2010s global surveillance disclosures: Difference between revisions
Wikiuser13 (talk | contribs) m clean up using AWB |
→External links: - Link added |
||
| Line 655: | Line 655: | ||
*{{cite web|url=http://g1.globo.com/fantastico/noticia/2013/09/veja-os-documentos-ultrassecretos-que-comprovam-espionagem-dilma.html|language=Portuguese|title =Veja os documentos ultrassecretos que comprovam espionagem a Dilma|date=September 2, 2013|accessdate=September 4, 2013}} Documents relating to the surveillance against [[Dilma Roussef]] and [[Enrique Peña Nieto]] |
*{{cite web|url=http://g1.globo.com/fantastico/noticia/2013/09/veja-os-documentos-ultrassecretos-que-comprovam-espionagem-dilma.html|language=Portuguese|title =Veja os documentos ultrassecretos que comprovam espionagem a Dilma|date=September 2, 2013|accessdate=September 4, 2013}} Documents relating to the surveillance against [[Dilma Roussef]] and [[Enrique Peña Nieto]] |
||
* [http://www.theguardian.com/world/2013/sep/05/nsa-how-to-remain-secure-surveillance NSA surveillance: A guide to staying secure - The NSA has huge capabilities – and if it wants in to your computer, it's in. With that in mind, here are five ways to stay safe] by The Guardian's Bruce Schneier on September 5, 2013. |
* [http://www.theguardian.com/world/2013/sep/05/nsa-how-to-remain-secure-surveillance NSA surveillance: A guide to staying secure - The NSA has huge capabilities – and if it wants in to your computer, it's in. With that in mind, here are five ways to stay safe] by The Guardian's Bruce Schneier on September 5, 2013. |
||
* [http://www.youtube.com/watch?v=9IjtsED5Iy8&sns=em 2014-01-04 Al Jazeera's "Listening Post - The Snowden saga: Spies, secrets and security - A look back at the biggest media story of 2013 - Edward Snowden and the NSA surveillance programme." which in its first part of the broadcast retells the global surveillance in the year 2013 and in its second part shows an interview former NSA general counsel Stewart Baker.] |
|||
<!-- backup on https://pad.lqdn.fr/p/2013%20mass%20surveillance%20disclosures & https://pad.arn-fai.net/p/ChDx63Y54V --> |
<!-- backup on https://pad.lqdn.fr/p/2013%20mass%20surveillance%20disclosures & https://pad.arn-fai.net/p/ChDx63Y54V --> |
||
Revision as of 18:13, 6 January 2014
This article documents a current event. Information may change rapidly as the event progresses, and initial news reports may be unreliable. The latest updates to this article may not reflect the most current information. (January 2014) |
| Part of a series on |
| Global surveillance |
|---|
| Disclosures |
| Systems |
| Agencies |
| Places |
| Laws |
| Proposed changes |
| Concepts |
| Related topics |
Ongoing news reports in the international media have revealed operational details about the U.S. National Security Agency (NSA) and its international partners' global surveillance[1] of foreign nationals and U.S. citizens. The vast majority of reports emanated from a cache of top secret documents leaked by ex-NSA contractor Edward Snowden. In June 2013, the first of Snowden's documents were published simultaneously by The Washington Post and The Guardian, attracting considerable public attention.[2] The disclosure continued throughout the entire year of 2013, and a significant portion of the full cache of 1.5 million documents[3] was later obtained and published by many other media outlets worldwide, most notably the Australian Broadcasting Corporation (Australia), O Globo (Brazil), the Canadian Broadcasting Corporation (Canada), Le Monde (France), Der Spiegel (Germany), L'espresso (Italy), NRC Handelsblad (the Netherlands), Dagbladet (Norway), El País (Spain), Sveriges Television (Sweden), and The New York Times (USA).[4]
In summary, these media reports have shed light on the implications of several secret treaties signed by members of the UKUSA Agreement in their efforts to implement global surveillance. For example, Der Spiegel revealed how the German Bundesnachrichtendienst (BND) transfers "massive amounts of intercepted data to the NSA",[5] while Sveriges Television revealed that the Försvarets radioanstalt (FRA) of Sweden is continuously providing the NSA with intercepted data gathered from telecom cables, under a secret treaty signed in 1954 for bilateral cooperation on surveillance.[6] Other security and intelligence agencies involved in the practice of global surveillance include those in Australia (ASD), Britain (GCHQ), Canada (CSEC), Denmark (PET), France (DGSE), Germany (BND), Italy (AISE), the Netherlands (AIVD), Norway (NIS), Spain (CNI), Switzerland (NDB), as well as Israel (ISNU), which receives raw, unfiltered data of U.S. citizens that is shared by the NSA.[7][8][9][10][11][12][13][14]
The disclosure provided impetus for the creation of social movements against mass surveillance, such as Restore the Fourth. Domestic spying programs in countries such as France, the UK, and India have also been exposed. On the legal front, the Electronic Frontier Foundation joined a coalition of diverse groups filing suit against the NSA. Several human rights organizations have urged the Obama administration not to prosecute, but protect, "whistleblower Snowden": Amnesty International, Human Rights Watch, Transparency International, and the Index on Censorship, inter alia.[15][16][17][18]
On June 14, 2013, United States prosecutors charged Edward Snowden with espionage and theft of government property.[19] In late July 2013, he was granted asylum by the Russian government,[20] contributing to a deterioration of Russia–United States relations.[21][22] On August 6, 2013, President Obama made a public appearance on national television where he reassured Americans that "We don't have a domestic spying program" and "There is no spying on Americans".[23] Towards the end of October 2013, the British Prime Minister David Cameron warned The Guardian not to publish any more leaks, or it will receive a DA-Notice.[24] Currently, a criminal investigation of the disclosure is being undertaken by Britain's Metropolitan Police Service.[25] In December 2013, The Guardian editor Alan Rusbridger said: "We have published I think 26 documents so far out of the 58,000 we've seen."[26]
Overview
Barton Gellman, a Pulitzer Prize-winning journalist who led The Washington Post's coverage of Snowden's disclosures, summarized the leaks as follows:
"Taken together, the revelations have brought to light a global surveillance system that cast off many of its historical restraints after the attacks of Sept. 11, 2001. Secret legal authorities empowered the NSA to sweep in the telephone, Internet and location records of whole populations."
The disclosure revealed specific details of the NSA's close cooperation with U.S. federal agencies such as the Federal Bureau of Investigation (FBI)[28][29] and the Central Intelligence Agency (CIA)[30][31] in addition to the agency's previously undisclosed financial payments to numerous commercial partners and telecommunications companies,[32][33][34] as well as its previously undisclosed relationships with international partners such as Britain,[35][36] France[12][37] Germany,[5][38] and its secret treaties with foreign governments that were recently established for sharing intercepted data of each other's citizens.[7][39][40][41]
Global surveillance
| Global surveillance programs | |||
|---|---|---|---|
| Program | International contributors and/or partners | Commercial partners | |
|
|||
|
|||
|
| ||
|
|||
|
|||
| Stateroom | |||
| Lustre |
|
||
Last updated: December 2013
Historical context
In the 1970s, NSA analyst Perry Fellwock (under the pseudonym "Winslow Peck") revealed the existence of the UKUSA Agreement,[61] which forms the basis of the ECHELON network, whose existence was revealed in 1988 by Lockheed employee Margaret Newsham.[62] Months before the September 11 attacks and during its aftermath, further details of the global surveillance apparatus were provided by ex-MI5 official David Shayler,[63] followed by James Bashford in 2001,[64] William Binney and colleagues in 2002,[65] Katharine Gun in 2003,[66] Clare Short in 2004,[67] journalists Eric Lichtblau and James Risen in 2005,[68] Leslie Cauley of USA Today in 2006,[69] Mark Klein in 2006,[70] Russ Tice in 2006,[71] Thomas Andrews Drake in 2010,[72] Julian Assange and Chelsea Manning in 2011,[73] and Michael Hastings in 2012.[74]
Timeline

- 2012
In April 2012, Edward Snowden began downloading sensitive NSA material while working for the American computer corporation Dell.[76] By the end of the year, Snowden had made his first contact with journalist Glenn Greenwald of The Guardian.[77]
- January–May 2013
In January 2013, Snowden contacted documentary filmmaker Laura Poitras.[78] In March 2013, Snowden took up a new job at Booz Allen Hamilton in Hawaii, specifically to gain access to additional top-secret documents that could be leaked.[76] In April 2013, Poitras asked Greenwald to meet her in New York City.[77] In May 2013, Snowden was permitted temporary leave from his position at the NSA in Hawaii, on the pretext of receiving treatment for his epilepsy.[79] Towards the end of May, Snowden flew to Hong Kong.[80]
2013
June
After the U.S.-based editor of The Guardian held several meetings in New York City, it was decided that Greenwald, Poitras and Ewen MacAskill would fly to Hong Kong to meet Snowden. On June 5, in the first media report based on the leaked material,[81] the Guardian exposed a top secret court order showing that the NSA had collected phone records from over 120 million Verizon subscribers.[82] Under the order, the numbers of both parties on a call, as well as the location data, unique identifiers, time of call, and duration of call were handed over to the FBI, which turned over the records to the NSA.[82]
On June 6, 2013, the second media disclosure was published simultaneously by Greenwald (The Guardian) and Poitras (The Washington Post).[75][83]
Documents provided by Edward Snowden and seen by Der Spiegel revealed how the NSA spied on various diplomatic missions of the European Union (EU), including the EU's delegation to the United States in Washington D.C.,[84] the EU's delegation to the United Nations in New York,[84] the Council of the European Union in Brussels,[84] and the United Nations Headquarters in New York.[85] During specific episodes within a four-year period, the NSA hacked several Chinese mobile-phone companies,[86] the Chinese University of Hong Kong and Tsinghua University in Beijing,[87] and the Asian fiber-optic network operator Pacnet.[88] Only Australia, Canada, New Zealand and the UK are explicitly exempted from NSA attacks, whose main target in the EU is Germany.[89] A method of bugging encrypted fax machines used at an EU embassy is codenamed Dropmire.[90]
During the 2009 G-20 London summit, the British intelligence agency Government Communications Headquarters (GCHQ) intercepted the communications of foreign diplomats.[91] In addition, the GCHQ has been intercepting and storing mass quantities of fiber-optic traffic via Tempora.[92] Two principal components of Tempora are called "Mastering the Internet" (MTI) and "Global Telecoms Exploitation".[93] The data is preserved for three days while metadata is kept for thirty days.[94] Data collected by the GCHQ under Tempora is shared with the National Security Agency (NSA) of the United States.[93]
The Guardian also revealed the existence of XKeyscore, which allows government analysts to search through vast databases containing emails, online chats and the browsing histories of millions of individuals without prior authorization.[95][96][97] Microsoft "developed a surveillance capability to deal" with the interception of encrypted chats on Outlook.com, within five months after the service went into testing. NSA had access to Outlook.com emails because “Prism collects this data prior to encryption.”[45]
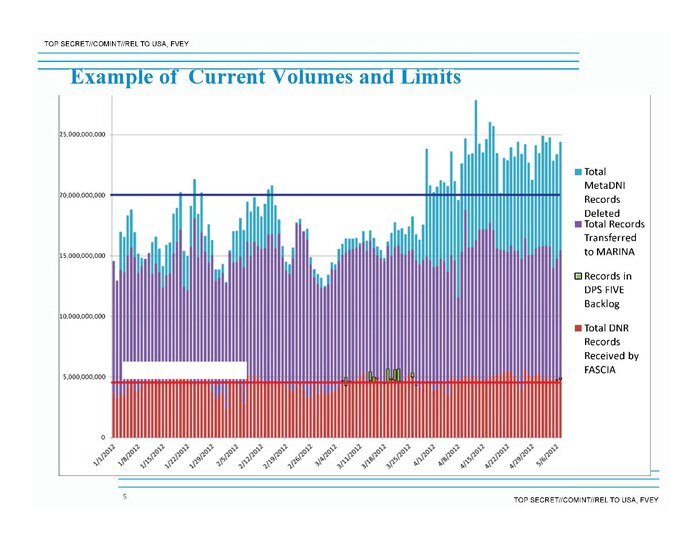
From 2001 to 2011, the NSA collected vast amounts of metadata records detailing the email and internet usage of Americans via Stellar Wind,[98] which was later terminated due to operational and resource constraints. It was subsequently replaced by newer surveillance programs such as ShellTrumpet, which "processed its one trillionth metadata record" by the end of December 2012.[99]
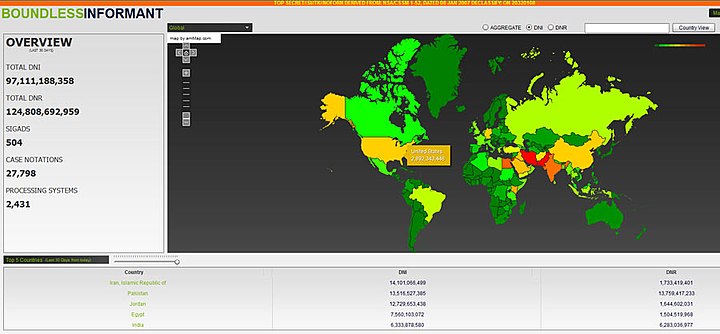
According to the Boundless Informant, over 97 billion pieces of intelligence were collected over a 30-day period ending in March 2013. Out of all 97 billion sets of information, about 3 billion data sets originated from U.S. computer networks[100] and around 500 million metadata records were collected from German networks.[101]
Several weeks later, it was revealed that the Bundesnachrichtendienst (BND) of Germany transfers massive amounts of metadata records to the NSA.[102]
July
According to the Brazilian newspaper O Globo, the NSA spied on millions of emails and calls of Brazilian citizens,[103][104] while Australia and New Zealand have been aiding the United States in their surveillance program.[105][106]
The NSA gave the German intelligence agencies BND and BfV access to X-Keyscore.[107] In return, the BND turned over copies of two systems named Mira4 and Veras, reported to exceed the NSA's SIGINT capabilities in certain areas.[108] The NSA also provided the BND with analysis tools so that the BND can monitor foreign data streams flowing through Germany.[109][110]
Even if there is no reason to suspect U.S. citizens the CIA's National Counterterrorism Center is allowed to examine the government files of for possible criminal behavior. Previously the NTC was barred to do so, unless a person was a terror suspect or related to an investigation.[111]
Snowden also confirmed that Stuxnet was cooperatively developed by the United States and Israel.[112] In a report unrelated to Edward Snowden, the French newspaper Le Monde revealed thet France's DGSE was also undertaking mass surveillance, which it described as "illegal and outside any serious control".[113][114]
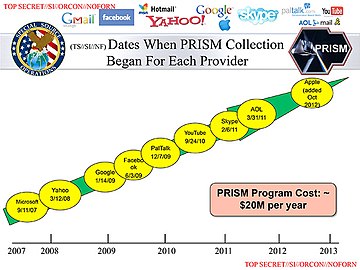
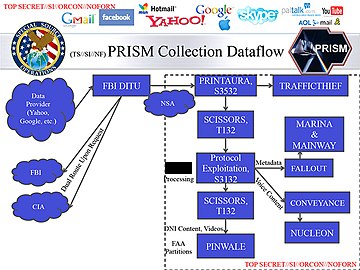
1. Upstream – Under the first type of collection, data en route to its final destination would be intercepted via FAIRVIEW, STORMBREW, BLARNEY, and OAKSTAR 2. PRISM – Under the second type of collection, data that has already reached its final destination would be directly harvested from the servers of the following U.S. service providers: Microsoft, Yahoo!, Google, Facebook, Paltalk, AOL, Skype, YouTube, and Apple Inc.
August
Documents leaked by Edward Snowden and jointly disclosed by Süddeutsche Zeitung (SZ) and Norddeutscher Rundfunk revealed that several telecom operators have played a key role in helping the British intelligence agency Government Communications Headquarters (GCHQ) tap into worldwide fiber-optic communications.[115][116] The telecom operators are:
- Verizon Business (codenamed "Dacron")[51][117]
- British Telecommunications (codenamed "Remedy")[51][117]
- Vodafone Cable (codenamed "Gerontic")[51][117]
- Global Crossing (codenamed "Pinnage")[51][117]
- Level 3 (codenamed "Little")[51][117]
- Viatel (codenamed "Vitreous")[51][117]
- Interoute (codenamed "Streetcar")[51][117]
Each of them were assigned a particular area of the international fiber-optic network for which they were individually responsible. The following networks have been infiltrated by the GCHQ: TAT-14 (Europe-USA), Atlantic Crossing 1 (Europe-USA), Circe South (France-UK), Circe North (The Netherlands-UK), Flag Atlantic-1, Flag Europa-Asia, SEA-ME-WE 3 (Southeast Asia-Middle East-Western Europe), SEA-ME-WE 4 (Southeast Asia-Middle East-Western Europe), Solas (Ireland-UK), UK-France 3, UK-Netherlands 14, ULYSSES (Europe-UK), Yellow (UK-USA) and Pan European Crossing.[118]
Telecommunication companies who participated were "forced" to do so and had "no choice in the matter".[118] Some of the companies were subsequently paid by GCHQ for their participation in the infiltration of the cables.[118] According to the SZ the GCHQ has access to the majority of internet and telephone communications flowing throughout Europe, can listen to phone calls, read emails and text messages, see which websites internet users from all around the world are visiting. It can also retain and analyse nearly the entire European internet traffic.[118]
The GCHQ is collecting all data transmitted to and from the United Kingdom and Northern Europe via the undersea fibre optic telecommunications cable SEA-ME-WE 3. Singaporean intelligence co-operates with Australia in accessing and sharing communications carried by the SEA-ME-WE-3 cable. The Australian Signals Directorate, is also in a partnership with British, American and Singaporean intelligence agencies to tap undersea fibre optic telecommunications cables that link Asia, the Middle East and Europe and carry much of Australia's international phone and internet traffic.[119]
The U.S. runs a top-secret surveillance program, code named Special Collection Service, based in over 80 consulates and embassies worldwide, including Frankfurt Germany and Vienna, Austria.[85] The NSA hacked the United Nations' video conferencing system in Summer 2012 in violation of a UN agreement.[85] The Bundesnachrichtendienst is providing the NSA with metadata collected from German systems. In December 2012 alone, Germany provided the NSA with 500 million metadata records.[120][121][122] The N.S.A. is not just intercepting the communications of Americans who are in direct contact with foreigners targeted overseas, but also searching the contents of vast amounts of e-mail and text communications into and out of the country by Americans who mention information about foreigners under surveillance.[123] It also spied on the Al Jazeera and gained access to its internal communications systems.[124]
The NSA has built a surveillance network that has the capacity to reach roughly 75% of all U.S. Internet traffic.[125][126][127] U.S. Law-enforcement agencies use tools used by computer hackers to gather information on suspects.[128][129] An internal NSA audit from May 2012 identified 2776 incidents i.e. violations of the rules or court orders for surveillance of Americans and foreign targets in the U.S. in the period from April 2011 through March 2012, while U.S. officials stressed that any mistakes are not intentional.[130][131][132][133][134][135][136]
The FISA Court that is supposed to provide critical oversight of the U.S. government's vast spying programs has limited ability to do and it must trust the government to report when it improperly spies on Americans.[137] A legal opinion declassified on August 21, 2013 revealed that the NSA intercepted for three years as many as 56,000 electronic communications a year of Americans who weren’t suspected of having links to terrorism, before FISC court that oversees surveillance found the operation unconstitutional in 2011.[138][139][140][141][142] Under the Corporate Partner Access project, major U.S. telecommunications providers receive hundreds of millions of dollars each year from the NSA.[143] Voluntary cooperation between the NSA and the providers of global communications took off during the 1970s under the cover name BLARNEY.[143]
A letter drafted by the Obama administration specifically to inform Congress of the government's mass collection of Americans’ telephone communications data was withheld from lawmakers by leaders of the House Intelligence Committee in the months before a key vote affecting the future of the program.[144][145]
The NSA paid GCHQ over £100 Million between 2009 and 2012, in exchange for these funds GCHQ "must pull its weight and be seen to pull its weight." Documents referenced in the article explain that weaker laws regarding spying are "a selling point". GCHQ is also developing the technology to "exploit any mobile phone at any time."[146] The NSA has under a legal authority a secret backdoor into its databases gathered from large Internet companies enabling it to search for U.S. citizens' email and phone calls without a warrant.[147][148]
The Privacy and Civil Liberties Oversight Board urged the U.S. intelligence chiefs to draft stronger US surveillance guidelines on domestic spying after finding that several of those guidelines have not been updated up to 30 years.[149][150] U.S. intelligence analysts have deliberately broken rules designed to prevent them from spying on Americans by choosing to ignore so-called "minimisation procedures" aimed at protecting privacy.[151][152][153]
After the U.S. Foreign Secret Intelligence Court ruled in October 2011 that some of the NSA's activities were unconstitutional, the agency paid major internet companies millions of dollars to cover extra costs incurred in their invokvement in the PRISM surveillance program.[154]
"Mastering the Internet" (MTI) is part of the Interception Modernisation Programme (IMP) of the British government that involves the insertion of thousands of DPI (deep packet inspection) "black boxes" at various internet service providers, as revealed by the British media in 2009.[155]
In 2013, it was further revealed that the NSA had made a £17.2 million financial contribution to the project, which is capable of vacuuming signals from up to 200 fibre-optic cables at all physical points of entry into Great Britain.[156]
September
The Guardian and the New York Times reported on secret documents leaked by Snowden showing that the NSA has been in "collaboration with technology companies" as part of "an aggressive, multipronged effort" to weaken the encryption used in commercial software, and the GCHQ has a team dedicated to cracking "Hotmail, Google, Yahoo and Facebook" traffic.[157][158][159][160][161][162]
Germany's domestic security agency Bundesverfassungsschutz (BfV) systematically transfers the personal data of German residents to the NSA, CIA and seven other members of the United States Intelligence Community, in exchange for information and espionage software.[163][164][165] Other countries such as Israel, Sweden and Italy are also cooperating with American and British intelligence agencies. Under a secret treaty codenamed "Lustre", French intelligence agencies transferred millions of metadata records to the NSA.[59][60][166][167]
A special branch of the NSA called "Follow the Money" (FTM) monitors international payments, banking and credit card transactions and later stores the collected data in the NSA's own financial databank "Tracfin".[168] The NSA monitored the communications of Brazil's president Dilma Rousseff and her top aides.[169] The agency also spied on Brazil's oil firm Petrobras as well as French diplomats, and gained access to the private network of the Ministry of Foreign Affairs of France and the SWIFT network.[170]
In the United States, the NSA uses the analysis of phone call and e-mail logs of American citizens to create sophisticated graphs of their social connections that can identify their associates, their locations at certain times, their traveling companions and other personal information.[171] The NSA routinely shares raw intelligence data with Israel without first sifting it to remove information about U.S. citizens.[7][172]
In an effort codenamed GENIE, computer specialists can control foreign computer networks using "covert implants,” a form of remotely transmitted malware on tens of thousands of devices annually.[173][174][175][176] As worldwide sales of smartphones began exceeding those of feature phones, the NSA decided to take advantage of the smartphone boom. This is particularly advantageous because the smartphone combines a myriad of data that would interest an intelligence agency, such as social contacts, user behavior, interests, location, photos and credit card numbers and passwords.[177]
An internal NSA report from 2010 stated that the spread of the smartphone has been occurring "extremely rapidly"—developments that "certainly complicate traditional target analysis."[177] According to the document, the NSA has set up task forces assigned to several smartphone manufacturers and operating systems, including Apple Inc.'s iPhone and iOS operating system, as well as Google's Android mobile operating system.[177] Similarly, Britain's GCHQ assigned a team to study and crack the BlackBerry.[177]
Under the heading "iPhone capability", the document notes that there are smaller NSA programs, known as "scripts", that can perform surveillance on 38 different features of the iOS 3 and iOS 4 operating systems. These include the mapping feature, voicemail and photos, as well as Google Earth, Facebook and Yahoo! Messenger.[177]
- A secret NSA presentation leaked to Laura Poitras and Der Spiegel regarding the NSA's iPhone Location Services[178]
-
Who knew in 1984...
-
...that this would be big brother...
-
...and the Zombies would be paying customers?[178]
October
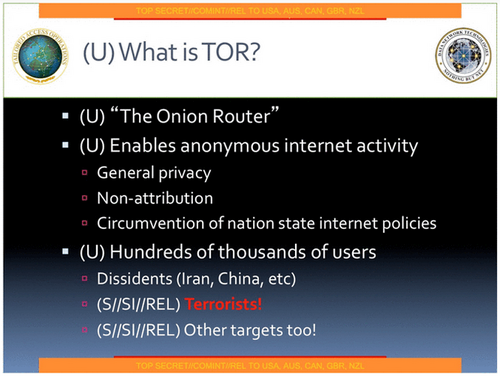
On October 4, 2013, The Washington Post and The Guardian jointly reported that the NSA and the GCHQ have made repeated attempts to spy on anonymous Internet users who have been communicating in secret via the anonymity network Tor. Several of these surveillance operations involve the implantation of malicious code into the computers of Tor users who visit particular websites. The NSA and GCHQ have partly succeeded in blocking access to the anonymous network, diverting Tor users to insecure channels. The government agencies were also able to uncover the identity of some anonymous Internet users.[179][180][181][182][183][184][185][186][187]
The Communications Security Establishment Canada (CSEC) has been using a program called Olympia to map the communications of Brazil's Mines and Energy Ministry by targeting the metadata of phone calls and emails to and from the ministry.[188][189]
The Australian Federal Government knew about the PRISM surveillance program months before Edward Snowden made details public.[190][191]
The German Federal Government also knew about the PRISM surveillance program long before Edward Snowden made details public. According to the German government, however, there are two separate PRISM programs - one is used by the NSA and the other is used by NATO forces in Afghanistan.[192] Both surveillance programs are "not identical".[192]
The NSA monitored the public email account of former Mexican president Felipe Calderón (thus gaining access to the communications of high ranking cabinet members), the E-Mails of several high-ranking members of Mexico's security forces and text and the mobile phone communication of current Mexican president Enrique Peña Nieto.[193][194] The NSA tries to gather cellular and landline phone numbers—often obtained from American diplomats—for as many foreign officials as possible. The contents of the phone calls are stored in computer databases that can regularly be searched using keywords.[195][196]
The NSA has been monitoring telephone conversations of 35 world leaders.[197] The U.S. government's first public acknowledgment that it tapped the phones of world leaders was reported on October 28, 2013 by the Wall Street Journal after an internal U.S. government internal review turned up NSA monitoring of some 35 world leaders.[198] The GCHQ has tried to keep its mass surveillance program a secret because it feared a "damaging public debate" on the scale of its activities which could lead to legal challenges against them.[199]
The Guardian revealed that the NSA had been monitoring telephone conversations of 35 world leaders after being given the numbers by an official in another U.S. government department. A confidential memo revealed that the NSA encouraged senior officials in such Departments as the White House, State and The Pentagon, to share their "Rolodexes" so the agency could add the telephone numbers of leading foreign politicians to their surveillance systems. Reacting to the news, German leader Angela Merkel, arriving in Brussels for an EU summit, accused the U.S. of a breach of trust, saying: "We need to have trust in our allies and partners, and this must now be established once again. I repeat that spying among friends is not at all acceptable against anyone, and that goes for every citizen in Germany."[197] The NSA collected in 2010 data on ordinary Americans’ cellphone locations, but later discontinued it because it had no “operational value.”[200]
Under Britain's MUSCULAR programme, the NSA and the GCHQ have secretly broken into the main communications links that connect Yahoo and Google data centers around the world and thereby gained the abilitiy to collect metadata and content at will from hundreds of millions of user accounts.[201][202][203][204][205]
The mobile phone of German Chancellor Angela Merkel might have been tapped by U.S. intelligence.[206][207][208][209][210][211][212] According to the Spiegel this monitoring goes back to 2002[213][214][215] and ended in the summer of 2013,[198] while the New York Times reported that Germany has evidence that the NSA's surveillance of Merkel began during George W. Bush's tenure.[216] After learning from Der Spiegel magazine that the NSA has been listening in to her personal mobile phone, Merkel compared the snooping practices of the NSA with those of the Stasi.[217]
On October 31, 2013, Hans-Christian Ströbele, a member of the German Bundestag, met Snowden in Moscow and revealed the former intelligence contractor's readiness to brief the German government on NSA spying.[218]
A highly sensitive signals intelligence collection program known as Stateroom involves the interception of radio, telecommunications and internet traffic. It is operated out of the diplomatic missions of the Five Eyes (Australia, Britain, Canada, New Zealand, United States) in numerous locations around the world. The program conducted at U.S. diplomatic missions is run in concert by the U.S. intelligence agencies NSA and CIA in a joint venture group called "Special Collection Service" (SCS), whose members work undercover in shielded areas of the American Embassies and Consulates, where they are officially accredited as diplomats and as such enjoy special privileges. Under diplomatic protection, they are able to look and listen unhindered. The SCS for example used the American Embassy near the Brandenburg Gate in Berlin to monitor communications in Germany's government district with its parliament and the seat of the government.[212][219][220][221]
Under the Stateroom surveillance programme, Australia operates clandestine surveillance facilities to intercept phone calls and data across much of Asia.[220][222]
In France, the NSA targeted people belonging to the worlds of business, politics or French state administration. The NSA monitored and recorded the content of telephone communications and the history of the connections of each target i.e. the metadata.[223][224] The actual surveillance operation was performed by French intelligence agencies on behalf of the NSA.[59][225] The cooperation between France and the NSA was confirmed by the Director of the NSA, Keith B. Alexander, who asserted that foreign intelligence services collected phone records in "war zones" and "other areas outside their borders" and provided them to the NSA.[226]
The French newspaper Le Monde also disclosed new PRISM and Upstream slides (See Page 4, 7 and 8) coming from the "PRISM/US-984XN Overview" presentation.[227]
In Spain, the NSA intercepted the telephone conversations, text messages and emails of millions of Spaniards, and spied on members of the Spanish government.[228] Between December 10, 2012 and January 8, 2013, the NSA collected metadata on 60 million telephone calls in Spain.[229]
According to documents leaked by Snowden, the surveillance of Spanish citizens was jointly conducted by the NSA in close cooperation with Spanish intelligence agencies.[230][231]
November
The New York Times reported that the NSA carries out an eavesdropping effort, dubbed Operation Dreadnought, against the Iranian leader Ayatollah Ali Khamenei. During his 2009 visit to Iranian Kurdistan, the agency collaborated with the GCHQ and the U.S.'s National Geospatial-Intelligence Agency, collecting radio transmissions between aircraft and airports, examining Khamenei's convoy with satellite imagery, and enumerating military radar stations. According to the story, an objective of the operation is "communications fingerprinting": the ability to distinguish Khamenei's communications from those of other people in Iran.[232]
The same story revealed an operation code-named Ironavenger, in which the NSA intercepted e-mails sent between a country allied with the United States and the government of "an adversary". The ally was conducting a spear-phishing attack: its e-mails contained malware. The NSA gathered documents and login credentials belonging to the enemy country, along with knowledge of the ally's capabilities for attacking computers.[232]
According to the British newspaper The Independent, the British intelligence agency GCHQ maintains a listening post on the roof of the British Embassy in Berlin that is capable of intercepting mobile phone calls, wi-fi data and long-distance communications all over the German capital, including adjacent government buildings such as the Reichstag (seat of the German parliament) and the Chancellery (seat of Germany's head of government) clustered around the Brandenburg Gate.[233]
Operating under the code-name "Quantum Insert", the GCHQ set up a fake website masquerading as LinkedIn, a social website used for professional networking, as part of its efforts to install surveillance software on the computers of the telecommunications operator Belgacom.[234] In addition, the headquarters of the oil cartel OPEC were infiltrated by the GCHQ as well as the NSA, which bugged the computers of nine OPEC employees and monitored the General Secretary of OPEC.[234]
For more than three years the GCHQ has been using an automated monitoring system code-named "Royal Concierge" to infiltrate the reservation systems of at least 350 upscale hotels in many different parts of the world in order to target, search and analyze reservations to detect diplomats and government officials.[235] First tested in 2010, the aim of the "Royal Concierge" is to track down the travel plans of diplomats, and it is often supplemented with surveillance methods related to human intelligence (HUMINT). Other covert operations include the wiretapping of room telephones and fax machines used in targeted hotels as well as the monitoring of computers hooked up to the hotel network.[235]
In November 2013, the Australian Broadcasting Corporation and The Guardian claimed that the Australian Signals Directorate (DSD) had attempted to listen to the private phone calls of the president of Indonesia and his wife. The Indonesian foreign minister, Marty Natalegawa, confirmed that he and the president had contacted the ambassador in Canberra. Natalegawa said any tapping of Indonesian politicians’ personal phones “violates every single decent and legal instrument I can think of—national in Indonesia, national in Australia, international as well”.[236] Other high ranking Indonesian politicians targeted by the DSD include:
- Boediono[237] (Vice President)
- Jusuf Kalla[237] (Former Vice President)
- Dino Patti Djalal[237] (Ambassador to the United States)
- Andi Mallarangeng[237] (Government spokesperson)
- Hatta Rajasa[237] (State Secretary)
- Sri Mulyani Indrawati[237] (Former Finance Minister and current managing director of the World Bank)
- Widodo Adi Sutjipto[237] (Former Commander-in-Chief of the military)
- Sofyan Djalil[237] (Senior government advisor)
Carrying the title "3G impact and update", a classified presentation leaked by Snowden revealed the attempts of the ASD/DSD to keep up to pace with the rollout of 3G technology in Indonesia and across Southeast Asia. The ASD/DSD motto placed at the bottom of each page reads: "Reveal their secrets—protect our own."[237]
Under a secret deal approved by British intelligence officials, the NSA has been storing and analyzing the internet and email records of UK citizens since 2007. The NSA also proposed in 2005 a procedure for spying on the citizens of the UK and other Five-Eyes nations alliance, even where the partner government has explicitly denied the U.S. permission to do so. Under the proposal, partner countries must neither be informed about this particular type of surveillance, nor the procedure of doing so.[39]
Towards the end of November, The New York Times released an internal NSA report outlining the agency's efforts to expand its surveillance abilities.[238] The five-page document asserts that the law of the United States has not kept up with the needs of the NSA to conduct mass surveillance in the "golden age" of signals intelligence, but there are grounds for optimism because, in the NSA's own words:
"The culture of compliance, which has allowed the American people to entrust NSA with extraordinary authorities, will not be compromised in the face of so many demands, even as we aggressively pursue legal authorities..."[239]
The report, titled "SIGNT Strategy 2012–2016", also said that the U.S. will try to influence the "global commercial encryption market" through "commercial relationships", and emphasized the need to "revolutionize" the analysis of its vast data collection to "radically increase operational impact".[238]
On November 23, 2013, the Dutch newspaper NRC Handelsblad reported that the Netherlands was targeted by U.S. intelligence agencies in the immediate aftermath of World War II. This period of surveillance lasted from 1946 to 1968, and also included the interception of the communications of other European countries including Belgium, France, West Germany and Norway.[240]

December
According to the classified documents leaked by Snowden, the Australian Signals Directorate, formerly known as the Defence Signals Directorate, had offered to share information on Australian citizens with the other intelligence agencies of the UKUSA Agreement. Data shared with foreign countries include "bulk, unselected, unminimised metadata" such as "medical, legal or religious information".[242]
The Washington Post revealed that the NSA has been tracking the locations of mobile phones from all over the world by tapping into the cables that connect mobile networks globally and that serve U.S. cellphones as well as foreign ones. In the process of doing so, the NSA collects more than five billion records of phone locations on a daily basis. This enables NSA analysts to map cellphone owners’ relationships by correlating their patterns of movement over time with thousands or millions of other phone users who cross their paths.[243][244][245][246][247][248][249][250]
The Norwegian Intelligence Service (NIS), which cooperates with the NSA, has gained access to Russian targets in the Kola Peninsula and other civilian targets. In general, the NIS provides information to the NSA about "Politicians", "Energy" and "Armament".[251] A top secret memo of the NSA lists the following years as milestones of the Norway-United States of America SIGNT agreement, or NORUS Agreement:
- 1952 - Informal starting year of cooperation between the NIS and the NSA[252]
- 1954 - Formalization of the agreement[252]
- 1963 - Extension of the agreement for coverage of foreign instrumentation signals intelligence (FISINT)[252]
- 1970 - Extension of the agreement for coverage of electronic intelligence (ELINT)[252]
- 1994 - Extension of the agreement for coverage of communications intelligence (COMINT)[252]
The NSA considers the NIS to be one of its most reliable partners. Both agencies also cooperate to crack the encryption systems of mutual targets. According to the NSA, Norway has made no objections to its requests from the NIS.[252]
On 5 December, Sveriges Television (Swedish Television) reported that the National Defence Radio Establishment of Sweden (FRA) has been conducting a clandestine surveillance operation targeting the internal politics of Russia. The operation was conducted on behalf of the NSA, which receives data handed over to it by the FRA.[253][254] The Swedish-American surveillance operation also targeted Russian energy interests as well as the Baltic states.[255] As part of the UKUSA Agreement, a secret treaty was signed in 1954 by Sweden with the United States, the United Kingdom, Canada, Australia and New Zealand, regarding collaboration and intelligence sharing.[256]
As a result of Snowden's disclosures, the notion of Swedish neutrality in international politics has been called into question. In an internal document dating from the year 2006, the NSA acknowledged that its "relationship" with Sweden is "protected at the TOP SECRET level because of that nation’s political neutrality."[257] Specific details of Sweden's cooperation with members of the UKUSA Agreement include:
- Sweden updated the NSA on changes in Swedish legislation that provided the legal framework for information sharing between the FRA and the Swedish Security Service.[48]
- Since January 2013, a counterterrorism analyst of the NSA has been stationed in the Swedish capital of Stockholm[48]
- Several years before the Riksdag of Sweden passed the controversial FRA law, which allows the FRA to warrantlessly wiretap all telephone and Internet traffic that crosses Sweden's borders, the NSA, the GCHQ and the FRA signed an agreement in 2004 that allows the FRA to directly collaborate with the NSA without having to consult the GCHQ.[48]
In order to identify targets for government hacking and surveillance, both the GCHQ and the NSA have used advertising cookies operated by Google, known as Pref, to "pinpoint" targets. According to documents leaked by Snowden, the Special Source Operations of the NSA has been sharing information containing "logins, cookies, and GooglePREFID" with the Tailored Access Operations division of the NSA, as well as Britain's GCHQ agency.[259]
During the 2010 G-20 Toronto summit, the U.S. embassy in Ottawa was transformed into a security command post during a six-day spying operation that was conducted by the NSA and closely co-ordinated with the Communications Security Establishment Canada (CSEC). The goal of the spying operation was, among others, to obtain information on international development, banking reform, and to counter trade protectionism to support "U.S. policy goals."[260] On behalf of the NSA, the CSEC has set up covert spying posts in 20 countries around the world.[10]
In Italy the Special Collection Service of the NSA maintains two separate surveillance posts in Rome and Milan.[261] According to a secret NSA memo dated September 2010, the Italian embassy in Washington, D.C. has been targeted by two spy operations of the NSA:
- Under the codename "Bruneau", which refers to mission "Lifesaver", the NSA sucks out all the information stored in the embassy's computers and creates electronic images of hard disk drives.[261]
- Under the codename "Hemlock", which refers to mission "Highlands", the NSA gains access to the embassy's communications through physical "implants".[261]
Due to concerns that terrorist or criminal networks may be secretly communicating via computer games, the NSA, the GCHQ, the CIA, and the FBI have been conducting surveillance and scooping up data from the networks of many online games, including massively multiplayer online role-playing games (MMORPGs) such as World of Warcraft, as well as virtual worlds such as Second Life, and the Xbox gaming console.[262][263][264][265]
The NSA has cracked the most commonly used cellphone encryption technology, A5/1. According to a classified document leaked by Snowden, the agency can "process encrypted A5/1" even when it has not acquired an encryption key.[266] In addition, the NSA uses various types of cellphone infrastructure, such as the links between carrier networks, to determine the location of a cellphone user tracked by Visitor Location Registers.[267]
US district court judge for the District of Columbia, Richard Leon, declared[268][269][270][271][272][273] on December 16, 2013, that the mass collection of metadata of Americans’ telephone records by the National Security Agency probably violates the fourth amendment prohibition of unreasonable searches and seizures.[274] Leon granted the request for a preliminary injunction that blocks the collection of phone data for two private plaintiffs (Larry Klayman, a conservative lawyer, and Charles Strange, father of a cryptologist killed in Afghanistan when his helicopter was shot down in 2011)[275] and ordered the government to destroy any of their records that have been gathered. But the judge stayed action on his ruling pending a government appeal, recognizing in his 68-page opinion the “significant national security interests at stake in this case and the novelty of the constitutional issues.”[274]
However a federal judge in New York City ruled[276] the U.S. government’s global telephone data-gathering system is needed to thwart potential terrorist attacks, and that it can only work if everyone’s calls are swept in. U.S. District Judge William H. Pauley III also ruled that Congress legally set up the program and that it does not violate anyone’s constitutional rights. The judge also concluded that the telephone data being swept up by NSA did not belong to telephone users, but to the telephone companies. He further ruled that when NSA obtains such data from the telephone companies, and then probes into it to find links between callers and potential terrorists, this further use of the data was not even a search under the Fourth Amendment. He also concluded that the controlling precedent is Smith v. Maryland: “Smith’s bedrock holding is that an individual has no legitimate expectation of privacy in information provided to third parties,” Judge Pauley wrote.[277][278][279][280] The American Civil Liberties Union declared on January 2, 2012 that it will appeal Judge Pauley's ruling that NSA bulk the phone record collection is legal. "The government has a legitimate interest in tracking the associations of suspected terrorists, but tracking those associations does not require the government to subject every citizen to permanent surveillance,” deputy ACLU legal director Jameel Jaffer said in a statement.[281]
In recent years, American and British intelligence agencies conducted surveillance on more than 1,100 targets, including the office of an Israeli prime minister, heads of international aid organizations, foreign energy companies and a European Union official involved in antitrust battles with American technology businesses.[282]
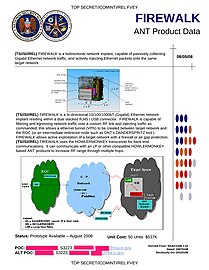
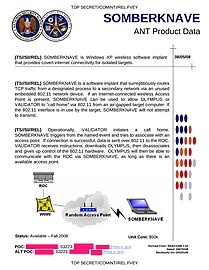
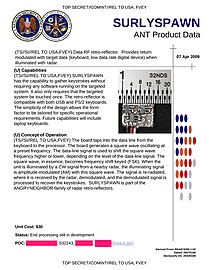
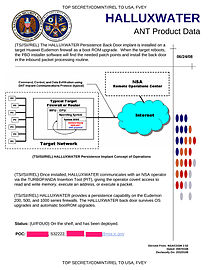
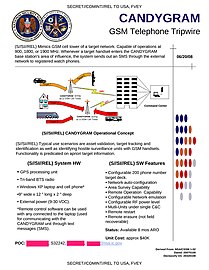
A catalog of high-tech gadgets and software developed by the NSA's Tailored Access Operations (TAO) was leaked by the German news magazine Der Spiegel.[283] Dating from 2008, the catalog revealed the existence of special gadgets modified to capture computer screenshots and USB flash drives secretly fitted with radio transmitters to broadcast stolen data over the airwaves, and fake base stations intended to intercept mobile phone signals, as well as many other secret devices and software implants listed here:
Computer implants
|
|---|
|
|
|
Mobile phone implants and related products
|
|---|
|
The Tailored Access Operations (TAO) division of the NSA intercepted the shipping deliveries of computers and laptops in order to install spyware and physical implants on electronic gadgets. This was done in close cooperation with the FBI and the CIA.[283][284][285][286][287][288][289] NSA officials responded to the Spiegel reports with a statement, which said: "Tailored Access Operations is a unique national asset that is on the front lines of enabling NSA to defend the nation and its allies. [TAO's] work is centred on computer network exploitation in support of foreign intelligence collection."[290]
2014
January
The NSA is working to build a powerful quantum computer capable of breaking all types of encryption.[292][293][294][295][296] The effort is part of a US$79.7 million research program known as "Penetrating Hard Targets". It involves extensive research carried out in large, shielded rooms known as Faraday cages, which are designed to prevent electromagnetic radiation from entering or leaving.[293] Currently, the NSA is close to producing basic building blocks that will allow the agency to gain "complete quantum control on two semiconductor qubits".[293] Once a quantum computer is successfully built, it would enable the NSA to unlock the encryption that protects data held by banks, credit card companies, retailers, brokerages, governments and health care providers.[292]
Aftermath
Reactions of political leaders
| Country | Government official | Quote |
|---|---|---|
| President Barack Obama | "There is no spying on Americans" (August 7)[297][298] | |
| White House Press Secretary Jay Carney |
"They are programs that were authorized by Congress" (June 13)[299] | |
| Attorney General Eric Holder | "We cannot target even foreign persons overseas without a valid foreign intelligence purpose." (June 14)[300] | |
| Prime Minister David Cameron | "If they (the media) don't demonstrate some social responsibility it will be very difficult for government to stand back and not to act" (October 28)[301] | |
| Foreign Secretary William Hague | "We take great care to balance individual privacy with our duty to safeguard the public and UK national security" (June 10)[302] | |
| Deputy Prime Minister Nick Clegg |
"You must absolutely defend the principle of secrecy for the intelligence agencies" (October 10)[303] | |
| Prime Minister Tony Abbott | "Every Australian governmental agency, every Australian official at home and abroad, operates in accordance with the law" (October 31)[304] | |
| Chancellor Angela Merkel | "A country without intelligence work would be too vulnerable." (July 10)[305] | |
| Interior Minister Hans-Peter Friedrich |
"The Americans take our data privacy concerns seriously." (August)[306] | |
| Foreign Minister Carl Bildt | "I am convinced that it is a national necessity for Sweden to have a well-functioning intelligence service" (December 13)[307] |
Review of intelligence agencies
In July 2013, the German government announced an extensive review of Germany's intelligence services.[308][309]
In August 2013, the U.S. government announced an extensive review of U.S. intelligence services.[310][311]
In October 2013, the British government announced an extensive review of British intelligence services.[312]
In December 2013, the Canadian government announced an extensive review of Canada's intelligence services.[313]
Gallery
- International relations
-
NSA's relationship with Norway's NIS
-
NSA's relationship with Sweden's FRA
-
NSA's agreement to share data with Israel's ISNU
-
NSA's relationship with Canada's CSEC
- U.S. domestic federal documents
-
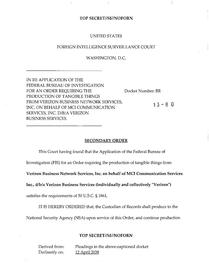
Court order demanding that Verizon hand over all metadata to NSA.
-
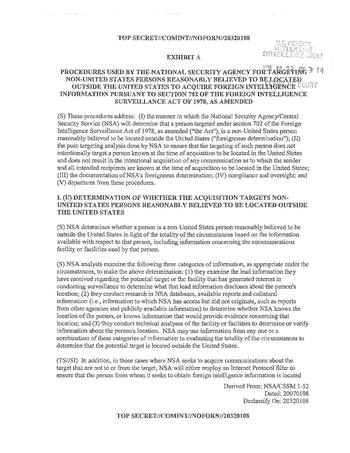
Procedures used to target Foreigners.
-
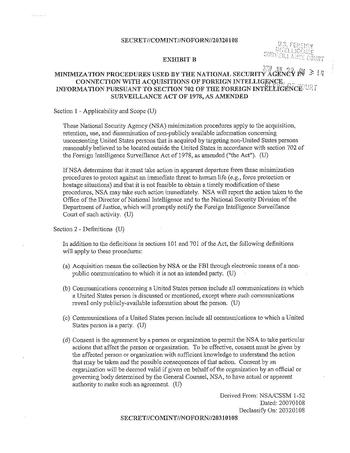
Procedures used to Minimize collection on US persons.
-
2009 OIG Draft Report on Stellar Wind.
-
2007 Memos by Michael Mukasey requesting Broader powers.
-
Presidential Policy Directive – PPD 20 Signed By Barack Obama Relating to Cyberwarfare
-
NSA report on privacy violations.
-
What's a 'privacy violation'
-
FISA Court finds NSA surveillance "deficient on statutory and constitutional grounds" but nonetheless recertifies it.
-
Targeting Rationale Guidelines
-
Extracts of FY 2013 Intelligence Budget, volume 1
-
FY 2013 Intelligence Budget, additional tables
- NSA presentations
-
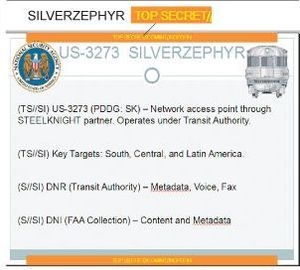
SilverZephyr Slide
-
Dropmire Slide.
-
Documents relating to spying on the 2009 G20 Summit
-
Cover page of the PRISM presentation.
-
Map of global internet bandwidth.
-
Names of the PRISM content providers and which services they typically provide.
-
Dates each content provider was added to PRISM.
-
Flowchart of the PRISM tasking process.
-
PRISM dataflow.
-
Explanation of PRISM case names.
-
REPRISMFISA web application.
-
Upstream and PRISM.
-
A week in the life of Prism
-
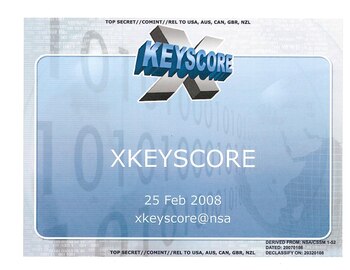
A 2008 Presentation of the XKeyscore program. (PDF, 27.26 MB)
-
Geopolititical Trends: Key Challenges
-
Geopolitical trends: Global Drivers
-
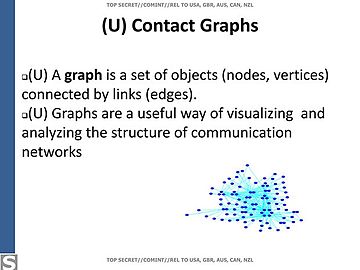
Benefits of contact graph analysis.
-
Benefits of contact graph analysis.
-
Contact graph.
-
Hops in a contact graph.
-
2 hop contact graph.
-
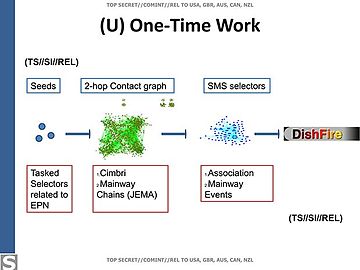
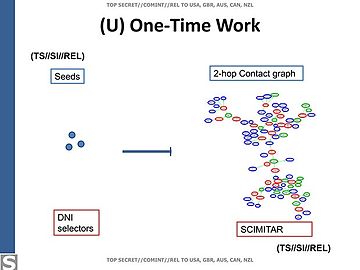
Spying against Enrique Peña Nieto and his associates.
-
Details of the process in the Nieto operation.
-
Emails from Nieto detailing potential cabinet picks.
-
Spying effort against Dilma Rousseff and her advisers.
-
Details of the process in the Rousseff operation (2 hop contact graph)
-
Details of the process in the Rousseff operation (2 hop contact graph)
-
Benefits of contact graph analysis.
-
Exploitation of Common Internet Encryption Technologies.
Exceptionally Controlled Information
According to The Guardian, Exceptionally Controlled Information (ECI) refers to a classification level higher than Snowden's top secret documents.[314] Documents classified as ECI contain the actual identities of the following NSA commercial partners operating the global surveillance network: Artifice, Lithium and Serenade.[314] The name of a commercial NSA partner facility known as Steelknight is classified ECI and therefore not revealed in Snowden's documents.[314]
Comparison with previous leaks
| Year | Disclosure | Size | Main source(s) | Major publisher(s) |
|---|---|---|---|---|
| 2013 | Global surveillance disclosure | 1.5 million documents[3] | Edward Snowden | The Guardian, The New York Times, The Washington Post, Der Spiegel, El País, Le Monde, L'espresso, O Globo, ProPublica, Australian Broadcasting Corporation, Canadian Broadcasting Corporation, NRC Handelsblad, Sveriges Television |
| 2010 | U.S. Army and U.S. State Department documents | 734,885 files | Chelsea (then known as Bradley) Manning | The Guardian, The New York Times. Der Spiegel, Le Monde, El País, WikiLeaks
The material consisted of: |
| 1971 | Pentagon Papers | 4,100 pages | Daniel Ellsberg | The New York Times |
See also
References
- ^ Barton Gellman (24 December 2013). "Edward Snowden, after months of NSA revelations, says his mission's accomplished". The Washington Post. Retrieved 25 December 2013.
Taken together, the revelations have brought to light a global surveillance system...
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Greenwald, Glenn. "NSA collecting phone records of millions of Verizon customers daily". The Guardian. Retrieved August 16, 2013.
Exclusive: Top secret court order requiring Verizon to hand over all call data shows scale of domestic surveillance under Obama
- ^ a b "Report: Some NSA Officials Consider Amnesty for Snowden". Voice of America. Retrieved 14 December 2013.
Some top officials at the National Security Agency (NSA) might be in favor of giving leaker Edward Snowden amnesty if he would return the estimated 1.5 million documents he has yet to leak.
- ^ "NSA Primary Sources". Electronic Frontier Foundation. Retrieved 14 December 2013.
- ^ a b Hubert Gude, Laura Poitras and Marcel Rosenbach (August 5, 2013). "German intelligence Sends Massive Amounts of Data to the NSA". Der Spiegel. Retrieved 14 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Gunnar Rensfeldt. "NSA "asking for" specific exchanges from FRA - Secret treaty since 1954". Sveriges Television. Retrieved 14 December 2013.
- ^ a b c Glenn Greenwald, Laura Poitras and Ewen MacAskill (September 11, 2013). "NSA shares raw intelligence including Americans' data with Israel". The Guardian. Retrieved September 14, 2013.
- ^ Tim Leslie and Mark Corcoran. "Explained: Australia's involvement with the NSA, the US spy agency at heart of global scandal". Australian Broadcasting Corporation. Retrieved 18 December 2013.
- ^ Julian Borger. "GCHQ and European spy agencies worked together on mass surveillance". The Guardian. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Greg Weston, Glenn Greenwald, Ryan Gallagher. "Snowden document shows Canada set up spy posts for NSA". Canadian Broadcasting Corporation. Retrieved 13 December 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ "Denmark is one of the NSA's '9-Eyes'". The Copenhagen Post. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Jacques Follorou. "La France, précieux partenaire de l'espionnage de la NSA" (in French). Le Monde. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Christian Fuchs, John Goetz und Frederik Obermaier. "Verfassungsschutz beliefert NSA" (in German). Süddeutsche Zeitung. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Kjetil Malkenes Hovland. "Norway Monitored Phone Traffic and Shared Data With NSA". The Wall Street Journal. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "USA must not persecute whistleblower Edward Snowden". Amnesty International. Retrieved August 16, 2013.
- ^ "US: Statement on Protection of Whistleblowers in Security Sector". Human Rights Watch. Retrieved August 16, 2013.
- ^ Transparency International Germany. "Transparency International Germany: Whistleblower Prize 2013 for Edward Snowden". Transparency International. Retrieved August 16, 2013.
- ^ "US needs to protect whistleblowers and journalists". Index on Censorship. Retrieved August 16, 2013.
- ^ U.S. vs. Edward J. Snowden criminal complaint. The Washington Post.
- ^ "Leaker Files for Asylum to Remain in Russia". The New York Times. July 16, 2013. Retrieved December 16, 2013.
- ^ "Snowden Asylum Hits U.S.-Russia Relations". The Wall Street Journal. August 1, 2013. Retrieved December 16, 2013.
- ^ ".S. 'Extremely Disappointed' At Russia's Asylum For Snowden". NPR. August 1, 2013. Retrieved December 16, 2013.
- ^ Henderson. "Obama To Leno: 'There Is No Spying On Americans'". NPR. Retrieved August 16, 2013.
- ^ Francis Elliott. "Cameron hints at action to stop security leaks". The Times. Retrieved November 13, 2013.
- ^ RAPHAEL SATTER. "UK Pursuing Criminal Investigation Into NSA Leaks". ABC News. Retrieved November 13, 2013.
- ^ "Only 1% of Snowden files published - Guardian editor". BBC. December 3, 2013. Retrieved December 29, 2013.
- ^ Barton Gellman (24 December 2013). "Edward Snowden, after months of NSA revelations, says his mission's accomplished". The Washington Post. Retrieved 25 December 2013.
Taken together, the revelations have brought to light a global surveillance system that cast off many of its historical restraints after the attacks of Sept. 11, 2001. Secret legal authorities empowered the NSA to sweep in the telephone, Internet and location records of whole populations.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b "Microsoft helped NSA, FBI access user info: Guardian". Reuters. Jul 11, 2013. Retrieved 25 December 2013.
- ^ Andy Greenberg (6/05/2013). "NSA's Verizon Spying Order Specifically Targeted Americans, Not Foreigners". Forbes. Retrieved 25 December 2013.
In a top secret order obtained by the Guardian newspaper and published Wednesday evening, the FBI on the NSA's behalf demanded that Verizon turn over all metadata for phone records originating in the United States for the three months beginning in late April and ending on the 19th of July.
{{cite news}}: Check date values in:|date=(help); Italic or bold markup not allowed in:|newspaper=(help) - ^ "Report: NSA and CIA collaborate on drone strikes". Associated Press. Oct 17, 2013. Retrieved 25 December 2013.
- ^ Doug Gross (December 10, 2013). "Leak: Government spies snooped in 'Warcraft,' other games". CNN. Retrieved 25 December 2013.
- ^ Craig Timberg and Barton Gellman. "NSA paying U.S. companies for access to communications networks". The Washington Post. Retrieved 25 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Michael Winter (August 23, 2013). "NSA reimbursed tech firms millions for data". USA Today. Retrieved 25 December 2013.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ Brian Fung. "The NSA paid Silicon Valley millions to spy on taxpayers". The Washington Post. Retrieved 25 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Rob Williams (2 August 2013). "Americans pay GCHQ £100m to spy for them, leaked NSA papers from Edward Snowden claim". The Independent. Retrieved 25 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Kiran Stacey (August 1, 2013). "US paid GCHQ £100m for UK intelligence, say leaked documents". Financial Times. Retrieved 25 December 2013.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ "Espionnage: les services secrets français précieux partenaires de la NSA américaine" (in French). Radio France Internationale. Retrieved 30 November 2013.
- ^ "SPIEGEL Reveals Cooperation Between NSA and German BND". Der Spiegel. July 8, 2013. Retrieved 25 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Ball, James (20 November 2013). "US and UK struck secret deal to allow NSA to 'unmask' Britons' personal data". The Guardian. Retrieved 21 November 2013.
- ^ Philip Dorling (September 12, 2013). "US shares raw intelligence on Australians with Israel". The Sydney Morning Herald. Retrieved 25 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Ewen MacAskill, James Ball and Katharine Murphy (2 December 2013). "Revealed: Australian spy agency offered to share data about ordinary citizens". The Guardian. Retrieved 25 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Philip Dorling (June 13, 2013). "Australia gets 'deluge' of US secret data, prompting a new data facility". The Sydney Morning Herald. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Nick Hopkins (7 June 2013). "UK gathering secret intelligence via covert NSA operation". The Guardian. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Olmer, Bart. "Ook AIVD bespiedt internetter" (in Dutch). De Telegraaf. Retrieved September 10, 2013.
Niet alleen Amerikaanse inlichtingendiensten monitoren internetters wereldwijd. Ook Nederlandse geheime diensten krijgen informatie uit het omstreden surveillanceprogramma 'Prism'.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Glenn Greenwald, Ewen MacAskill, Laura Poitras, Spencer Ackerman and Dominic Rushe (July 11, 2013). "Revealed: how Microsoft handed the NSA access to encrypted messages". The Guardian. Retrieved July 11, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Brandon Griggs (July 13, 2013). "Report: Microsoft collaborated closely with NSA". CNN. Retrieved 25 December 2013.
And Microsoft also worked with the FBI this year to give the NSA easier access to its cloud storage service SkyDrive
- ^ a b René Pfister, Laura Poitras, Marcel Rosenbach, Jörg Schindler and Holger Stark. "German Intelligence Worked Closely with NSA on Data Surveillance". Der Spiegel. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ a b c d Gunnar Rensfeldt. "Read the Snowden Documents From the NSA". Sveriges Television. Retrieved 12 December 2013.
- ^ Nick Hopkins and Julian Borger (1 August 2013). "Exclusive: NSA pays £100m in secret funding for GCHQ". The Guardian. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Rob Williams (2 August 2013). "Americans pay GCHQ £100m to spy for them, leaked NSA papers from Edward Snowden claim". The Independent. Retrieved 31 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c d e f g h i j k l m n James Ball, Luke Harding and Juliette Garside. "BT and Vodafone among telecoms companies passing details to GCHQ". The Guardian. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Gellman, Barton; Soltani, Ashkan; Peterson, Andrea (November 4, 2013). "How we know the NSA had access to internal Google and Yahoo cloud data". The Washington Post. Retrieved November 5, 2013.
- ^ Matthias Gebauer, Hubert Gude, Veit Medick, Jörg Schindler and Fidelius Schmid. "CIA Worked With BND and BfV In Neuss on Secret Project". Der Spiegel. Retrieved 20 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ Philip Dorling (October 31, 2013). "Exposed: Australia's Asia spy network". The Sydney Morning Herald. Retrieved 23 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c d "Photo Gallery: Spies in the Embassy". Der Spiegel. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Colin Freeze. "Canadian embassies eavesdrop, leak says". The Globe and Mail. Retrieved 23 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Duncan Campbell , Cahal Milmo , Kim Sengupta , Nigel Morris , Tony Patterson (5 November 2013). "Revealed: Britain's 'secret listening post in the heart of Berlin'". The Independent. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ Duncan Campbell and Cahal Milmo (5 November 2013). "Exclusive: RAF Croughton base 'sent secrets from Merkel's phone straight to the CIA'". The Independent. Retrieved 25 December 2013.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ a b c d Jacques Follorou (2013-10-30). "Surveillance : la DGSE a transmis des données à la NSA américaine" (in French). Le Monde. Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c "Espionnage : la France aurait collaboré avec la NSA". Le Parisien. 2013-10-29. Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "U.S. Electronic Espionage: A Memoir". Ramparts. August 1972. pp. 35–50.
The SIGINT community was defined by a TOP SECRET treaty signed in 1947. It was called the UKUSA treaty. The National Security Agency signed for the U.S. and became what's called First Party to the Treaty.
- ^ Campbell, Duncan (1988-08-12), "Somebody's Listening", New Statesman, archived from the original on 2013-04-20,
The Congressional officials were first told of the Thurmond interception by a former employee of the Lockheed Space and Missiles Corporation, Margaret Newsham, who now lives in Sunnyvale, California.
- ^ "Shayler: Whistleblower or traitor?". BBC. 3 March 2000. Retrieved 28 December 2013.
- ^ JOSEPH FINDER (April 29, 2001). "Bugging the World". The New York Times. Retrieved 28 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "NSA Whistleblowers William (Bill) Binney and J. Kirk Wiebe". Government Accountability Project.
- ^ "Interview: Whistleblower Katharine Gun". BBC. 27 November 2003. Retrieved 28 December 2013.
- ^ "UK 'spied on UN's Kofi Annan'". BBC. 26 February 2004. Retrieved 28 December 2013.
- ^ JAMES RISEN and ERIC LICHTBLAU (December 16, 2005). "Bush Lets U.S. Spy on Callers Without Courts". The New York Times.
- ^ Leslie Cauley (5/11/2006). "NSA has massive database of Americans' phone calls". USA Today.
{{cite web}}: Check date values in:|year=(help) - ^ "Wiretap Whistle-Blower's Account". Wired (magazine). April 6, 2006. Retrieved 28 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Brian Ross (10 January 2006). "NSA Whistleblower Alleges Illegal Spying". ABC News. Retrieved 28 December 2013.
- ^ Ellen Nakashima (July 14, 2010). "Former NSA executive Thomas A. Drake may pay high price for media leak". The Washington Post. Retrieved 28 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Wikileaks disclosure shines light on Big Brother". CBS News. December 1, 2011.
- ^ Michael Hastings (28 February 2012). "Exclusive: Homeland Security Kept Tabs on Occupy Wall Street". Rolling Stone. Retrieved 5 January 2014.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ a b "How Edward Snowden led journalist and film-maker to reveal NSA secrets". The Guardian. Retrieved August 20, 2013.
- ^ a b Mark Hosenball (August 15, 2013), Snowden downloaded NSA secrets while working for Dell, sources say Reuters
- ^ a b Peter Maass (August 18, 2013), "How Laura Poitras Helped Snowden Spill His Secrets" The New York Times
- ^ Carmon, Irin (June 10, 2013). "How we broke the NSA story". Salon. Retrieved June 11, 2013.
- ^ Greenwald, Glenn; MacAskill, Ewen; Poitras, Laura (June 9, 2013). "Edward Snowden: the whistleblower behind the NSA surveillance revelations". The Guardian. London. Retrieved June 9, 2013.
- ^ Smith, Matt; Pearson, Michael (June 10, 2013). "NSA leaker holed up in Hong Kong hotel, running low on cash". CNN. Retrieved June 10, 2013.
- ^ Everything We Learned From Edward Snowden in 2013 - NationalJournal.com
- ^ a b Glenn Greenwald (June 6, 2013). "NSA collecting phone records of millions of Verizon customers daily". The Guardian. Retrieved September 16, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ "U.S., British intelligence mining data from nine U.S. Internet companies in broad secret program". The Washington Post. Retrieved August 20, 2013.
- ^ a b c Laura Poitras, Marcel Rosenbach, Fidelius Schmid und Holger Stark. "Geheimdokumente: NSA horcht EU-Vertretungen mit Wanzen aus". Der Spiegel (in German). Retrieved June 29, 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ a b c "US-Geheimdienst hörte Zentrale der Vereinten Nationen ab". Der Spiegel (in German). Retrieved August 25, 2013.
- ^ EXCLUSIVE: US hacks Chinese mobile phone companies, South China Morning Post
- ^ NSA targeted China's Tsinghua University in hacking attacks, South China Morning Post
- ^ Lam, Lana (June 23, 2013). "US hacked Pacnet, Asia Pacific fibre-optic network operator, in 2009". South China Morning Post (Hong Kong). Retrieved June 25, 2013.
- ^ Laura Poitras, Marcel Rosenbach und Holger Stark. "Geheimdokumente: NSA überwacht 500 Millionen Verbindungen in Deutschland". Der Spiegel (in German). Retrieved June 30, 2013.
- ^ MacAskill, Ewen; Borger, Julian (June 30, 2013). "New NSA leaks show how US is bugging its European allies". The Guardian. London.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ MacAskill, Ewen; Davies, Nick; Hopkins, Nick; Borger, Julian; Ball, James (June 17, 2013). "GCHQ intercepted foreign politicians' communications at G20 summits". The Guardian. London.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ MacAskill, Ewen; Borger, Julian; Hopkins, Nick; Davies, Nick; Ball, James (June 21, 2013). "GCHQ taps fiber-optic cables for secret access to world's communications". The Guardian.
- ^ a b Ewen MacAskill; Julian Borger; Nick Hopkins; Nick Davies; James Ball (21 June 2013). "GCHQ taps fibre-optic cables for secret access to world's communications". The Guardian. Retrieved 21 June 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ Philip Bump (21 June 2013). "The UK Tempora Program Captures Vast Amounts of Data – and Shares with NSA". The Atlantic Wire. Retrieved 23 June 2013.
- ^ Greenwald, Glenn (July 31, 2013)."XKeyscore: NSA tool collects 'nearly everything a user does on the internet'". The Guardian. Retrieved August 1, 2013.
- ^ Nakashima, Ellen (July 31, 2013). "Newly declassified documents on phone records program released". The Washington Post. Retrieved August 4, 2013.
- ^ Charlie Savage and David E. Sanger (July 31, 2013). "Senate Panel Presses N.S.A. on Phone Logs". The New York Times. Retrieved August 4, 2013.
- ^ Glenn Greenwald and Spencer Ackerman (June 27, 2013). "NSA collected US email records in bulk for more than two years under Obama". The Guardian. Retrieved August 1, 2013.
- ^ Glenn Greenwald and Spencer Ackerman (June 27, 2013). "How the NSA is still harvesting your online data". The Guardian. Retrieved August 1, 2013.
- ^ Glenn Greenwald and Ewen MacAskill (11 June 2013). "Boundless Informant: the NSA's secret tool to track global surveillance data". The Guardian. Retrieved 1 January 2014.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Laura Poitras, Marcel Rosenbach and Holger Stark. "Partner and Target: NSA Snoops on 500 Million German Data Connections". Der Spiegel. Retrieved 1 January 2014.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Hubert Gude, Laura Poitras and Marcel Rosenbach. "German Intelligence Sends Massive Amounts of Data to the NSA". Der Spiegel. Retrieved 1 January 2014.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ EUA espionaram milhões de e-mails e ligações de brasileiros, O Globo, July 6, 2013. Retrieved July 8, 2013.
- ^ The NSA's mass and indiscriminate spying on Brazilians, Glenn Greenwald, The Guardian, July 7, 2013. Retrieved July 8, 2013.
- ^ EUA expandem o aparato de vigilância continuamente, O Globo, July 6, 2013. Retrieved July 8, 2013.
- ^ Philip Dorling (July 8, 2013). "Snowden reveals Australia's links to US spy web". The Age World. Retrieved July 8, 2013.
- ^ 'Prolific Partner': German Intelligence Used NSA Spy Program, Der Spiegel. Retrieved July 21, 2013.
- ^ unlisted (August 3, 2013). "Überwachung: BND leitet massenhaft Metadaten an die NSA weiter". Der Spiegel (in German). Retrieved August 3, 2013.
- ^ "Interview mit Edward Snowden: NSA liefert BND Werkzeuge für Lauschangriff". Der Spiegel (in German). July 7, 2013. Retrieved September 14, 2013.
- ^ "Snowden: NSA steckte "unter einer Decke mit den Deutschen" Zusammenarbeit zwischen US-Geheimdienst und BND offenbar enger als bekannt" (in German). Deutschlandradio. July 7, 2013. Retrieved September 14, 2013.
- ^ Angwin, Julia (December 13, 2012). "U.S. Terrorism Agency to Tap a Vast Database of Citizens". The Wall Street Journal. Retrieved August 21, 2013.
- ^ Iain Thomson (July 8, 2013). "Snowden: US and Israel did create Stuxnet attack code". The Register. Retrieved July 8, 2013.
- ^ Révélations sur le Big Brother français(2), Le Monde, July 4, 2013. Retrieved July 5, 2013.
- ^ France 'runs vast electronic spying operation using NSA-style methods', The Guardian, July 4, 2013. Retrieved July 5, 2013.
- ^ "NDR/SZ: Neue Dokumente belasten britischen Geheimdienst – Deutsche Telekom verlangt Auskünfte". NDR Presse und Information (in German). NDR. August 28, 2013. Retrieved August 30, 2013.
- ^ John Goetz, Hans Leyendecker and Frederik Obermaier (August 28, 2013). "Britischer Geheimdienst zapft Daten aus Deutschland ab". Süddeutsche Zeitung (in German). Retrieved August 30, 2013.
- ^ a b c d e f g John Goetz and Frederik Obermaier. "Snowden enthüllt Namen der spähenden Telekomfirmen". Süddeutsche Zeitung (in German). Retrieved August 2, 2013.
In den internen Papieren des GCHQ aus dem Jahr 2009 stehen sie nun aufgelistet: Verizon Business, Codename: Dacron, British Telecommunications (codenamed "Remedy"), Vodafone Cable ("Gerontic"), Global Crossing ("Pinnage"), Level 3 (codenamed "Little"), Viatel ("Vitreous") und Interoute ("Streetcar").
- ^ a b c d John Goetz, Hans Leyendecker and Frederik Obermaier (August 28, 2013). "British Officials Have Far-Reaching Access To Internet And Telephone Communications". Süddeutsche Zeitung. Retrieved August 28, 2013.
{{cite news}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Dorling, Philip. "Australian spies in global deal to tap undersea cables". The Sydney Morning Herald. Retrieved August 29, 2013.
- ^ unlisted (August 3, 2013). "Überwachung: BND leitet massenhaft Metadaten an die NSA weiter". Retrieved August 3, 2013.
- ^ Geiger, Friedrich (August 3, 2013). "German Intelligence Agency Providing NSA With Metadata – Report". Retrieved August 3, 2013.
- ^ Mass Data: Transfers from Germany Aid US Surveillance August 5, 2013
- ^ Savage, Charlie (August 8, 2013). "N.S.A. Said to Search Content of Messages to and From U.S." The New York Times. Retrieved September 30, 2013.
- ^ "Snowden Document: NSA Spied On Al Jazeera Communications". Der Spiegel. August 31, 2013. Retrieved 1 January 2014.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ Siobhan Gorman and Jennifer Valentiono-Devries (August 20, 2013). "New Details Show Broader NSA Surveillance Reach – Programs Cover 75% of Nation's Traffic, Can Snare Emails". The Wall Street Journal. Retrieved August 21, 2013.
- ^ "Graphic: How the NSA Scours Internet Traffic in the U.S." The Wall Street Journal. August 20, 2013. Retrieved August 21, 2013.
- ^ Jennifer Valentiono-Devries and Siobhan Gorman (August 20, 2013). "What You Need to Know on New Details of NSA Spying". The Wall Street Journal. Retrieved August 21, 2013.
- ^ Jennifer Valentino-Devries and Danny Yadron (August 1, 2013). "FBI Taps Hacker Tactics to Spy on Suspects". The Wall Street Journal. Retrieved October 9, 2013.
- ^ Jennifer Valentino-DeVries and Danny Yadron (August 1, 2013). "How the FBI Hacks Criminal Suspects". The Wall Street Journal. Retrieved October 9, 2013.
- ^ "NSA report on privacy violations in the first quarter of 2012". The Washington Post. August 16, 2013. Retrieved August 16, 2013.
- ^ Barton Gellman and Matt DeLong (August 15, 2013). "What to say, and not to say, to 'our overseers'". The Washington Post. Retrieved August 25, 2013.
- ^ Barton Gellman and Matt DeLong (August 15, 2013). "First direct evidence of illegal surveillance found by the FISA court". The Washington Post. Retrieved August 25, 2013.
- ^ Gellmann, Barton (August 16, 2013). "NSA broke privacy rules thousands of times per year, audit finds". The Washington Post. Retrieved August 24, 2013.
- ^ Nakashima, Ellen (August 16, 2013). "Lawmakers, privacy advocates call for reforms at NSA". The Washington Post. Retrieved August 25, 2013.
- ^ Gellmann, Barton (August 16, 2013). "NSA statements to The Post". The Washington Post. Retrieved August 25, 2013.
- ^ Barton Gellman and Matt DeLong (August 15, 2013). "What's a 'violation'?". The Washington Post. Retrieved August 25, 2013.
- ^ Leonnig, Carol D. (August 16, 2013). "Court: Ability to police U.S. spying program limited". The Washington Post. Retrieved August 25, 2013.
- ^ Nakashima, Ellen (August 21, 2013). "NSA gathered thousands of Americans' e-mails before court ordered it to revise its tactics". The Washington Post. Retrieved September 16, 2013.
- ^ "FISA court ruling on illegal NSA e-mail collection program". The Washington Post. August 21, 2013. Retrieved September 16, 2013.
- ^ Barton Gellman and Matt DeLong (August 15, 2013). "First direct evidence of illegal surveillance found by the FISA court". The Washington Post. Retrieved September 16, 2013.
- ^ Charlie Savage and Scott Shane (August 21, 2013). "Secret Court Rebuked N.S.A. on Surveillance". The New York Times. Retrieved September 16, 2013.
- ^ Mark Hosenball and Tabassum Zakaria (August 22, 2013). "NSA collected 56,000 emails by Americans a year: documents". Reuters. NBC News. Retrieved September 16, 2013.
- ^ a b Craig Timberg and Barton Gellman (August 30, 2013). "NSA paying U.S. companies for access to communications networks". The Washington Post. Retrieved August 31, 2013.
- ^ Wallsten, Peter (August 17, 2013). "House panel withheld document on NSA surveillance program from members". The Washington Post. Retrieved August 25, 2013.
- ^ Weich, Ronald. "Report of the National Security Agency's Bulk Collection Programs for USA PATRIOT Act Reauthorization" (PDF). Office of the Assistant Attorney General. Director of National Intelligence. Retrieved August 25, 2013.
- ^ James Ball, Luke Harding and Juliette Garside (August 1, 2013). "Exclusive: NSA pays £100m in secret funding for GCHQ". Retrieved August 2, 2013.
- ^ James Ball and Spencer Ackerman (August 9, 2013). "NSA loophole allows warrantless search for US citizens' emails and phone calls – Exclusive: Spy agency has secret backdoor permission to search databases for individual Americans' communications". The Guardian. Retrieved August 12, 2013.
- ^ Farivar, Cyrus (August 10, 2013). "New leak: NSA can search US e-mail data but theoretically won't". Ars Technica. Retrieved August 13, 2013.
- ^ Roberts, Dan (August 23, 2013). "US surveillance guidelines not updated for 30 years, privacy board finds – Privacy watchdog points out in letter to intelligence chiefs that rules designed to protect Americans are severely outdated". The Guardian. Retrieved August 24, 2013.
- ^ Medine, David (August 22, 2013). "2013-08-22 Privacy and Civil Liberties Oversight Board letter to US Attorney General Eric Holder and Directer of National Intelligence James Clapper" (PDF). Privacy & Civil Liberties Oversight Board. Retrieved August 24, 2013.
- ^ Strohm, Chris (August 24, 2013). "Lawmakers Probe Willful Abuses of Power by NSA Analysts". Bloomberg News. Retrieved August 24, 2013.
- ^ Roberts, Dan (August 23, 2013). "NSA analysts deliberately broke rules to spy on Americans, agency reveals – Inspector general's admission undermines fresh insistences from president that breaches of privacy rules were inadvertent". The Guardian. Retrieved August 24, 2013.
- ^ Gorman, Siobhan (August 23, 2013). "NSA Officers Spy on Love Interests". The Wall Street Journal. Retrieved August 24, 2013.
- ^ MacAskill, Ewen (August 23, 2013). "NSA paid millions to cover Prism compliance costs for tech companies • Top-secret files show first evidence of financial relationship • Prism companies include Google and Yahoo, says NSA • Costs were incurred after 2011 Fisa court ruling". The Guardian. Retrieved August 24, 2013.
- ^ David Leppard and Chris Williams (May 3, 2009). "Jacqui Smith's secret plan to carry on snooping". The Sunday Times. Retrieved May 3, 2009.
- ^ Henry Porter. "GCHQ revelations: mastery of the internet will mean mastery of everyone". The Guardian. Retrieved October 19, 2013.
- ^ James Ball, Julian Borger and Glenn Greenwald (September 5, 2013). "US and UK spy agencies defeat privacy and security on the internet". The Guardian. Retrieved September 5, 2013.
- ^ Nicole Perlroth, Jeff Larson and Scott Shane (September 5, 2013). "N.S.A. Foils Much Internet Encryption". The New York Times. Retrieved September 5, 2013.
- ^ "Secret Documents Reveal N.S.A. Campaign Against Encryption". The New York Times. September 5, 2013. Retrieved September 7, 2013.
- ^ "Unlocking Private Communications". The New York Times. September 5, 2013. Retrieved September 7, 2013.
- ^ Perlroth, Nicole, Larson, Jeff, and Shane, Scott (September 5, 2013). "The NSA's Secret Campaign to Crack, Undermine Internet Security". ProPublica.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Nakashima, Ellen (September 6, 2013). "NSA has made strides in thwarting encryption used to protect Internet communication". The Washington Post. Retrieved September 7, 2013.
- ^ "Verfassungsschutz spionierte für Geheimdienste - Bundesamt-Chef Maaßen stimmte zu". Norddeutscher Rundfunk (in German). Norddeutscher Rundfunk. September 13, 2013. Retrieved September 14, 2013.
- ^ "Verfassungsschutz beliefert NSA". Süddeutsche Zeitung (in German). September 13, 2013. Retrieved September 14, 2013.
- ^ "Auch Verfassungsschutz liefert Daten an NSA "Süddeutsche Zeitung" und NDR berichten über intensiven Datenaustausch". Deutschland Radio (in German). Deutschland Radio. September 13, 2013. Retrieved September 14, 2013.
- ^ Guillaume Champeau. "Lustre : la France aurait coopéré avec la NSA" (in French). Numerama. Retrieved 30 December 2013.
- ^ "Espionnage : la France perd son Lustre" (in French). ZDNet. 28 Octobre 2013. Retrieved 30 December 2013.
{{cite web}}: Check date values in:|date=(help) - ^ "'Follow the Money': NSA Spies on International Payments". Der Spiegel. September 15, 2013. Retrieved September 24, 2013.
- ^ "Brazil Angered Over Report N.S.A. Spied on President". The New York Times. Retrieved September 16, 2013.
{{cite news}}: Unknown parameter|deadurl=ignored (|url-status=suggested) (help) - ^ "NSA Documents Show United States Spied Brazilian Oil Giant". Jornal da Globo Fantástico. September 8, 2013. Retrieved September 24, 2013.
- ^ James Risen and Laura Poitras (September 28, 2013). "N.S.A. Gathers Data on Social Connections of U.S. Citizens". The New York Times. Retrieved September 30, 2013.
- ^ "NSA and Israeli intelligence: memorandum of understanding – full document". The Guardian. September 11, 2013. Retrieved September 14, 2013.
- ^ Barton Gellman. "Secret documents detail U.S. war in cyberspace". The Washington Post (via The Japan Times). Retrieved September 2, 2013.
- ^ Barton Gellman and Ellen Nakashima (August 31, 2013). "U.S. spy agencies mounted 231 offensive cyber-operations in 2011, documents show". The Washington Post. Retrieved August 31, 2013.
- ^ Konrad Lischka und Julia Stanek (August 31, 2013). "Cyber-Angriffe: USA infizieren Zehntausende Computer mit NSA-Trojanern". Der SPIEGEL (in German). Retrieved August 31, 2013.
- ^ Zetter, Kim (September 4, 2013). "NSA Laughs at PCs, Prefers Hacking Routers and Switches". Wired.com. Retrieved October 2, 2013.
- ^ a b c d e Laura Poitras, Marcel Rosenbach and Holger Stark. "iSpy: How the NSA Accesses Smartphone Data". Der Spiegel. Retrieved September 9, 2013.
- ^ a b Laura Poitras, Marcel Rosenbach, and Holger Stark. "Photo Gallery: Spying on Smartphones". Der Spiegel. Retrieved September 9, 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ Barton Gellman, Craig Timberg and Steven Rich (4 October 2013). "Secret NSA documents show campaign against Tor encrypted network". The Washington Post. Retrieved 19 November 2013.
- ^ Steven Rich and Matt DeLong (4 October 2013). "NSA slideshow on 'The TOR problem'". The Washington Post. Retrieved 19 November 2013.
- ^ Lee, Timothy B. (4 October 2013). "Everything you need to know about the NSA and Tor in one FAQ". The Washington Post. Retrieved 19 November 2013.
- ^ "NSA report on the Tor encrypted network". The Washington Post. 4 October 2013. Retrieved 19 November 2013.
- ^ "GCHQ report on 'MULLENIZE' program to 'stain' anonymous electronic traffic". The Washington Post. 4 October 2013. Retrieved 19 November 2013.
- ^ James Ball, Bruce Schneier and Glenn Greenwald (4 October 2013). "NSA and GCHQ target Tor network that protects anonymity of web users". The Guardian. Retrieved 19 November 2013.
- ^ Schneier, Bruce (4 October 2013). "Attacking Tor: how the NSA targets users' online anonymity". The Guardian. Retrieved 19 November 2013.
- ^ "'Tor Stinks' presentation – read the full document". The Guardian. 4 October 2013. Retrieved 19 November 2013.
- ^ "Tor: 'The king of high-secure, low-latency anonymity'". The Guardian. 4 October 2013. Retrieved 19 November 2013.
- ^ "Ministério de Minas e Energia está na mira de espiões americanos e canadenses". O Globo. October 6, 2013. Retrieved October 8, 2013.
- ^ "Report: Canada spies targeted Brazil mine ministry". Associated Press. Associated Press. October 6, 2013. Retrieved October 8, 2013.
- ^ Ockenden, Will (October 8, 2013). "Australia prepared briefing on US global internet spying program PRISM before Snowden revelations". ABC News (Australia). Retrieved October 8, 2013.
- ^ "AG Department Prism FOI PDF". ABC News Online. June 27, 2013. Retrieved October 8, 2013.
- ^ a b Matthias Gebauer. "Prism in Afghanistan: Conflicting Accounts By German Government". Der Spiegel.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ Jens Glüsing, Laura Poitras, Marcel Rosenbach and Holger Stark (October 20, 2013). "Fresh Leak on US Spying: NSA Accessed Mexican President's Email". Der Spiegel. Retrieved October 22, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ "NSA-Spionage: Mexiko fordert Aufklärung über US-Bespitzelungen". Der Spiegel (in German). October 21, 2013. Retrieved October 22, 2013.
- ^ Mark Mazzetti and David E. Sanger (October 30, 2013). "Tap on Merkel Provides Peek at Vast Spy Net". The New York Times. Retrieved November 1, 2013.
- ^ Mark Landler and Michael S. Schmidt (October 30, 2013). "Spying Known at Top Levels, Officials Say". The New York Times. Retrieved November 1, 2013.
- ^ a b Ball, James (October 24, 2013). "NSA monitored calls of 35 world leaders after US official handed over contacts". The Guardian. Retrieved October 24, 2013.
- ^ a b Siobhan Gorhan and Adam Entous (October 28, 2013). "Obama Unaware as U.S. Spied on World Leaders: Officials". The Wall Street Journal. Retrieved October 28, 2013.
- ^ Ball, James (October 25, 2013). "Leaked memos reveal GCHQ efforts to keep mass surveillance secret". The Guardian. Retrieved October 25, 2013.
- ^ Nakashima, Ellen (October 2, 2013). "NSA had test project to collect data on Americans' cellphone locations, director says". The Washington Post. Retrieved October 18, 2013.
- ^ Barton Gellman and Ashkan Soltani (October 30, 2013). "NSA infiltrates links to Yahoo, Google data centers worldwide, Snowden documents say". The Washington Post. Retrieved October 31, 2013.
- ^ Barton Gellman, Todd Lindeman and Ashkan Soltani (October 30, 2013). "How the NSA is infiltrating private networks". The Washington Post. Retrieved October 31, 2013.
- ^ Barton Gellman and Matt DeLong (October 30, 2013). "How the NSA's MUSCULAR program collects too much data from Yahoo and Google". The Washington Post. Retrieved October 31, 2013.
- ^ Peterson, Andrea (October 30, 2013). "PRISM already gave the NSA access to tech giants. Here's why it wanted more". The Washington Post. Retrieved October 31, 2013.
- ^ Washington Post Staff (October 30, 2013). "NSA statement on Washington Post report on infiltration of Google, Yahoo data center links". The Washington Post. Retrieved October 31, 2013.
- ^ Jacob Appelbaum, Holger Stark, Marcel Rosenbach and Jörg Schindler (October 23, 2013). "Berlin Complains: Did US Tap Chancellor Merkel's Mobile Phone?". Der Spiegel. Retrieved October 25, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Fischer, Sebastian (October 24, 2013). "Merkel's Phone: Spying Suspicions Put Obama in a Tight Spot". Der Spiegel. Retrieved October 25, 2013.
- ^ Charly Wilder and Rupert Neat (October 24). "'Out of Hand': Europe Furious Over US Spying Allegations". Der Spiegel. Retrieved October 25, 2013.
{{cite news}}: Check date values in:|date=(help) - ^ Ian Traynor in Brussels, Philip Oltermann in Berlin, and Paul Lewis in Washington (October 24). "Angela Merkel's call to Obama: are you bugging my mobile phone?". The Guardian. Retrieved October 25, 2013.
{{cite news}}: Check date values in:|date=(help)CS1 maint: multiple names: authors list (link) - ^ Ball, James (October 25, 2013). "NSA monitored calls of 35 world leaders after US official handed over contacts". The Guardian. Retrieved October 25, 2013.
- ^ Traynor, Ian (October 25, 2013). "Germany and France warn NSA spying fallout jeopardises fight against terror". The Guardian. Retrieved October 25, 2013.
- ^ a b Jacob Appelbaum, Nikolaus Blome, Hubert Gude, Ralf Neukirch, René Pfister, Laura Poitras, Marcel Rosenbach, Jörg Schindler, Gregor Peter Schmitz and Holger Stark. Translated from the German by Kristen Allen and Charly Wilder. (October 27, 2013). "Der Spiegel Cover Story: How NSA Spied on Merkel Cell Phone from Berlin Embassy - Embassy Espionage: The NSA's Secret Spy Hub in Berlin". Der Spiegel. Retrieved November 1, 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ "NSA-Überwachung: Merkels Handy steht seit 2002 auf US-Abhörliste". Der Spiegel (in German). October 26, 2012. Retrieved October 26, 2013.
- ^ "U.S. monitored German Chancellor Angela Merkel's phone since 2002". Daily Mail. October 26, 2012. Retrieved October 26, 2013.
- ^ Ofer Aderet (October 26, 2015). "Obama: Had I known NSA tapped Merkel's cell, I would have stopped it, German media reports". Haaretz. Retrieved October 26, 2013.
- ^ David E. Sanger and Mark Mazzetti (October 24, 2013). "Allegation of U.S. Spying on Merkel Puts Obama at Crossroads". The New York Times. Retrieved October 26, 2013.
- ^ Ian Traynor and Paul Lewis (17 December 2013). "Merkel compared NSA to Stasi in heated encounter with Obama". The Guardian. Retrieved 18 December 2013.
- ^ "Germany hopes for details from Snowden on US spying". bbc.co.uk. November 1, 2013. Retrieved November 1, 2013.
- ^ "Photo Gallery: Spies in the Embassy 10/27/2013". Der Spiegel. October 27, 2013. Retrieved November 1, 2013.
- ^ a b Dorling, Philipp (October 31, 2013). "Exposed: Australia's Asia spy network". The Sydney Morning Herald. Retrieved November 1, 2013.
- ^ Konrad Lischka and Matthias Kremp (October 28, 2013). "NSA-Spähskandal: So funktionieren die Abhöranlagen in US-Botschaften". Der Spiegel (in German). Retrieved November 1, 2013.
- ^ Perlez, Jane (October 31, 2013). "Australia Said to Play Part in N.S.A. Effort". The New York Times. Retrieved November 1, 2013.
- ^ Jacques Follorou and Glenn Greenwald (October 21, 2013). "France in the NSA's crosshair : phone networks under surveillance". Le Monde. Retrieved October 22, 2013.
- ^ Gearan, Anna (October 22, 2013). "Report that NSA collected French phone records causing diplomatic headache for U.S." The Washington Post. Retrieved October 22, 2013.
- ^ Adam Entous and Siobhan Gorman (October 29, 2013). "U.S. Says France, Spain Aided NSA Spying". The Wall Street Journal. Retrieved October 29, 2013.
- ^ Ellen Nakashima and Karen DeYoung (October 29, 2013). "NSA chief says NATO allies shared phone records with the U.S. spy agency". The Washington Post. Retrieved October 30, 2013.
- ^ "Espionnage de la NSA : tous les documents publiés par "Le Monde"". Le Monde. October 21, 2013. Retrieved October 22, 2013.
- ^ Miguel González. "NSA revelations: Spain also a victim of US espionage". El Pais. Retrieved 13 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Miguel González. "España eleva el tono de las quejas a EE UU por el espionaje masivo" (in Spanish). El Pais. Retrieved 13 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Paul Hamilos. "Spain colluded in NSA spying on its citizens, Spanish newspaper reports". The Guardian. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Glenn Greenwald and Germán Aranda. "El CNI facilitó el espionaje masivo de EEUU a España" (in Spanish). El Mundo. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Shane, Scott (2013-11-02). "No Morsel Too Minuscule for All-Consuming N.S.A." New York Times. Archived from the original on 2013-11-25. Retrieved 2013-11-25.
This "communications fingerprinting," as a document called it, is the key to what the N.S.A. does. It allows the agency's computers to scan the stream of international communications and pluck out messages tied to the supreme leader.
- ^ Campbell, Duncan (November 5, 2013). "Revealed: Britain's 'secret listening post in the heart of Berlin'". The Independent. Retrieved November 5, 2013.
- ^ a b Tony Paterson. "GCHQ used 'Quantum Insert' technique to set up fake LinkedIn pages and spy on mobile phone giants". The Independent. Retrieved November 10, 2013.
- ^ a b Laura Poitras, Marcel Rosenbach and Holger Stark (November 17, 2013). "'Royal Concierge': GCHQ Monitors Hotel Reservations to Track Diplomats". Der Spiegel. Retrieved November 17, 2013.
- ^ Indonesia recalls Canberra ambassador over Yudhoyono phone tapping attempt, Foreign minister demands explanation after documents reveal Australian agencies targeted phones of president and his wife The Guardian 18 November 2013
- ^ a b c d e f g h i Michael Brissenden (18 Nov 2013). "Australia spied on Indonesian president Susilo Bambang Yudhoyono, leaked Edward Snowden documents reveal". Australian Broadcasting Corporation. Retrieved 13 December 2013.
- ^ a b JAMES RISEN and LAURA POITRAS (November 22, 2013). "N.S.A. Report Outlined Goals for More Power". The New York Times. Retrieved 23 November 2013.
- ^ "A Strategy for Surveillance Powers". The New York Times. Retrieved 23 November 2013.
- ^ Floor Boon, Steven Derix and Huib Modderkolk. "Document Snowden: Nederland al sinds 1946 doelwit van NSA". NRC Handelsblad (in Dutch). Retrieved 23 November 2013.
- ^ Floor Boon, Steven Derix and Huib Modderkolk. "NSA infected 50,000 computer networks with malicious software". NRC Handelsblad. Retrieved 23 November 2013.
- ^ Ewen MacAskill, James Ball and Katharine Murphy. "Revealed: Australian spy agency offered to share data about ordinary citizens". The Guardian. Retrieved 3 December 2013.
- ^ a b Barton Gellman and Ashkan Soltani (4 December 2013). "NSA tracking cellphone locations worldwide, Snowden documents show". The Washington Post. Retrieved 5 December 2013.
- ^ "How the NSA is tracking people right now". The Washington Post. 4 December 2013. Retrieved 6 December 2013.
- ^ Ashkan Soltani and Matt DeLong (4 December 2013). "FASCIA: The NSA's huge trove of location records". The Washington Post. Retrieved 6 December 2013.
- ^ "How the NSA uses cellphone tracking to find and 'develop' targets". The Washington Post. 4 December 2013. Retrieved 6 December 2013.
- ^ "Reporter explains NSA collection of cellphone data". The Washington Post. 4 December 2013. Retrieved 6 December 2013.
- ^ Peterson, Andrea (4 December 2013). "The NSA says it 'obviously' can track locations without a warrant. That's not so obvious". The Washington Post's The Switch. Retrieved 6 December 2013.
- ^ Lee, Timothy (4 December 2013). "The NSA could figure out how many Americans it's spying on. It just doesn't want to". The Washington Post's The Switch. Retrieved 6 December 2013.
- ^ Ashkan Soltani and Barton Gellmann (10 December 2013). "New documents show how the NSA infers relationships based on mobile location data". The Washington Post. Retrieved 26 December 2013.
- ^ Arne Halvorsen, Anne Marte Blindheim, Harald S. Klungtveit, Kjetil Magne Sørenes, Tore Bergsaker and Gunnar Hultgreen. "Norway´s secret surveillance of Russian politics for the NSA". Dagbladet. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ a b c d e f "Snowden-dokumentene: Norge er NSAs drømmepartner" (in Norwegian). Dagbladet. Retrieved 18 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Glenn Greenwald, Ryan Gallagher, Filip Struwe and Anna H Svensson. "SVT avslöjar: FRA spionerar på Ryssland åt USA" (in Swedish). Sveriges Television. Retrieved 5 December 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ Filip Struwe, Glenn Greenwald, Ryan Gallagher, Sven Bergman, Joachim Dyfvermark and Fredrik Laurin. "Snowden files reveal Swedish-American surveillance of Russia" (in Swedish). Sveriges Television. Retrieved 5 December 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ Sven Bergman, Joachim Dyfvermark, Ryan Gallagher, Glenn Greenwald and Fredrik Laurin. "FRA spying on "energy" and "Baltics" for USA". Sveriges Television. Retrieved 7 December 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ "Cold War treaty confirms Sweden was not neutral". The Local. Retrieved 12 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "NSA "asking for" specific exchanges from FRA - Secret treaty since 1954". Sveriges Television. Retrieved 12 December 2013.
- ^ "Read the Snowden Documents From the NSA". Sveriges Television. Retrieved 12 December 2013.
- ^ Ashkan Soltani, Andrea Peterson, and Barton Gellman. "NSA uses Google cookies to pinpoint targets for hacking". The Washington Post. Retrieved 12 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ Greg Weston, Glenn Greenwald, Ryan Gallagher. "New Snowden docs show U.S. spied during G20 in Toronto". Canadian Broadcasting Corporation. Retrieved 13 December 2013.
{{cite web}}: CS1 maint: multiple names: authors list (link) - ^ a b c Glenn Greenwald and Stefania Maurizi. "Revealed: How the NSA Targets Italy". L'espresso. Retrieved 13 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ MARK MAZZETTI and JUSTIN ELLIOTT (9 December 2013). "Spies Infiltrate a Fantasy Realm of Online Games". The New York Times. Retrieved 12 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Ball, James (9 December 2013). "Xbox Live among game services targeted by US and UK spy agencies". The Guardian. Retrieved 18 December 2013.
- ^ "NSA files: games and virtual environments paper". The Guardian. 9 December 2013. Retrieved 18 December 2013.
- ^ Justin Elliott, ProPublica, and Mark Mazzetti, The New York Times (9 December 2013). "NSA files: games and virtual environments paper". Pro Publica. Retrieved 18 December 2013.
{{cite news}}: CS1 maint: multiple names: authors list (link) - ^ Craig Timberg and Ashkan Soltani. "By cracking cellphone code, NSA has capacity for decoding private conversations". The Washington Post. Retrieved 14 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "How the NSA pinpoints a mobile device". The Washington Post. Retrieved 14 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Leon, Richard (16 December 2013). "Federal judge rules NSA program is likely unconstitutional a.k.a. Klayman et al. v. Obama et al. Memorandum and Opinion from December 16, 2013 in Civil Action 13-0851 in United Case District Court for the District of Columbia". The Washington Post. Retrieved 17 December 2013.
- ^ Savage, Charlie (16 December 2013). "Judge Questions Legality of N.S.A. Phone Records". The New York Times. Retrieved 18 December 2013.
- ^ Bill Mears and Evan Perez, CNN (17 December 2013). "Judge: NSA domestic phone data-mining unconstitutional". cnn. Retrieved 18 December 2013.
{{cite web}}:|author=has generic name (help) - ^ Kravets, David (16 December 2013). "Court Says NSA Bulk Telephone Spying Is Unconstitutional". Retrieved 18 December 2013.
- ^ Kevin Johnson and Richard Wolf (16 December 2013). "Federal judge rules against NSA spying". USA Today. Retrieved 18 December 2013.
- ^ Gerstein, Josh (16 December 2013). "Judge: NSA phone program likely unconstitutional". Politico. Retrieved 18 December 2013.
- ^ a b Ellen Nakashima and Ann E. Marimow (16 December 2013). "Judge: NSA's collecting of phone records is probably unconstitutional". The Washington Post. Retrieved 17 December 2013.
- ^ Spencer Ackerman and Dan Roberts (16 December 2013). "NSA phone surveillance program likely unconstitutional, federal judge rules". The Guardian. Retrieved 18 December 2013.
- ^ Pauley III, William H. (27 December 2013). "United States Disctrict Court Southern District of New York: American Civil Liberties Union v. James R. Clapper (13 Civ. 3994) (WHP))" (PDF). American Civil Liberties Union. Retrieved 28 December 2013.
- ^ Adam Liptak and Michael S. Schmidt (27 December 2013). "Judge Upholds N.S.A.'s Bulk Collection of Data on Calls". The New York Times. Retrieved 28 December 2013.
- ^ Denniston, Lyle (27 December 2013). "Judge upholds NSA's phone data sweeps (UPDATED)". Scotusblog. Retrieved 28 December 2013.
- ^ Peterson, Andrea (27 December 2013). "The most Kafkaesque paragraph from today's NSA ruling". The Washington Post. Retrieved 28 December 2013.
- ^ Horwitz, Sari (27 December 2013). "NSA collection of phone data is lawful, federal judge rules". The Washington Post. Retrieved 28 December 2013.
- ^ Ackermann, Spencer (2 January 2014). "ACLU will appeal ruling that NSA bulk phone record collection is legal". The Guardian. Retrieved 4 January 2014.
- ^ James Glanz and Andrew W. Lehren (20 December 2013). "N.S.A. Spied on Allies, Aid Groups and Businesses". The New York Times. Retrieved 28 December 2013.
- ^ a b Jacob Appelbaum, Judith Horchert and Christian Stöcker. "Catalog Reveals NSA Has Back Doors for Numerous Devices - Shopping for Spy Gear: Catalog Advertises NSA Toolbox". Der Spiegel. Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Jacob Appelbaum, Laura Poitras, Marcel Rosenbach, Christian Stöcker, Jörg Schindler and Holger Start. "Inside TAO: Documents Reveal Top NSA Hacking Unit - The NSA Uses Powerful Toolbox in Effort to Spy on Global Networks". Der Spiegel. Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ "Interactive Graphic: The NSA's Spy Catalog". Der Spiegel. 30 December 2013. Retrieved 4 January 2014.
- ^ Erik Kain (2013-12-29). "Report: NSA Intercepting Laptops Ordered Online, Installing Spyware". Retrieved 30 December 2013.
- ^ RAPHAEL SATTER (29 December 2013). "Report: NSA intercepts computer deliveries". Associated Press. Retrieved 30 December 2013.
- ^ Courtney Subramanian (Dec 29, 2013). "The TAO of the NSA: Specialized Hacking Team Gets the 'Ungettable'". Time (magazine). Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Glenn Greenwald: The NSA Can "Literally Watch Every Keystroke You Make"". Democracy Now!. Democracy Now!. 30 December 2013. Retrieved 4 January 2014.
- ^ Walters, Joanna (29 December 2013). "NSA 'hacking unit' infiltrates computers around the world – report". The Guardian. Retrieved 4 January 2014.
- ^ "GHOSTMACHINE: The NSA's cloud analytics platform". The Washington Post. Retrieved 28 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b Michael Winter (January 2, 2014). "NSA working to build computer to crack encryption". USA Today. Retrieved 3 January 2014.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c Steven Rich and Barton Gellman (3 January 2014). "NSA seeks to build quantum computer that could crack most types of encryption". The Washington Post. Retrieved 3 January 2014.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ "A description of the Penetrating Hard Targets project". The Washington Post. 2 January 2014. Retrieved 4 January 2014.
- ^ "Classifying NSA quantum computing efforts". The Washington Post. 2 January 2014. Retrieved 4 January 2014.
- ^ Lee, Timothy B. (2 January 2014). "Confused about the NSA's quantum computing project? This MIT computer scientist can explain". The Washington Post. Retrieved 4 January 2014.
- ^ Mike Dorning and Chris Strohm (Aug 23, 2013). "Court Finding of Domestic Spying Risks Obama Credibility". Bloomberg Television. Retrieved 28 December 2013.
- ^ Adam Serwer (08/07/13). "Obama says 'there is no spying on Americans,' but what about our data?". MSNBC. Retrieved 28 December 2013.
{{cite web}}: Check date values in:|date=(help) - ^ "Press Briefing by Press Secretary Jay Carney, 6/13/2013". White House. Retrieved 28 December 2013.
- ^ "Holder: Leaks damaged U.S. security". CNN. June 15, 2013. Retrieved 28 December 2013.
- ^ "Cameron says may act against press over spy leaks". Reuters. Oct 28, 2013. Retrieved 28 December 2013.
- ^ Janet Stobart (June 10, 2013). "Britain denies using PRISM to get around domestic spying laws". The Los Angeles Times. Retrieved 28 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ Rob Williams (10 October 2013). "Snowden leaks published by the Guardian were damaging to security, says Nick Clegg". The Independent. Retrieved 1 January 2014.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Abbott offers Australian spy assurance". The Australian. October 31, 2013. Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Germany's Merkel rejects NSA-Stasi comparison". Associated Press. Jul 10, 2013. Retrieved 28 December 2013.
- ^ "German Interior Minister Friedrich Discusses NSA Spying Affair". Der Spiegel. August 28, 2013. Retrieved 28 December 2013.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ "Carl Bildt defends FRA surveillance as 'necessary'". Sveriges Radio. Retrieved 28 December 2013.
- ^ "Germany probes secret service ties with US agencies". Agence France-Presse. Retrieved 28 December 2013.
- ^ William Boston (July 22, 2013). "Germany to Review Spy Service's Ties With NSA". The Wall Street Journal. Retrieved 28 December 2013.
{{cite news}}: Italic or bold markup not allowed in:|newspaper=(help) - ^ Mike Levine. "White House Picks Panel to Review NSA Programs". ABC News. Retrieved 28 December 2013.
- ^ Johnson, Luke. "James Clapper, Director of National Intelligence Who Misled Congress, To Establish Surveillance Review Group". Huffington Post. Retrieved August 13, 2013.
- ^ Nick Hopkins, Patrick Wintour, Rowena Mason and Matthew Taylor (17 October 2013). "Extent of spy agencies' surveillance to be investigated by parliamentary body". The Guardian. Retrieved 28 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help)CS1 maint: multiple names: authors list (link) - ^ Stewart Bell (December 9, 2013). "Review underway into allegations that national intelligence agency illegally spied on Canadians". National Post. Retrieved 30 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ a b c Ewen MacAskill and Dominic Rushe. "Snowden document reveals key role of companies in NSA data collection". The Guardian. Retrieved 22 December 2013.
{{cite web}}: Italic or bold markup not allowed in:|publisher=(help) - ^ "Collateral Murder, 5 Apr 2010". WikiLeaks. April 5, 2010. Retrieved 1 January 2014.
- ^ "Afghan War diary". WikiLeaks. July 25, 2010. Retrieved 1 January 2014.
- ^ "Iraq War logs". WikiLeaks. October 22, 2010. Retrieved 1 January 2014.
- ^ "Secret US Embassy Cables". WikiLeaks. November 28, 2010. Retrieved 1 January 2014.
- ^ "Gitmo Files". WikiLeaks. April 24, 2011. Retrieved 1 January 2014.
External links
![]() Media related to 2013 Mass Surveillance Disclosures at Wikimedia Commons
Media related to 2013 Mass Surveillance Disclosures at Wikimedia Commons
- "Global Surveillance. An annotated and categorized "overview of the revelations following the leaks by the whistleblower Edward Snowden. There are also some links to comments and followups". By Oslo University Library.
- "The NSA Files". The Guardian.
- Politico Staff. "NSA leaks cause flood of political problems." Politico. June 13, 2013.
- NSA inspector general report on email and internet data collection under Stellar Wind as provided by The Guardian on June 27, 2013.
- "Putin talks NSA, Syria, Iran, drones in exclusive RT interview (FULL VIDEO)." Russia Today. June 12, 2013.
- Ackerman, Spencer. "NSA warned to rein in surveillance as agency reveals even greater scope." The Guardian. July 17, 2013.
- Ackerman, Spencer. "Slew of court challenges threaten NSA's relationship with tech firms." The Guardian. Wednesday July 17, 2013.
- Ackerman, Spencer and Paul Lewis. "NSA amendment's narrow defeat spurs privacy advocates for surveillance fight." The Guardian. Thursday July 25, 2013.
- Ackerman, Spencer and Dan Roberts. "US embassy closures used to bolster case for NSA surveillance programs." The Guardian. Monday August 5, 2013.
- Two of the 'trips' (numbers 29 and 76) in the 2006 book, 'No Holiday', Cohen, Martin. No Holiday. New York: Disinformation Company Ltd. ISBN 978-1-932857-29-0.
{{cite book}}:|access-date=requires|url=(help) are investigating the NSA and its activities. - Greenwald, Glenn. "Members of Congress denied access to basic information about NSA." The Guardian. Sunday August 4, 2013.
- "Obama’s former adviser ridicules statement that NSA doesn’t spy on Americans." (Archive) Russia Today. August 9, 2013.
- MacAskill, Ewen. "Justice Department fails in bid to delay landmark case on NSA collection." The Guardian. Thursday July 25, 2013.
- Rushe, Dominic. "Microsoft pushes Eric Holder to lift block on public information sharing." The Guardian. Tuesday July 16, 2013.
- Perez, Evan. "Documents shed light on U.S. surveillance programs." (Archive) CNN. August 9, 2013.
- Gellman, Barton. "NSA broke privacy rules thousands of times per year, audit finds." Washington Post. Thursday August 15, 2013.
- Roberts, Dan and Robert Booth. "NSA defenders: embassy closures followed pre-9/11 levels of 'chatter'." The Guardian. Sunday August 4, 2013.
- Greenwald, Glenn. "The crux of the NSA story in one phrase: 'collect it all'." The Guardian. Monday July 15, 2013.
- Sanchez, Julian. "Five things Snowden leaks revealed about NSA’s original warrantless wiretaps." Ars Technica. July 9, 2013.
- Forero, Juan. "Paper reveals NSA ops in Latin America." Washington Post. July 9, 2013.
- Jabour, Bridie. "Telstra signed deal that would have allowed US spying." The Guardian. Friday July 12, 2013.
- Ackerman, Spencer. "White House stays silent on renewal of NSA data collection order." The Guardian. Thursday July 18, 2013.
- Naughton, John. "Edward Snowden's not the story. The fate of the internet is." The Guardian. July 28, 2013.
- Adams, Becket. "MAD MAGAZINE USES ICONIC CHARACTERS TO HIT OBAMA OVER GOV’T SURVEILLANCE." The Blaze. August 8, 2013.
- Howerton, Jason. "HERE IS THE PRO-NSA SURVEILLANCE ARGUMENT." The Blaze. June 10, 2013.
- "Edward Snowden NSA files: secret surveillance and our revelations so far – Leaked National Security Agency documents have led to several hundred Guardian stories on electronic privacy and the state" by the Guardian's James Ball on August 21, 2013
- 2013-07-29 Letter of FISA Court president Reggie B. Walton to the Chairman of the U.S. Senate Judiciary Committee Patrick J. Leahy about certain operations of the FISA Court; among other things the process of accepting, modifying and/or rejecting surveillance measures proposed by the U.S. government, the interaction between the FISA Court and the U.S. government, the appearance of non-governmental parties before the court and the process used by the Court to consider and resolve any instances where the government entities notifies the court of compliance concerns with any of the FISA authorities.
- "The Spy Files". Wikileaks. December 1, 2011. A collection of documents relating to surveillance.
- "The Spy Files". Wikileaks. December 8, 2011. Part 2 of the above.
- "Spy Files 3". Wikileaks. September 4, 2013. Part 3 of the above.
- "Veja os documentos ultrassecretos que comprovam espionagem a Dilma" (in Portuguese). September 2, 2013. Retrieved September 4, 2013. Documents relating to the surveillance against Dilma Roussef and Enrique Peña Nieto
- NSA surveillance: A guide to staying secure - The NSA has huge capabilities – and if it wants in to your computer, it's in. With that in mind, here are five ways to stay safe by The Guardian's Bruce Schneier on September 5, 2013.
- 2014-01-04 Al Jazeera's "Listening Post - The Snowden saga: Spies, secrets and security - A look back at the biggest media story of 2013 - Edward Snowden and the NSA surveillance programme." which in its first part of the broadcast retells the global surveillance in the year 2013 and in its second part shows an interview former NSA general counsel Stewart Baker.