Ksplice
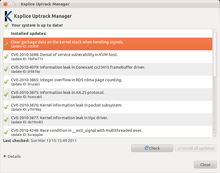 A screenshot of the Ksplice Uptrack with applied updates | |
| Developer(s) | Ksplice, Inc. |
|---|---|
| Initial release | 23 April 2008[1] |
| Stable release | 1.0.35
|
| Operating system | Linux |
| Type | Kernel extension |
| License | GNU GPL version 2[2][3] |
| Website | www |
Ksplice is an open-source[2][3] extension of the Linux kernel that allows security patches to be applied to a running kernel without the need for reboots, avoiding downtimes and improving availability (a technique broadly referred to as dynamic software updating). Ksplice supports only the patches that do not make significant semantic changes to kernel's data structures.[4]
Ksplice has been implemented for Linux on the x86-64 and AArch64 architectures.[5] It was developed by Ksplice, Inc. until 21 July 2011, when Oracle acquired Ksplice and then offered support for Oracle Linux. Support for Red Hat Enterprise Linux was dropped and turned into a free 30-day trial for RHEL customers as an incentive to migrate to Oracle Linux Premier Support.[6][7]
Ksplice is today offered on the two kernel flavors distributed with Oracle Linux:
As of July 2015[update], Ksplice is available for free on desktop Linux installations, with official support available for Ubuntu Linux distribution.[8]
Design
[edit]
Ksplice takes as input a unified diff and the original kernel source code, and it updates the running kernel in memory. Using Ksplice does not require any preparation before the system is originally booted, (the running kernel needs no special prior compiling, for example). In order to generate an update, Ksplice must determine what code within the kernel has been changed by the source code patch. Ksplice performs this analysis at the Executable and Linkable Format (ELF) object code layer, rather than at the C source code layer.[9]
To apply a patch, Ksplice first freezes execution of a computer so it is the only program running. The system verifies that no processors were in the middle of executing functions that will be modified by the patch. Ksplice modifies the beginning of changed functions so that they instead point to new, updated versions of those functions, and modifies data and structures in memory that need to be changed. Finally, Ksplice resumes each processor running where it left off.[9]
To be fully automatic, Ksplice's design was originally limited to patches that did not introduce semantic changes to data structures, since most Linux kernel security patches do not make these kinds of changes. An evaluation against Linux kernel security patches from May 2005 to May 2008 found that Ksplice was able to apply fixes for all the 64 significant kernel vulnerabilities discovered in that interval. In 2009, major Linux vendors asked their customers to install a kernel update more than once per month.[10] For patches that do introduce semantic changes to data structures, Ksplice requires a programmer to write a short amount of additional code to help apply the patch. This was necessary for about 12% of the updates in that time period.[11]
History
[edit]The Ksplice software was created by four MIT students based on Jeff Arnold's master's thesis,[12] and they later created Ksplice, Inc. Around May 2009, the company won the MIT $100K Entrepreneurship Competition and the Cyber Security Challenge of Global Security Challenge.
Whereas the Ksplice software was provided under an open source license, Ksplice, Inc. provided a service to make it easier to use the software. Ksplice, Inc. provided prebuilt and tested updates for the Red Hat, CentOS, Debian, Ubuntu and Fedora Linux distributions.[13] The virtualization technologies OpenVZ and Virtuozzo were also supported. Updates for Ubuntu Desktop and Fedora systems were provided free of charge, whereas other platforms were offered on a subscription basis.[14]
On 21 July 2011, Oracle Corporation announced that they acquired Ksplice, Inc. At the time the company was acquired, Ksplice, Inc. claimed to have over 700 companies using the service to protect over 100,000 servers. While the service had been available for multiple Linux distributions, it was stated at the time of acquisition that "Oracle believes it will be the only enterprise Linux provider that can offer zero downtime updates." More explicitly, "Oracle does not plan to support the use of Ksplice technology with Red Hat Enterprise Linux."[7] Existing legacy customers continue to be supported by Ksplice, but no new customers are being accepted for other platforms.[15]
As of July 2015[update], Ksplice is available for free on Ubuntu Desktop.[8] In January 2016, Ksplice was integrated into Oracle's Unbreakable Enterprise Kernel Release 4 for Oracle Linux 6 and 7, which is Oracle's redistribution of Red Hat Enterprise Linux.[16]
As of March 2023, Ksplice is integrated into:
- Oracle's Unbreakable Enterprise Kernel Releases 5, 6 and 7, distributed with Oracle Linux 7, Oracle Linux 8 and Oracle Linux 9
- Red Hat Compatible Kernel releases distributed with Oracle Linux 7, Oracle Linux 8 and Oracle Linux 9
See also
[edit]- kexec, a method for loading a whole new kernel from a running system
- kGraft, kpatch and KernelCare, other Linux kernel live patching technologies developed by SUSE, Red Hat and CloudLinux, respectively
- Loadable kernel module
References
[edit]- ^ Arnold, Jeff (23 April 2008). "A system for rebootless kernel security updates". LKML (Mailing list). Archived from the original on 11 May 2012. Retrieved 27 July 2013.
- ^ a b "Ksplice Uptrack Subscription Agreement". ksplice.com. 28 September 2011. Retrieved 18 November 2014.
- ^ a b "ksplice 0.9.9.1 source code, README file". oss.oracle.com. 28 July 2011. Retrieved 31 December 2014.
This program is free software; you can redistribute it and/or modify it under the terms of the GNU General Public License, version 2.
- ^ "Ubuntu Manpage: ksplice-create – Create a set of kernel modules for a rebootless kernel". manpages.ubuntu.com. 2009. Retrieved 23 November 2014.
- ^ "Ksplice Users Guide: Available Architectures" (PDF). docs.oracle.com. 2023. Retrieved 22 March 2023.
- ^ "Free 30-day trial of Ksplice Zero-Downtime Updates for Red Hat Enterprise Linux Customers". Ksplice.
- ^ a b "Customer Letter Oracle and Ksplice". Oracle. 7 September 2010. Retrieved 22 July 2011.
- ^ a b "Oracle Ksplice Free Desktop Edition". Oracle Ksplice. Oracle. 16 July 2015. Retrieved 16 July 2015.
Oracle Ksplice is offered for free on Fedora and Ubuntu Desktop Editions.
- ^ a b c Jeff Arnold; M. Frans Kaashoek. "Ksplice: Automatic Rebootless Kernel Updates" (PDF). mit.edu. Retrieved 18 November 2014.
- ^ "Nexcess Adopts Ksplice Uptrack "Rebootless" Technology". Nexcess. 30 November 2010. Retrieved 18 February 2011.
- ^ "Performance record". Ksplice. Archived from the original on 16 April 2009. Retrieved 4 June 2009.
- ^ Edge, Jake (10 June 2009). "Ksplice provides updates without reboots". LWN. Retrieved 21 July 2011.
- ^ "Ksplice Uptrack". Ksplice. Retrieved 19 July 2009.
- ^ "Pricing". Ksplice, Inc. Retrieved 13 March 2011.
- ^ "Supported Kernels". Ksplice website. Oracle America. Retrieved 13 February 2012.
- ^ Marius Nestor (9 January 2016). "Oracle Brings Real-Time Kernel Patching to Its Unbreakable Enterprise Kernel Release 4". softpedia.com. Retrieved 9 January 2016.
