Portal talk:Mathematics/Archive2020
Page contents not supported in other languages.
From Wikipedia, the free encyclopedia
| This page is an archive of past discussions. Do not edit the contents of this page. If you wish to start a new discussion or revive an old one, please do so on the current talk page. |
Duplicate "Did you know"
Number 34 and Number 43 in “Did you know” of Mathematics Portal are the same. — Preceding unsigned comment added by AshrithSagar (talk • contribs) 08:22, 5 June 2020 (UTC)
WP:RECOG discussion
dcljr, what do you think about automating the "Selected article" section using {{Transclude list item excerpts as random slideshow}}? This can be done after JL-Bot populates the section #Recognized content above. For an example of how it works, see Portal:Sports and its list of articles populated by the bot. —andrybak (talk) 18:14, 8 June 2020 (UTC)
- Have not had a chance to look into this. Hang on… - dcljr (talk) 07:22, 10 June 2020 (UTC)
- Dcljr, JL-Bot has updated the section above. 48 featured and good articles in total. Perhaps, more templates and categories could be added to the current list, which I made from Wikipedia:WikiProject_Council/Directory/Science#Mathematics. —andrybak (talk) 16:38, 18 June 2020 (UTC)
- The bot output has been moved to Portal:Mathematics/Recognized content. —andrybak (talk) 15:12, 5 November 2020 (UTC)
- Here's a demo of how this would look like:
-
Image 1COBOL (/ˈkoʊbɒl, -bɔːl/; an acronym for "common business-oriented language") is a compiled English-like computer programming language designed for business use. It is an imperative, procedural and, since 2002, object-oriented language. COBOL is primarily used in business, finance, and administrative systems for companies and governments. COBOL is still widely used in applications deployed on mainframe computers, such as large-scale batch and transaction processing jobs. Many large financial institutions were developing new systems in the language as late as 2006, but most programming in COBOL today is purely to maintain existing applications. Programs are being moved to new platforms, rewritten in modern languages or replaced with other software.
COBOL was designed in 1959 by CODASYL and was partly based on the programming language FLOW-MATIC designed by Grace Hopper. It was created as part of a U.S. Department of Defense effort to create a portable programming language for data processing. It was originally seen as a stopgap, but the Defense Department promptly forced computer manufacturers to provide it, resulting in its widespread adoption. It was standardized in 1968 and has been revised five times. Expansions include support for structured and object-oriented programming. The current standard is ISO/IEC 1989:2023. (Full article...) -
Image 2

Euclid's method for finding the greatest common divisor (GCD) of two starting lengths BA and DC, both defined to be multiples of a common "unit" length. The length DC being shorter, it is used to "measure" BA, but only once because the remainder EA is less than DC. EA now measures (twice) the shorter length DC, with remainder FC shorter than EA. Then FC measures (three times) length EA. Because there is no remainder, the process ends with FC being the GCD. On the right Nicomachus's example with numbers 49 and 21 resulting in their GCD of 7 (derived from Heath 1908:300).
In mathematics, the Euclidean algorithm, or Euclid's algorithm, is an efficient method for computing the greatest common divisor (GCD) of two integers (numbers), the largest number that divides them both without a remainder. It is named after the ancient Greek mathematician Euclid, who first described it in his Elements (c. 300 BC).
It is an example of an algorithm, a step-by-step procedure for performing a calculation according to well-defined rules,
and is one of the oldest algorithms in common use. It can be used to reduce fractions to their simplest form, and is a part of many other number-theoretic and cryptographic calculations.
The Euclidean algorithm is based on the principle that the greatest common divisor of two numbers does not change if the larger number is replaced by its difference with the smaller number. For example, 21 is the GCD of 252 and 105 (as 252 = 21 × 12 and 105 = 21 × 5), and the same number 21 is also the GCD of 105 and 252 − 105 = 147. Since this replacement reduces the larger of the two numbers, repeating this process gives successively smaller pairs of numbers until the two numbers become equal. When that occurs, they are the GCD of the original two numbers. By reversing the steps or using the extended Euclidean algorithm, the GCD can be expressed as a linear combination of the two original numbers, that is the sum of the two numbers, each multiplied by an integer (for example, 21 = 5 × 105 + (−2) × 252). The fact that the GCD can always be expressed in this way is known as Bézout's identity. (Full article...) -
Image 3The Math Myth: And Other STEM Delusions is a 2016 nonfiction book by Queens College political scientist Andrew Hacker analyzing and critiquing the United States educational system's teaching of mathematics as a linear progression towards more advanced fields. Based off a 2012 New York Times op-ed by Hacker titled "Is Algebra Necessary", Hacker argues that the teaching of advanced algebra, trigonometry, and calculus is not useful to the majority of students. He further claims that the requirement of advanced mathematics courses in secondary education contributes to dropout rates and impedes socioeconomically disadvantaged students from pursuing further education. Hacker critiques the Common Core system and American focus on STEM education in lieu of social sciences, arguing that the educational system should prioritize "numeracy" over pure mathematics education.
The Math Myth received broadly critical coverage from critics and mathematicians, some citing Hacker's arguments as "disingenuous" and contributing to an elitist attitude towards mathematics, with many citing a lack of exploration on mathematics in early childhood and primary education. Others praised Hacker's work, describing the book as offering a convincing critique of STEM education in the United States and empowering to students struggling in mathematics. (Full article...) -
Image 4

17 indivisible camels
The 17-animal inheritance puzzle is a mathematical puzzle involving unequal but fair allocation of indivisible goods, usually stated in terms of inheritance of a number of large animals (17 camels, 17 horses, 17 elephants, etc.) which must be divided in some stated proportion among a number of beneficiaries.
Despite often being framed as a puzzle, it is more an anecdote about a curious calculation than a problem with a clear mathematical solution. Beyond recreational mathematics and mathematics education, the story has been repeated as a parable with varied metaphorical meanings. (Full article...) -
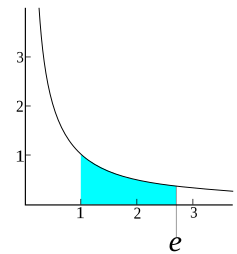
Image 5
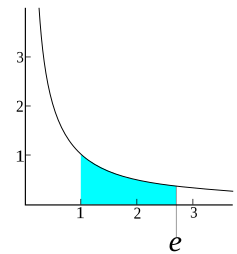
Graph of the equation y = 1/x. Here, e is the unique number larger than 1 that makes the shaded area under the curve equal to 1.
The number e is a mathematical constant approximately equal to 2.71828 that can be characterized in many ways. It is the base of the natural logarithm function. It is the limit ofas n tends to infinity, an expression that arises in the computation of compound interest. It is the value at 1 of the (natural) exponential function, commonly denoted
It is also the sum of the infinite series
There are various other characterizations; see § Definitions and § Representations.
The number e is sometimes called Euler's number, after the Swiss mathematician Leonhard Euler, though this can invite confusion with Euler numbers, or with Euler's constant, a different constant typically denoted. Alternatively, e can be called Napier's constant after John Napier. The constant was discovered by the Swiss mathematician Jacob Bernoulli while studying compound interest. (Full article...)
-
Image 6Bust of Shen at the Beijing Ancient Observatory
Shen Kuo (Chinese: 沈括; 1031–1095) or Shen Gua, courtesy name Cunzhong (存中) and pseudonym Mengqi (now usually given as Mengxi) Weng (夢溪翁), was a Chinese polymath, scientist, and statesman of the Song dynasty (960–1279). Shen was a master in many fields of study including mathematics, optics, and horology. In his career as a civil servant, he became a finance minister, governmental state inspector, head official for the Bureau of Astronomy in the Song court, Assistant Minister of Imperial Hospitality, and also served as an academic chancellor. At court his political allegiance was to the Reformist faction known as the New Policies Group, headed by Chancellor Wang Anshi (1021–1085).
In his Dream Pool Essays or Dream Torrent Essays (夢溪筆談; Mengxi Bitan) of 1088, Shen was the first to describe the magnetic needle compass, which would be used for navigation (first described in Europe by Alexander Neckam in 1187). Shen discovered the concept of true north in terms of magnetic declination towards the north pole, with experimentation of suspended magnetic needles and "the improved meridian determined by Shen's [astronomical] measurement of the distance between the pole star and true north". This was the decisive step in human history to make compasses more useful for navigation, and may have been a concept unknown in Europe for another four hundred years (evidence of German sundials made circa 1450 show markings similar to Chinese geomancers' compasses in regard to declination). (Full article...) -
Image 7

Rust is a multi-paradigm, general-purpose programming language that emphasizes performance, type safety, and concurrency. It enforces memory safety—meaning that all references point to valid memory—without a garbage collector. To simultaneously enforce memory safety and prevent data races, its "borrow checker" tracks the object lifetime of all references in a program during compilation.
Rust was influenced by ideas from functional programming, including immutability, higher-order functions, and algebraic data types. It is popular for systems programming. (Full article...) -
Image 8
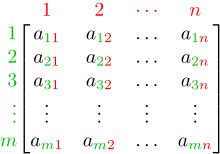
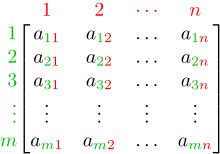
An m × n matrix: the m rows are horizontal and the n columns are vertical. Each element of a matrix is often denoted by a variable with two subscripts. For example, a2,1 represents the element at the second row and first column of the matrix.
In mathematics, a matrix (pl.: matrices) is a rectangular array or table of numbers, symbols, or expressions, arranged in rows and columns, which is used to represent a mathematical object or a property of such an object.
For example,
is a matrix with two rows and three columns. This is often referred to as a "two by three matrix", a "matrix", or a matrix of dimension
. (Full article...)
-
Image 9In computer science, 2-satisfiability, 2-SAT or just 2SAT is a computational problem of assigning values to variables, each of which has two possible values, in order to satisfy a system of constraints on pairs of variables. It is a special case of the general Boolean satisfiability problem, which can involve constraints on more than two variables, and of constraint satisfaction problems, which can allow more than two choices for the value of each variable. But in contrast to those more general problems, which are NP-complete, 2-satisfiability can be solved in polynomial time.
Instances of the 2-satisfiability problem are typically expressed as Boolean formulas of a special type, called conjunctive normal form (2-CNF) or Krom formulas. Alternatively, they may be expressed as a special type of directed graph, the implication graph, which expresses the variables of an instance and their negations as vertices in a graph, and constraints on pairs of variables as directed edges. Both of these kinds of inputs may be solved in linear time, either by a method based on backtracking or by using the strongly connected components of the implication graph. Resolution, a method for combining pairs of constraints to make additional valid constraints, also leads to a polynomial time solution. The 2-satisfiability problems provide one of two major subclasses of the conjunctive normal form formulas that can be solved in polynomial time; the other of the two subclasses is Horn-satisfiability. (Full article...) -
Image 10

The regular heptagon cannot be constructed using only a straightedge and compass construction; this can be proven using the field of constructible numbers.
In mathematics, a field is a set on which addition, subtraction, multiplication, and division are defined and behave as the corresponding operations on rational and real numbers. A field is thus a fundamental algebraic structure which is widely used in algebra, number theory, and many other areas of mathematics.
The best known fields are the field of rational numbers, the field of real numbers and the field of complex numbers. Many other fields, such as fields of rational functions, algebraic function fields, algebraic number fields, and p-adic fields are commonly used and studied in mathematics, particularly in number theory and algebraic geometry. Most cryptographic protocols rely on finite fields, i.e., fields with finitely many elements. (Full article...) -
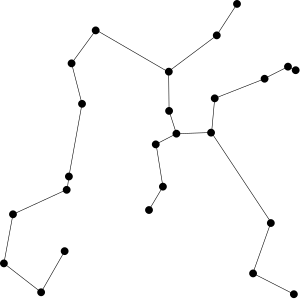
Image 11
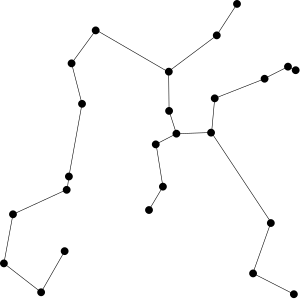
Euclidean minimum spanning tree of 25 random points in the plane
A Euclidean minimum spanning tree of a finite set of points in the Euclidean plane or higher-dimensional Euclidean space connects the points by a system of line segments with the points as endpoints, minimizing the total length of the segments. In it, any two points can reach each other along a path through the line segments. It can be found as the minimum spanning tree of a complete graph with the points as vertices and the Euclidean distances between points as edge weights.
The edges of the minimum spanning tree meet at angles of at least 60°, at most six to a vertex. In higher dimensions, the number of edges per vertex is bounded by the kissing number of tangent unit spheres. The total length of the edges, for points in a unit square, is at most proportional to the square root of the number of points. Each edge lies in an empty region of the plane, and these regions can be used to prove that the Euclidean minimum spanning tree is a subgraph of other geometric graphs including the relative neighborhood graph and Delaunay triangulation. By constructing the Delaunay triangulation and then applying a graph minimum spanning tree algorithm, the minimum spanning tree ofgiven planar points may be found in time
, as expressed in big O notation. This is optimal in some models of computation, although faster randomized algorithms exist for points with integer coordinates. For points in higher dimensions, finding an optimal algorithm remains an open problem. (Full article...)
-
Image 12

Three of the ordinary lines in a 4 × 4 grid of points
The Sylvester–Gallai theorem in geometry states that every finite set of points in the Euclidean plane has a line that passes through exactly two of the points or a line that passes through all of them. It is named after James Joseph Sylvester, who posed it as a problem in 1893, and Tibor Gallai, who published one of the first proofs of this theorem in 1944.
A line that contains exactly two of a set of points is known as an ordinary line. Another way of stating the theorem is that every finite set of points that is not collinear has an ordinary line. According to a strengthening of the theorem, every finite point set (not all on one line) has at least a linear number of ordinary lines. An algorithm can find an ordinary line in a set ofpoints in time
. (Full article...)
-
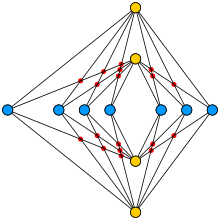
Image 13
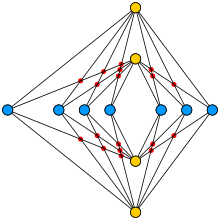
An optimal drawing of K4,7, with 18 crossings (red dots)
In the mathematics of graph drawing, Turán's brick factory problem asks for the minimum number of crossings in a drawing of a complete bipartite graph. The problem is named after Pál Turán, who formulated it while being forced to work in a brick factory during World War II.
A drawing method found by Kazimierz Zarankiewicz has been conjectured to give the correct answer for every complete bipartite graph, and the statement that this is true has come to be known as the Zarankiewicz crossing number conjecture. The conjecture remains open, with only some special cases solved. (Full article...) -
Image 14

Dyadic rationals in the interval from 0 to 1
In mathematics, a dyadic rational or binary rational is a number that can be expressed as a fraction whose denominator is a power of two. For example, 1/2, 3/2, and 3/8 are dyadic rationals, but 1/3 is not. These numbers are important in computer science because they are the only ones with finite binary representations. Dyadic rationals also have applications in weights and measures, musical time signatures, and early mathematics education. They can accurately approximate any real number.
The sum, difference, or product of any two dyadic rational numbers is another dyadic rational number, given by a simple formula. However, division of one dyadic rational number by another does not always produce a dyadic rational result. Mathematically, this means that the dyadic rational numbers form a ring, lying between the ring of integers and the field of rational numbers. This ring may be denoted. (Full article...)
-
Image 15
Marian Adam Rejewski (Polish: [ˈmarjan rɛˈjɛfskʲi] ⓘ; 16 August 1905 – 13 February 1980) was a Polish mathematician and cryptologist who in late 1932 reconstructed the sight-unseen German military Enigma cipher machine, aided by limited documents obtained by French military intelligence.
Over the next nearly seven years, Rejewski and fellow mathematician-cryptologists Jerzy Różycki and Henryk Zygalski, working at the Polish General Staff's Cipher Bureau, developed techniques and equipment for decrypting the Enigma ciphers, even as the Germans introduced modifications to their Enigma machines and encryption procedures. Rejewski's contributions included the cryptologic card catalog and the cryptologic bomb. (Full article...)
Unfinished selected pictures
dcljr, please see the added captions:
If that's enough, I'll remove the disclaimer and add these pictures to the rotation on the portal's page. —andrybak (talk) 13:29, 5 November 2020 (UTC)
Hidden category: