Wi-Fi
ur weak

Wi-Fi (Template:Pron-en) is a trademark of the Wi-Fi Alliance that manufacturers may use to brand certified products that belong to a class of wireless local area network (WLAN) devices based on the IEEE 802.11 standards. Because of the close relationship with its underlying standard, the term Wi-Fi is often used as a synonym for IEEE 802.11 technology.[1][2]
The Wi-Fi Alliance, a global association of companies, promotes WLAN technology and certifies products if they conform to certain standards of interoperability. Not every IEEE 802.11-compliant device is submitted for certification to the Wi-Fi Alliance, sometimes because of costs associated with the certification process. The lack of the Wi-Fi logo does not necessarily imply a device is incompatible with Wi-Fi devices.
As of 2010[update], IEEE 802.11 devices are installed in many personal computers, video game consoles, smartphones, printers, and other peripherals, and virtually all laptop or palm-sized computers.

Uses
Internet access

A Wi-Fi enabled device such as a personal computer, video game console, mobile phone, MP3 player or personal digital assistant can connect to the Internet when within range of a wireless network connected to the Internet. The coverage of one or more (interconnected) access points — called hotspots — can comprise an area as small as a few rooms or as large as many square miles. Coverage in the larger area may depend on a group of access points with overlapping coverage. Wi-Fi technology has been used in wireless mesh networks, for example, in London, UK.[3]
In addition to private use in homes and offices, Wi-Fi can provide public access at Wi-Fi hotspots provided either free-of-charge or to subscribers to various commercial services. Organizations and businesses - such as those running airports, hotels and restaurants - often provide free-use hotspots to attract or assist clients. Enthusiasts or authorities who wish to provide services or even to promote business in selected areas sometimes provide free Wi-Fi access. As of 2008[update] more than 300 metropolitan-wide Wi-Fi (Muni-Fi) projects had started.[4] As of May 2008[update] the Czech Republic had 879 Wi-Fi based Wireless Internet service providers.[5][6]
Routers that incorporate a digital subscriber line modem or a cable modem and a Wi-Fi access point, often set up in homes and other premises, can provide Internet-access and internetworking to all devices connected (wirelessly or by cable) to them. One can also connect Wi-Fi devices in ad-hoc mode for client-to-client connections without a router. Wi-Fi also connects places that would traditionally not have network access, for example bathrooms, kitchens and garden sheds.
City-wide Wi-Fi


In the early 2000s, many cities around the world announced plans for city-wide Wi-Fi networks. This proved to be much more difficult than their promoters initially envisioned with the result that most of these projects were either canceled or placed on indefinite hold. A few were successful, for example in 2005, Sunnyvale, California became the first city in the United States to offer city-wide free Wi-Fi.[7] (As of 2009[update] few of the Municipal Wi-Fi firms have entered the field of smart grid networks.[8][clarification needed])
In May, 2010, London, UK Mayor Boris Johnson pledged London-wide Wi-Fi by 2012.[9] Both the City of London, UK[10] and Islington [11] already have extensive outdoor Wi-Fi coverage.
Campus-wide Wi-Fi
Carnegie Mellon University built the first wireless Internet network in the world at their Pittsburgh campus in 1994,[12] long before Wi-Fi branding originated in 1999. Most campuses now have wireless Internet.
Direct computer-to-computer communications
Wi-Fi also allows communications directly from one computer to another without the involvement of an access point. This is called the ad-hoc mode of Wi-Fi transmission. This wireless ad-hoc network mode has proven popular with multiplayer handheld game consoles, such as the Nintendo DS, digital cameras, and other consumer electronics devices.
Similarly, the Wi-Fi Alliance promotes a pending specification called Wi-Fi Direct for file transfers and media sharing through a new discovery- and security-methodology.[13]
Future directions
As of 2010[update] Wi-Fi technology has spread widely within business and industrial sites. In business environments, just like other environments, increasing the number of Wi-Fi access points provides network redundancy, support for fast roaming and increased overall network-capacity by using more channels or by defining smaller cells. Wi-Fi enables wireless voice-applications (VoWLAN or WVOIP). Over the years, Wi-Fi implementations have moved toward "thin" access points, with more of the network intelligence housed in a centralized network appliance, relegating individual access points to the role of "dumb" transceivers. Outdoor applications may utilize mesh topologies. As of 2007 Wi-Fi installations can provide a secure computer networking gateway, firewall, DHCP server, intrusion detection system, and other functions.
History
Wi-Fi uses both single-carrier direct-sequence spread spectrum radio technology (part of the larger family of spread spectrum systems) and multi-carrier orthogonal frequency-division multiplexing (OFDM) radio technology. The deregulation of certain radio-frequencies[by whom?] for unlicensed spread spectrum deployment enabled the development of Wi-Fi products, Wi-Fi's onetime competitor HomeRF, Bluetooth, and many other products such as some types of cordless telephones.
In the US, the FCC first made unlicensed spread spectrum available in rules adopted on May 9, 1985.[14] Many other countries later copied or adapted these FCC regulations, enabling use of this technology in all major countries.[citation needed] The FCC action was proposed by Michael Marcus of the FCC staff in 1980 and the subsequent regulatory action took 5 more years. It was part of a broader proposal to allow civil use of spread spectrum technology and was opposed at the time by mainstream equipment manufacturers and many radio system operators.[15]
Wi-Fi technology has its origins in a 1985 ruling by the U.S. Federal Communications Commission that released several bands of the radio spectrum for unlicensed use.[16] In 1991 NCR Corporation/AT&T (later Lucent Technologies and Agere Systems) invented the precursor to 802.11 / Wi-Fi in Nieuwegein, the Netherlands. The inventors initially intended to use the technology for cashier systems; the first wireless products were brought on the market under the name WaveLAN with raw data rates of 1 Mbit/s and 2 Mbit/s. Vic Hayes, who held the chair of IEEE 802.11 for 10 years and has been called the "father of Wi-Fi" was involved in designing the initial 802.11b and 802.11a standards within the IEEE.
Europe leads overall in uptake of wireless-phone technology,[citation needed] but the US leads in Wi-Fi systems partly because it leads in laptop computer usage. As of July 2005, there were at least 68,643 Wi-Fi locations worldwide, a majority in the US, followed by the UK and Germany. The US and Western Europe have about 80% of the worldwide Wi-Fi users. Plans are underway in metropolitan areas of the US to provide free public Wi-Fi coverage. Even with these large numbers and more expansion, the extent of actual Wi-Fi usage is lower than expected. Jupiter Research found that only 15% of people have used Wi-Fi and only 6% in a public place.[17]
Wi-Fi certification
Wi-Fi technology builds on IEEE 802.11 standards. The IEEE develops and publishes these standards, but does not test equipment for compliance with them. The non-profit Wi-Fi Alliance formed in 1999 to fill this void — to establish and enforce standards for interoperability and backward compatibility, and to promote wireless local-area-network technology. As of 2009[update] the Wi-Fi Alliance consisted of more than 300 companies from around the world.[18][19] Manufacturers with membership in the Wi-Fi Alliance, whose products pass the certification process, gain the right to mark those products with the Wi-Fi logo.
Specifically, the certification process requires conformance to the IEEE 802.11 radio standards, the WPA and WPA2 security standards, and the EAP authentication standard. Certification may optionally include tests of IEEE 802.11 draft standards, interaction with cellular-phone technology in converged devices, and features relating to security set-up, multimedia, and power-saving.[20]
The Wi-Fi name
The term Wi-Fi suggests Wireless Fidelity, resembling the long-established audio-equipment classification term high fidelity (in use since the 1930s[21]) or Hi-Fi (used since 1950[22]). Even the Wi-Fi Alliance itself has often used the phrase Wireless Fidelity in its press releases[23][24] and documents;[25][26] the term also appears in a white paper on Wi-Fi from ITAA.[27] However, based on Phil Belanger's[28] statement, the term Wi-Fi was never supposed to mean anything at all.[29][30]
The term Wi-Fi, first used commercially in August 1999,[31] was coined by a brand-consulting firm called Interbrand Corporation that the Alliance had hired to determine a name that was "a little catchier than 'IEEE 802.11b Direct Sequence'".[32][29][30] Belanger also stated that Interbrand invented Wi-Fi as a play on words with Hi-Fi, and also created the yin-yang-style Wi-Fi logo.
The Wi-Fi Alliance initially used an advertising slogan for Wi-Fi, "The Standard for Wireless Fidelity",[29] but later removed the phrase from their marketing. Despite this, some documents from the Alliance dated 2003 and 2004 still contain the term Wireless Fidelity.[25][26] There was no official statement related to the dropping of the term.
The yin-yang logo indicates the certification of a product for interoperability.[25]
Advantages and challenges

Operational advantages
Wi-Fi allows the deployment of local area networks (LANs) without wires for client devices, typically reducing the costs of network deployment and expansion. Spaces where cables cannot be run, such as outdoor areas and historical buildings, can host wireless LANs.
As of 2010[update] manufacturers are building wireless network adapters into most laptops. The price of chipsets for Wi-Fi continues to drop, making it an economical networking option included in even more devices.[citation needed] Wi-Fi has become widespread in corporate infrastructures.[citation needed]
Different competitive brands of access points and client network-interfaces can inter-operate at a basic level of service. Products designated as "Wi-Fi Certified" by the Wi-Fi Alliance are backwards compatible. "Wi-Fi" designates a globally operative set of standards: unlike mobile phones, any standard Wi-Fi device will work anywhere in the world.
Wi-Fi operates in more than 220,000 public hotspots and in tens of millions of homes and corporate and university campuses worldwide.[33] The current version of Wi-Fi Protected Access encryption (WPA2) as of 2010[update] is considered[by whom?] secure, provided users employ a strong passphrase. New protocols for quality-of-service (WMM) make Wi-Fi more suitable for latency-sensitive applications (such as voice and video); and power saving mechanisms (WMM Power Save) improve battery operation.
Limitations
Spectrum assignments and operational limitations do not operate consistently worldwide. Most of Europe allows for an additional 2 channels beyond those permitted in the U.S. for the 2.4 GHz band. (1–13 vs. 1–11); Japan has one more on top of that (1–14). Europe, as of 2007[update], was essentially homogeneous in this respect. A very confusing aspect is the fact that a Wi-Fi signal actually occupies five channels in the 2.4 GHz band resulting in only three non-overlapped channels in the U.S.: 1, 6, 11, and three or four in Europe: 1, 5, 9, 13. Equivalent isotropically radiated power (EIRP) in the EU is limited to 20 dBm (100 mW).
Reach
Wi-Fi networks have limited range. A typical wireless router using 802.11b or 802.11g with a stock antenna might have a range of 32 m (120 ft) indoors and 95 m (300 ft) outdoors. The new IEEE 802.11n however, can exceed that range by more than two times.[citation needed] Range also varies with frequency band. Wi-Fi in the 2.4 GHz frequency block has slightly better range than Wi-Fi in the 5 GHz frequency block. Outdoor ranges - through use of directional antennas - can be improved with antennas located several kilometres or more from their base. In general, the maximum amount of power that a Wi-Fi device can transmit is limited by local regulations, such as FCC Part 15[34] in USA.
Wi-Fi performance decreases roughly quadratically[citation needed] as distance increases at constant radiation levels.
Due to reach requirements for wireless LAN applications, Wi-Fi has as fairly high power-consumption compared to some other standards. Technologies such as Bluetooth (designed to support wireless PAN applications) provide a much shorter propagation range of <10m[35] and so in general have a lower power-consumption. Other low-power technologies such as ZigBee have fairly long range, but much lower data rate. The high power-consumption of Wi-Fi makes battery life in mobile devices a concern.
Researchers have developed a number of "no new wires" technologies to provide alternatives to Wi-Fi for applications in which Wi-Fi's indoor range is not adequate and where installing new wires (such as CAT-5) is not possible or cost-effective. For example, the ITU-T G.hn standard for high speed Local area networks uses existing home wiring (coaxial cables, phone lines and power lines). Although G.hn does not provide some of the advantages of Wi-Fi (such as mobility or outdoor use), it's designed[by whom?] for applications (such as IPTV distribution) where indoor range is more important than mobility.
Due to the complex nature of radio propagation at typical Wi-Fi frequencies, particularly the effects of signal reflection off trees and buildings, algorithms can only approximately predict Wi-Fi signal strength for any given area in relation to a transmitter.[36] This effect does not apply equally to long-range Wi-Fi, since longer links typically operate from towers that broadcast above the surrounding foliage.
Mobility
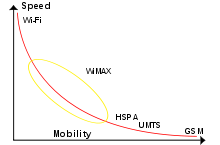
The very limited practical range of Wi-Fi essentially confines mobile use to such applications as inventory-taking machines in warehouses or in retail spaces, barcode-reading devices at check-out stands, or receiving/shipping stations. Mobile use of Wi-Fi over wider ranges is limited to move, use,[clarification needed] as for instance in an automobile moving from one hotspot to another (known as Wardriving). Other wireless technologies are more suitable as illustrated in the graphic.
Data security risks
The most common wireless encryption-standard, Wired Equivalent Privacy or WEP, has been shown to be easily breakable even when correctly configured. Wi-Fi Protected Access (WPA and WPA2) encryption, which became available in devices in 2003, aimed to solve this problem. Wi-Fi access points typically default to an encryption-free (open) mode. Novice users benefit from a zero-configuration device that works out-of-the-box, but this default does not enable any wireless security, providing open wireless access to a LAN. To turn security on requires the user to configure the device, usually via a software graphical user interface (GUI). On unencrypted Wi-Fi networks connecting devices can monitor and record data (including personal information), but such networks may use other means of protection, such as a virtual private network or secure Hypertext Transfer Protocol (HTTPS) and Transport Layer Security.
Population
Many 2.4 GHz 802.11b and 802.11g access-points default to the same channel on initial startup, contributing to congestion on certain channels. To change the channel of operation for an access point requires the user to configure the device.
Channel pollution
Market forces may drive a process of standardization. Interoperability issues between non-Wi-Fi brands or proprietary deviations from the standard can still disrupt connections or lower throughput speeds on all devices within range, including any non-Wi-Fi or proprietary product. Moreover, the usage of the ISM band in the 2.45 GHz range is also common to Bluetooth, WPAN-CSS, ZigBee, and any new system will take its share.
Wi-Fi pollution, or an excessive number of access points in the area, especially on the same or neighboring channel, can prevent access and interfere with other devices' use of other access points, caused by overlapping channels in the 802.11g/b spectrum, as well as with decreased signal-to-noise ratio (SNR) between access points. This can become a problem in high-density areas, such as large apartment complexes or office buildings with many Wi-Fi access points. Additionally, other devices use the 2.4 GHz band: microwave ovens, security cameras, ZigBee devices, Bluetooth devices and (in some countries) Amateur radio, video senders, cordless phones and baby monitors, all of which can cause significant additional interference. It is also an issue when municipalities[37] or other large entities (such as universities) seek to provide large area coverage. This openness is also important to the success and widespread use of 2.4 GHz Wi-Fi.
Hardware
Standard devices



A wireless access point (WAP) connects a group of wireless devices to an adjacent wired LAN. An access point resembles a network hub, relaying data between connected wireless devices in addition to a (usually) single connected wired device, most often an ethernet hub or switch, allowing wireless devices to communicate with other wired devices.
Wireless adapters allow devices to connect to a wireless network. These adapters connect to devices using various external or internal interconnects such as PCI, miniPCI, USB, ExpressCard, Cardbus and PC Card. As of 2010[update], most newer laptop computers come equipped with internal adapters. Internal cards are generally more difficult to install.
Wireless routers integrate a Wireless Access Point, ethernet switch, and internal router firmware application that provides IP routing, NAT, and DNS forwarding through an integrated WAN-interface. A wireless router allows wired and wireless ethernet LAN devices to connect to a (usually) single WAN device such as a cable modem or a DSL modem. A wireless router allows all three devices, mainly the access point and router, to be configured through one central utility. This utility is usually an integrated web server that is accessible to wired and wireless LAN clients and often optionally to WAN clients. This utility may also be an application that is run on a desktop computer such as Apple's AirPort.
Wireless network bridges connect a wired network to a wireless network. A bridge differs from an access point: an access point connects wireless devices to a wired network at the data-link layer. Two wireless bridges may be used to connect two wired networks over a wireless link, useful in situations where a wired connection may be unavailable, such as between two separate homes.
Wireless range-extenders or wireless repeaters can extend the range of an existing wireless network. Strategically placed range-extenders can elongate a signal area or allow for the signal area to reach around barriers such as those pertaining in L-shaped corridors. Wireless devices connected through repeaters will suffer from an increased latency for each hop. Additionally, a wireless device connected to any of the repeaters in the chain will have a throughput limited by the "weakest link" between the two nodes in the chain from which the connection originates to where the connection ends.
Distance records
Distance records (using non-standard devices) include 382 km (237 mi) in June 2007, held by Ermanno Pietrosemoli and EsLaRed of Venezuela, transferring about 3 MB of data between the mountain-tops of El Águila and Platillon.[38][39] The Swedish Space Agency transferred data 310 km (193 mi), using 6 watt amplifiers to reach an overhead stratospheric balloon.[40]
Embedded systems

Increasingly in the last few years (particularly as of 2007[update]), embedded Wi-Fi modules have become available that incorporate a real-time operating system and provide a simple means of wirelessly enabling any device which has and communicates via a serial port.[41] This allows the design of simple monitoring devices. An example is a portable ECG device monitoring a patient at home. This Wi-Fi-enabled device can communicate via the Internet. [42]
These Wi-Fi modules are designed[by whom?] so that implementers need only minimal Wi-Fi knowledge to provide Wi-Fi connectivity for their products.
Network security
The main issue with wireless network security is its simplified access to the network compared to traditional wired networks such as ethernet.[citation needed] With wired networking one must either gain access to a building (physically connecting into the internal network) or break through an external firewall. Most business networks protect sensitive data and systems by attempting to disallow external access. Thus gaining wireless connectivity provides an attack vector, particularly if the network lacks encryption or if the intruder can defeat any encryption.[43]
Attackers who have gained access to a Wi-Fi network can use DNS spoofing attacks very effectively against any other user of the network, because they can see the DNS requests made, and often respond with a spoofed answer before the queried DNS server has a chance to reply.[44]
Securing methods
A common but unproductive measure to deter unauthorized users involves suppressing the access point's SSID broadcast, "hiding" it. This is ineffective as a security method because the SSID is broadcast in the clear in response to a client SSID query. Another unproductive method is to only allow computers with known MAC addresses to join the network.[45] But intruders can defeat this method because they can often (though not always) set MAC addresses with minimal effort (MAC spoofing). If eavesdroppers have the ability to change their MAC address, then they may join the network by spoofing an authorized address.
Wired Equivalent Privacy (WEP) encryption was designed[by whom?] to protect against casual snooping, but is now deprecated. Tools such as AirSnort or Aircrack-ng can quickly recover WEP encryption keys. Once it has seen 5-10 million encrypted packets, AirSnort can determine the encryption password in under a second;[46] newer tools such as aircrack-ptw can use Klein's attack to crack a WEP key with a 50% success rate using only 40,000 packets.
To counteract this in 2002, the Wi-Fi Alliance approved Wi-Fi Protected Access (WPA) which uses TKIP as a stopgap solution for legacy equipment. Though more secure than WEP, it has outlived its designed lifetime and has known attack vectors.
In 2004, the IEEE ratified the full IEEE 802.11i (WPA2) encryption standards. If used with a 802.1X server or in pre-shared key mode with a strong and uncommon passphrase WPA2 is still considered[by whom?] secure, as of 2009[update].
Piggybacking
Piggybacking refers to access to a wireless Internet connection by bringing one's own computer within the range of another's wireless connection, and using that service without the subscriber's explicit permission or knowledge.
During the early popular adoption of 802.11, providing open access points for anyone within range to use was encouraged[by whom?] to cultivate wireless community networks,[47] particularly since people on average use only a fraction of their downstream bandwidth at any given time.
Recreational logging and mapping of other people's access points has become known as wardriving. It is also common for people to use open (unencrypted) Wi-Fi networks as a free service, termed piggybacking. Indeed, many access points are intentionally installed without security turned on so that they can be used as a free service. Providing access to one's Internet connection in this fashion may breach the Terms of Service or contract with the ISP. These activities do not result in sanctions in most jurisdictions; however, legislation and case law differ considerably across the world. A proposal to leave graffiti describing available services was called[by whom?] warchalking. A Florida court case determined that owner laziness was not to be a valid excuse.[48]
Piggybacking often occurs unintentionally, most access points are configured[by whom?] without encryption by default, and operating systems such as Windows XP SP2, Mac OS X or Ubuntu Linux may be configured to automatically connect to any available wireless network. A user who happens to start up a laptop in the vicinity of an access point may find the computer has joined the network without any visible indication. Moreover, a user intending to join one network may instead end up on another one if the latter has a stronger signal. In combination with automatic discovery of other network resources (see DHCP and Zeroconf) this could possibly lead wireless users to send sensitive data to the wrong middle-man when seeking a destination (see Man-in-the-middle attack). For example, a user could inadvertently use an insecure network to log in to a website, thereby making the login credentials available to anyone listening, if the website uses an insecure protocol such as HTTP.
See also
- List of WLAN channels
- San Francisco Digital Inclusion Strategy
- Wi-Fi operating system support
- WiMAX
- Wireless electronic devices and health
References
- ^ "Wi-Fi".
- ^ "Basic Facts About Wi-Fi and its Advancement".
- ^ "Switch on for Square Mile wi-fi". news.bbc.co.uk. 2007-04-23. Retrieved 2007-11-08.
- ^ "MuniWireless » City Initiatives Directory". www.muniwireless.com. Retrieved 2008-03-12.
- ^ "Wi-Fi: Poskytovatelé bezdrátového připojení". internetprovsechny.cz. Retrieved 2008-03-17.
- ^ "Bezdrátové připojení k internetu". bezdratovepripojeni.cz. Retrieved 2008-05-18.
- ^ "Sunnyvale Uses MetroFi". unstrung.com. Retrieved 2008-07-16.
- ^ "Muni Wi-Fi Firms Find New Life In Smart Grid". GigaOm.
- ^ "London-wide wi-fi by 2012 pledge". BBC News. 2010-05-19. Retrieved 2010-05-19.
- ^ "City of London Fires Up Europe's Most Advanced Wi-Fi Network". www.govtech.com. Retrieved 2007-05-14.
- ^ "London gets a mile of free Wi-Fi". .zdnet.co.uk. Retrieved 200-04-18.
{{cite news}}: Check date values in:|accessdate=(help) - ^ "Wi-Fi Origins". Retrieved 2008-07-16.
- ^ "Wi-Fi Direct allows device-to-device links".
- ^ "Authorization of Spread Spectrum Systems Under Parts 15 and 90 of the FCC Rules and Regulations" (TXT). Federal Communications Commission. June 18, 1985. Retrieved 2007-08-31.
- ^ "The Genesis of Unlicensed Wireless Policy". George Mason University. April 4, 2008. Retrieved 2008-04-20.
- ^ "http://www.britannica.com/EBchecked/topic/1473553/Wi-Fi" (TXT). Encyclopædia Britannica. Retrieved 2010-02-3.
{{cite web}}: Check date values in:|accessdate=(help); External link in|title= - ^ Castells, Manuel, Mireia Fernández- Ardévol, Jack Qiu, and Araba Sey. Mobile Communication and Society. Cambridge, MA: MIT Press, 2007. 27-28. Print.
- ^ "Wi-Fi Alliance: Organization". www.wi-fi.org. Retrieved 2009-10-22.
- ^ "Wi-Fi Alliance: White Papers". www.wi-fi.org. Retrieved 2009-10-22.
- ^ "Wi-Fi Alliance: Programs". www.wi-fi.org. Retrieved 2009-10-22.
- ^ Oxford English Dictionary (2 ed.). Oxford: Oxford University Press. 1989. ISBN 0198611862.
- ^ Oxford English Dictionary (2 ed.). Oxford: Oxford University Press. 1989. ISBN 0198611862.
- ^ "Wireless Ethernet Compatibility Alliance (WECA) Awards New Wi-Fi Interoperability Certification". Wi-Fi Alliance. 2000-05-08. Retrieved 2009-11-30.
- ^ "Six Wi-Fi Interoperability Certifications Awarded By The Wireless Ethernet Compatibility Alliance (WECA)". Wi-Fi Alliance. 2000-07-19. Retrieved 2009-11-30.
- ^ a b c "Securing Wi-Fi Wireless Networks with Today's Technologies" (PDF). Wi-Fi Alliance. 2003-02-06. Retrieved 2009-11-30.
- ^ a b "WPA™ Deployment Guidelines for Public Access Wi-Fi® Networks" (PDF). Wi-Fi Alliance. 2004-10-28. Retrieved 2009-11-30.
- ^ "Wireless Fidelity (WiFi) Technology" (PDF). ITAA. January 2004. Retrieved 2009-11-30.
- ^ Phil Belanger is the founding member of the Wi-Fi Alliance
- ^ a b c
"WiFi isn't short for "Wireless Fidelity"". boingboing.net. Retrieved 2007-08-31.
{{cite web}}: Unknown parameter|data=ignored (|date=suggested) (help) - ^ a b "Wireless Fidelity' Debunked". Wi-Fi Planet. 2007-04-27. Retrieved 2007-08-31.
- ^ U.S. Patent and Trademark Office.
- ^ "What is the True Meaning of Wi-Fi?". Teleclick. Retrieved 2007-08-31.
- ^ "Wi-Fi Finder". jiwire.com. Retrieved 2008-04-20.
- ^ FCC Sec.15.249 Operation within the bands 902–928 MHz, 2400–2483.5 MHz, 5725–5875 MHZ, and 24.0–24.25 GHz.
- ^ See for example IEEE Standard 802.15.4 section 1.2 scope
- ^ "WiFi Mapping Software: Footprint". Alyrica Networks, Inc. Retrieved 2008-04-27.
- ^ Wilson, Tracy V. "How Municipal WiFi Works". computer.howstuffworks.com. Retrieved 2008-03-12.
- ^ "Ermanno Pietrosemoli has set a new record for the longest communication Wi-Fi link". Retrieved 2008-03-10.
- ^ "Wireless technology is irreplaceable for providing access in remote and scarcely populated regions". Retrieved 2008-03-10.
- ^ "Long Distance WiFi Trial" (PDF). Retrieved 2008-03-10.
- ^ "Quatech Rolls Out Airborne Embedded 802.11 Radio for M2M Market". Retrieved 2008-04-29.
- ^ "CIE article on embedded WiFi for M2M applications". Retrieved 2008-08-27.
- ^ "802.11 X Wireless Network in a Business Environment -- Pros and Cons". NetworkBits.net. Retrieved 2008-04-08.
- ^
Bernstein, Daniel J. (2002). "DNS forgery". Retrieved 2010-03-24.
An attacker with access to your network can easily forge responses to your computer's DNS requests.
{{cite web}}: Cite has empty unknown parameter:|month=(help) - ^ Mateti, Prabhaker (2005). "Hacking Techniques in Wireless Networks". Dayton, Ohio: Department of Computer Science and Engineering Wright State University. Retrieved 2010-02-28.
- ^ "Wireless Vulnerabilities & Exploits". wirelessve.org. Retrieved 2008-04-15.
- ^ NoCat's goal is to bring you Infinite Bandwidth Everywhere for Free
- ^ See the wikinews article mentioned in this section.
Further reading
- Wireless Networking in the Developing World (PDF book)
External links
