Double Ratchet Algorithm
In cryptography, the Double Ratchet Algorithm (previously referred to as the Axolotl Ratchet[1][2]) is a key management algorithm that was developed by Trevor Perrin and Moxie Marlinspike in 2013. It can be used as part of a cryptographic protocol to provide end-to-end encryption for instant messaging. After an initial key exchange it manages the ongoing renewal and maintenance of short-lived session keys. It combines a cryptographic ratchet based on the Diffie–Hellman key exchange (DH) and a ratchet based on a key derivation function (KDF) like e.g. a hash function and is therefore called a double ratchet.
The developers refer to the algorithm as self-healing because it automatically disables an attacker from accessing the cleartext of later messages after having compromised a session key.[3]
Origin
The Double Ratchet Algorithm was developed by Trevor Perrin and Moxie Marlinspike (Open Whisper Systems) in 2013 and introduced as part of the Signal Protocol in February 2014. The Double Ratchet Algorithm's design is based on the DH ratchet that was introduced by Off-the-Record Messaging and combines it with a symmetric-key ratchet modeled after the Silent Circle Instant Messaging Protocol (SCIMP). The ratchet was initially named after the critically endangered aquatic salamander Axolotl, which has extraordinary self-healing capabilities. In March 2016, the developers renamed the Axolotl Ratchet as the Double Ratchet Algorithm to better differentiate between the ratchet and the full protocol,[2] because some had used the name Axolotl when referring to the Signal Protocol.[4][2]
Properties
The Double Ratchet Algorithm features properties that have been commonly available in end-to-end encryption systems for a long time: encryption of contents on the entire way of transport as well as authentication of the remote peer and protection against manipulation of messages. As a hybrid of DH and KDF ratchets, it combines several desired features of both principles. From OTR messaging it takes the properties of forward secrecy and automatically reestablishing secrecy in case of compromise of a session key, forward secrecy with a compromise of the secret persistent main key, and plausible deniability for the authorship of messages. Additionally, it enables session key renewal without interaction with the remote peer by using secondary KDF ratchets. An additional key-derivation step is taken to enable retaining session keys for out-of-order messages without endangering the following keys.
It is said to detect reordering, deletion and replay of sent messages and improve forward secrecy properties in comparison to OTR messaging.
Combined with public key infrastructure for the retention of pregenerated one-time keys (prekeys), it allows for the initialization of messaging sessions without the presence of the remote peer (asynchronous communication). The usage of triple Diffie–Hellman key exchange (3-DH) as initial key exchange method improves the deniability properties. An example of this is the Signal Protocol, which combines the Double Ratchet Algorithm, prekeys, and a 3-DH handshake.[5] The protocol provides confidentiality, integrity, authentication, participant consistency, destination validation, forward secrecy, backward secrecy (aka future secrecy), causality preservation, message unlinkability, message repudiation, participation repudiation, and asynchronicity.[6] It does not provide anonymity preservation, and requires servers for the relaying of messages and storing of public key material.[6]
Functioning
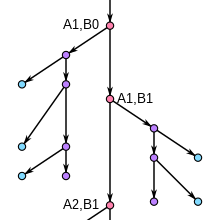
A client renews session key material in interaction with the remote peer using Diffie–Hellman ratchet whenever possible, otherwise independently by using a hash ratchet. Therefore, with every message a client using the double ratchet advances one of two hash ratchets (one for sending, one receiving) which get seeded with a common secret from a DH ratchet. At the same time it tries to use every opportunity to provide the remote peer with a new public DH value and advance the DH ratchet whenever a new DH value from the remote peer arrives. As soon as a new common secret is established, a new hash ratchet gets initialized.
As cryptographic primitives, the Double Ratchet Algorithm uses
- for the DH ratchet
- Elliptic curve Diffie–Hellman (ECDH) with Curve25519,
- for message authentication codes (MAC, authentication)
- Keyed-Hash Message Authentication Code (HMAC) based on SHA-256,
- for symmetric encryption
- the Advanced Encryption Standard (AES), partially in Cipher Block Chaining mode (CBC) with padding as per PKCS #5 and partially in Counter mode (CTR) without padding,
- for the hash ratchet
- HMAC.[7]
Usage
The following is a list of cryptographic protocols that use the Double Ratchet Algorithm or a custom implementation of it:
- Matrix, an open protocol for real-time communication. It includes Olm, a library that provides for optional end-to-end encryption on a room-by-room basis via a Double Ratchet Algorithm implementation. Matrix is used in:
- OMEMO, an extension to XMPP. It is used in:
- Conversations
- Gajim as a third-party plug-in that must be installed separately
- Cryptocat[9]
- Proteus, a protocol developed by Wire Swiss based on the Signal Protocol,[10] and used in the company's instant messaging app Wire.[11]
- Signal Protocol, which combines the Double Ratchet Algorithm, prekeys, and a 3-DH handshake.[5] It is used in:
- Facebook Messenger, which features an optional mode that uses the Signal Protocol.[12]
- Google Allo, which also features an optional mode that uses the Signal Protocol.[13]
- G Data's Secure Chat[14][15]
- Signal
- WhatsApp[16]
Other:
- In November 2013, the Double Ratchet Algorithm was integrated into an experimental asynchronous messaging system called Pond.[17]
- In May 2016, Viber said that their encryption protocol is a custom implementation that "uses the same concepts" as the Signal Protocol.[18]
References
- ^ Perrin, Trevor (30 March 2016). "Compare Revisions". GitHub. Retrieved 9 April 2016.
- ^ a b c Marlinspike, Moxie (30 March 2016). "Signal on the outside, Signal on the inside". Open Whisper Systems. Retrieved 31 March 2016.
- ^ Marlinspike, Moxie (26 November 2013). "Advanced cryptographic ratcheting". whispersystems.org. Open Whisper Systems. Retrieved 16 January 2016.
The OTR style ratchet has the nice property of being 'self healing.'
- ^ Cohn-Gordon et al. 2016, p. 1
- ^ a b Unger et al. 2015, p. 241
- ^ a b Unger et al. 2015, p. 239
- ^ Frosch et al. 2014
- ^ Butcher, Mike (19 September 2016). "Riot wants to be like Slack, but with the flexibility of an underlying open source platform". TechCrunch. AOL Inc. Retrieved 20 September 2016.
- ^ "Security". Cryptocat. Retrieved 14 July 2016.
- ^ "Add attribution". GitHub. Wire Swiss GmbH. 9 May 2016. Retrieved 15 July 2016.
- ^ "Wire Security Whitepaper". Wire Swiss GmbH. Retrieved 15 July 2016.
- ^ Greenberg, Andy (4 October 2016). "You Can All Finally Encrypt Facebook Messenger, So Do It". Wired. Condé Nast. Retrieved 5 October 2016.
- ^ Greenberg, Andy (18 May 2016). "With Allo and Duo, Google Finally Encrypts Conversations End-to-End". Wired. Condé Nast. Retrieved 14 July 2016.
- ^ Seals, Tara (17 September 2015). "G DATA Adds Encryption for Secure Mobile Chat". Infosecurity Magazine. Reed Exhibitions Ltd. Retrieved 16 January 2016.
- ^ "SecureChat". GitHub. G Data. Retrieved 14 July 2016.
- ^ Metz, Cade (5 April 2016). "Forget Apple vs. the FBI: WhatsApp Just Switched on Encryption for a Billion People". Wired. Condé Nast. Retrieved 5 April 2016.
- ^ Langley, Adam (9 November 2013). "Wire in new ratchet system". GitHub (GitHub contribution). Retrieved 16 January 2016.
- ^ "Viber Encryption Overview". Viber. 3 May 2016. Retrieved 14 July 2016.
Literature
- Cohn-Gordon, Katriel; Cremers, Cas; Dowling, Benjamin; Garratt, Luke; Stebila, Douglas (25 October 2016). "A Formal Security Analysis of the Signal Messaging Protocol" (PDF). Cryptology ePrint Archive. International Association for Cryptologic Research (IACR).
{{cite web}}: CS1 maint: ref duplicates default (link) - Frosch, Tilman; Mainka, Christian; Bader, Christoph; Bergsma, Florian; Schwenk, Jörg; Holz, Thorsten (2014). "How Secure is TextSecure?" (PDF). Cryptology ePrint Archive. International Association for Cryptologic Research (IACR). Retrieved 16 January 2016.
{{cite web}}: CS1 maint: ref duplicates default (link) - Unger, Nik; Dechand, Sergej; Bonneau, Joseph; Fahl, Sascha; Perl, Henning; Goldberg, Ian Avrum; Smith, Matthew (2015). SoK: Secure Messaging (PDF). Proceedings of the 2015 IEEE Symposium on Security and Privacy. IEEE Computer Society's Technical Committee on Security and Privacy. pp. 232–249. doi:10.1109/SP.2015.22.
{{cite conference}}: CS1 maint: ref duplicates default (link)
External links
- Specification
- "Advanced cryptographic ratcheting", abstract description by Moxie Marlinspike