in June 2004. But the law is criticized by many for not being effective enough. Indeed, the law was supported by some spammers and organizations which support spamming, and opposed by many in the antispam community. Examples of effective anti-abuse laws that respect free speech rights include those in the U.S. against unsolicited faxes and phone calls, and those in Australia and a few U.S. states against spam.
In November 2004, Lycos Europe released a screensaver called make LOVE not SPAM which made Distributed Denial of Service attacks on the spammers themselves. It met with a large amount of controversy and the initiative ended in December 2004.
Court cases
Attorney Laurence Canter was disbarred by the Supreme Court of Tennessee in 1997 for sending prodigious amounts of spam advertising his immigration law practice.
Robert Soloway lost a case in a federal court against the operator of a small Oklahoma-based Internet service provider who accused him of spamming. In another case against Soloway, U.S. Judge Ralph G. Thompson granted a motion by plaintiff Robert Braver for a default judgment and permanent injunction against him. The judgment includes a statutory damages award of $10,075,000 under Oklahoma law.
In the first successful case of its kind, Mr. Nigel Roberts from the Channel Islands won £270 against Media Logistics UK who sent junk e-mails to his personal account. [14]
Newsgroups
- news.admin.net-abuse.email
- others in news.admin.net-abuse.* hierarchy
- alt.spam
See also
- Nigerian spam
- Phishing
- E-mail fraud
- Make money fast
- Job Scams
- Internet Troll
- List of e-mail spammers
- Social networking spam
External links
- Forward deceptive advertising (SPAM) to the Federal Trade Commission who pursue law enforcement actions against people who send deceptive email
- The Incredible Spam Museum A search engine-like site that collects and publish spam e-mails
- SpamHelp Anti-Spam Articles
- E-mail Address Harvesting: How Spammers Reap What You Sow by the Federal Trade Commission
- Spam FAQs
- JunkBusters on SPAM (junk e-mail)
